Write and test a program that simulates the byte stuffing and byte unstuffing as shown in Figure
Question:
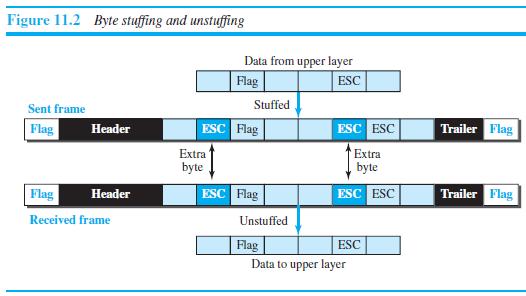
Write and test a program that simulates the byte stuffing and byte unstuffing as shown in Figure 11.2.
Transcribed Image Text:
Figure 11.2 Byte stuffing and unstuffing Data from upper layer Flag ESC Sent frame Stuffed Flag ESC Flag ESC ESC Trailer Flag Header Extra Extra byte byte Flag ESC Flag ESC ESC Trailer Flag Header Received frame Unstuffed Flag Data to upper layer ESC
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (4 reviews)
The first programs show how we can do bytestuffing in a byteoriented protocol The us...View the full answer

Answered By

Sigei Kipngeno
I am a professional writer with more than 2 years of writing experience. I will always deliver a grade A paper with zero plagiarism . Thanks in advance.
4.70+
175+ Reviews
311+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Write and test a program that simulates the bit stuffing and bit unstuffing as shown in Figure 11.4. Figure 11.4 Bit stuffing and unstuffing Data from upper layer 0001111111001111101000 Stuffed Frame...
-
Magic 8 Ball is a toy developed in the 1950s and used for fortune-telling or advice-seeking. A player asks or thinks of a yes-or-no question such as, Will I be rich someday? The player then turns the...
-
Write a program that displays a bean machine introduced in Exercise, as shown in Figure. The bean machine, also known as a quincunx or the Galton box, is a device for statistics experiments named...
-
A. What is Alpha One's NOPAT? Why does NOPAT differ from the earnings after taxes? B. Estimate the effective before-tax cost of the long-term debt. c. Estimate the effective after-tax cost of the...
-
Tammy teaches elementary school history for the Metro School District. In 2016 she has incurred the following expenses associated with her job: Noncredit correspondence course on history...
-
Why is it helpful to divide the funding needs of a seasonal business into its permanent and seasonal funding requirements when developing a funding strategy?
-
The following sale related transactions for PDR, Inc., occurred during the month of June. Requirement 1. Journalize the transactions for PDR, Inc. Omit explanations. Jun 3 Sold $3,200 (cost $2,100)...
-
C. N. Itall has been a systems analyst for Tun-L-Vision Corporation for many years. When you came on board as part of the systems analysis team and suggested prototyping as part of the SDLC for a...
-
Can you help create an outline for my economics? I chose to create a presentation on the economics of concert tickets. I want to highlight how Ticketmaster/Live Nation is a Monopoly and how their...
-
Refer to Simon Company's balance sheets in Exercise 13-6. Simon Company's year-end balance sheets follow. Express the balance sheets in common-size percents. Round amounts to the nearest one-tenth of...
-
What is multipath propagation? What is its effect on wireless networks?
-
In a BSS with no AP (ad hoc network), we have five stations: A, B, C, D, and E. Station A needs to send a message to station B. Answer the following questions for the situation where the network is...
-
Sketch the region under the graph of the function and find its area using FTC I. f(x) = cos x, [0, 1]
-
2:21. Activity 4 EVAL... Activity: Module 3 Lesson 2 Group yourselves into 5 members per group. Each group will choose/identify one multimodal text (print advertisement) and insert the photo in your...
-
In 2008, economist Eleni Gabre-Mahin established the Ethiopian Commodity Exchange (ECX) with the exclusive right to trade coffee. The Exchange mixed the raw beans from different sources before...
-
The Marine Division of Pacific Corporation has average invested assets of $120,000,000. Sales revenue of $50,270,000 results in net operating income of $9,974,000. The hurdle rate is 5%. Required a....
-
The "fraud triangle" has been used to identify conditions or circumstances that typically present in frauds. It consists of three components, which together may lead to fraudulent behavior: (1)...
-
A chart showing the Average Cost (AC) of cell phones as a function of the quantity (Q) of Cell Phones sold. The mathematical function can be written as: AC = F(Q). Using the chart, what is the lowest...
-
Air with a specific weight of 12.5 N/m 3 and a dynamic viscosity of 2.0 Ã 10 -5 Pas flows through the shaded portion of the duct shown in Fig. 9.16 at the rate of 150 m 3 /h. Calculate the...
-
The Alert Company is a closely held investment-services group that has been very successful over the past five years, consistently providing most members of the top management group with 50% bonuses....
-
Is the frequency domain plot of an alarm system discrete or continuous?
-
What is the bandwidth of the composite signal shown in Figure 3.37? Frequency 180 5 5 5 5
-
What is the frequency of the signal in Figure 3.36? 4 ms Time
-
Gary notices that his production department requires information from the sales division: in turn, the production budget is sent on to other departments. He sees how the budget pieces fit together...
-
On January 1 , Year 1 , Cakes ' N ' Bakes Co . purchased $ 3 0 , 0 0 0 of equipment. The equipment has a salvage value of $ 2 , 0 0 0 and an estimated useful life of 1 0 years. The company uses the...
-
On November 1 , 2 0 2 2 , Gordon Company collected $ 6 , 3 0 0 in cash from its tenant as an advance rent payment on its store location. The six - month lease period ends on April 3 0 , 2 0 2 3 , at...

Study smarter with the SolutionInn App


