Explain why encryption is used in the second message (from Bob to Alice) in Figure 31.23, but
Question:
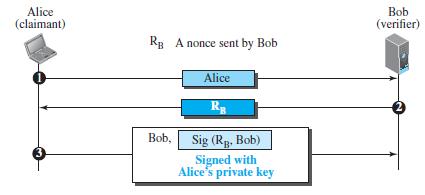
Explain why encryption is used in the second message (from Bob to Alice) in Figure 31.23, but signing is done in the third message (from Alice to Bob) in Figure 31.24.
Figure 31.23
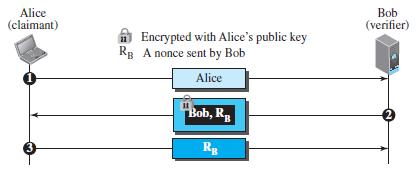
Figure 31.24
Transcribed Image Text:
Alice (claimant) Bob (verifier) A Encrypted with Alice's public key Rg A nonce sent by Bob Alice Bob, R 3 Rg
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (12 reviews)
In Figure 3123 Bob encrypts the message with Alices public key encryption should ...View the full answer

Answered By

Pushpinder Singh
Currently, I am PhD scholar with Indian Statistical problem, working in applied statistics and real life data problems. I have done several projects in Statistics especially Time Series data analysis, Regression Techniques.
I am Master in Statistics from Indian Institute of Technology, Kanpur.
I have been teaching students for various University entrance exams and passing grades in Graduation and Post-Graduation.I have expertise in solving problems in Statistics for more than 2 years now.I am a subject expert in Statistics with Assignmentpedia.com.
4.40+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Explain why we may need a router in Figure 9.16. Bob Alice R Alice's site Bob's site
-
Suppose Alice wants to communicate with Bob using symmetric key cryptography using a session key KS. In Section 8.2, we learned how public-key cryptography can be used to distribute the session key...
-
Change Figure 31.23 to allow bidirectional authentication. Alice needs to be authenticated for Bob and Bob for Alice.
-
A double-ended queue or deque (pronounced "deck") is a collection that is a combination of a stack and a queue. Write a class Deque that uses a linked list to implement the following API: public...
-
Critically assess the similarities and differences between the marketing communications mix elements when it comes to influence on society.
-
Chris Co. purchased a piece of equipment and incurred the following costs. Which of these costs is properly capitalized and recorded as part of the cost of the equipment? I. Freight charges to...
-
For each of the following notes receivable, compute the amount of interest revenue earned during 2010. Use a 360-day year, and round to the nearest dollar. Note 1 Note 2 Note 3 Note Principal...
-
Donald Tweedt started a company to produce and distribute natural fertilizers. Donalds company sells two fertilizers that are wildly popular: green fertilizer and compost fertilizer. Green...
-
(39) Compute the standard deviation (or dispersion) , in the scalar velocities around the mean for neon atoms at 298K. (Molar mass of Ne: 20.2 g/mol.) (40) Obtain the expression for <16>1/3 within...
-
The CFO for the Shelton Corporation has $1.2 million to allocate to the following budget requests from 5 departments: Because the total budget requests exceed the available $1.2 million, not all the...
-
If Alice and Bob need to communicate using asymmetric-key cryptography, how many keys do they need? Who needs to create these keys?
-
If the one-time pad cipher (Figure 31.12 in the text) is the simplest and most secure cipher, why is it not used all of the time? Figure 31.12 Random sequence bit generator Secure key-exchange...
-
Explain why only government purchases of goods and services, not transfers, are a component of aggregate demand.
-
What is recoverable amount?
-
The following data relates to Fay Ltd, a company that buys and sells only one product: 1. Calculate the cost of ending inventory and the COGS, assuming: a. A perpetual system using the LIFO cost flow...
-
Which cost flow assumption do you believe gives the most appropriate asset figure in times of rising prices?
-
Reconcile Henry's month-end bank account balance and, based on your analysis, indicate what corrections you would make to Henry's records: 1. Month-end bank balance according to the bank's statement,...
-
Gibbs Ltd operates a manufacturing facility to produce its key products. On 1 July 2016, the balance of an equipment account was as follows: During the 2017 financial year, Gibbs Ltd incurred the...
-
a. What does CS mean? (Do not just spell out the abbreviation.) 19a.) In CS MA/CA, CS means __________. a. Cancel sending b. Counter-source c. Carriage suspension d. Carrier sense b. How is carrier...
-
This problem continues the Draper Consulting, Inc., situation from Problem 12-45 of Chapter 12. In October, Draper has the following transactions related to its common shares: Oct 1 Draper...
-
A complex view can contain which of the following? a. Data from one or more tables b. An expression c. A GROUP BY clause for data retrieved from one table d. Five columns from one table e. All of the...
-
What does FIND-MAXIMUM-SUBARRAY return when all elements of A are negative?
-
Write pseudocode for the brute-force method of solving the maximum-subarray problem. Your procedure should run in (n 2 ) time.
-
Presented below are the comparative income and retained earnings statements for Sunland Inc. for the years 2025 and 2026. 2026 2025 Sales $374,000 $268,000 Cost of sales 213,000 128,000 Gross profit...
-
What are the financial and operational implications of leverage buyouts and private equity takeovers on target companies, including capital structure and governance changes ?
-
How do environmental, social, and governance (ESG) criteria influence investment strategies, and what is their impact on portfolio diversification and risk-adjusted returns?

Study smarter with the SolutionInn App


