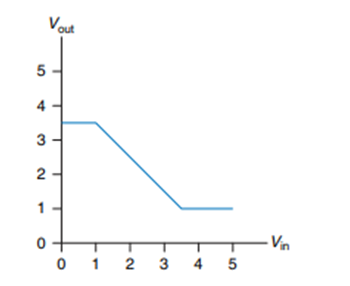
Repeat Exercise 1.78 for the transfer characteristics shown in Figure 1.45. Voue 2 - Vn 4
Question:
Repeat Exercise 1.78 for the transfer characteristics shown in Figure 1.45.
Transcribed Image Text:
Voue 2 - Vn т 4 3. 4. 3.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 80% (5 reviews)
No there is no legal set of logi...View the full answer

Answered By

Utsab mitra
I have the expertise to deliver these subjects to college and higher-level students. The services would involve only solving assignments, homework help, and others.
I have experience in delivering these subjects for the last 6 years on a freelancing basis in different companies around the globe. I am CMA certified and CGMA UK. I have professional experience of 18 years in the industry involved in the manufacturing company and IT implementation experience of over 12 years.
I have delivered this help to students effortlessly, which is essential to give the students a good grade in their studies.
3.50+
2+ Reviews
10+ Question Solved
Related Book For 

Digital Design and Computer Architecture
ISBN: 978-0123944245
2nd edition
Authors: David Harris, Sarah Harris
Question Posted:
Students also viewed these Computer science questions
-
Is it possible to assign logic levels so that a device with the transfer characteristics shown in Figure 1.44 would serve as an inverter? If so, what are the input and output low and high levels (V...
-
Is it possible to assign logic levels so that a device with the transfer characteristics shown in Figure 1.46 would serve as a buffer? If so, what are the input and output low and high levels (V IL...
-
Ben Bitdiddle has invented a circuit with the transfer characteristics shown in Figure 1.47 that he would like to use as a buffer. Will it work? Why or why not? He would like to advertise that it is...
-
Use the present value tables in Appendix A and Appendix B to compute the NPV of each of the following cash inflows. a. $89,000 received at the end of six years. The discount rate is 4 percent. b....
-
A bond with a face value of $10,000 is issued at a discount of $800 on January 1, 2012. The face rate of interest on the bond is 7%. Required 1. Was the market rate at the time of issuance greater...
-
Home equity, student, and auto loans are special-purpose consumer loans. Which ones offer the unique benefit of tax deductibility for interest paid?
-
The following transactions occurred during April 2010, for Angelos Garden Center, Inc.: Requirement 1. Journalize the April transactions for Angelos Garden Center, Inc. Omit explanations. Apr 3...
-
Linda loves buying shoes and going out to dance. Her utility function for pairs of shoes, S, and the number of times she goes dancing per month, T, is U(S, T) = 2ST, so MUS = 2T and MUT = 2S. It...
-
A communications system uses unipolar NRZ signals to transmit '1' and '0' bits: s 1 (t) = A, 0 < t < T, for a '1' bit and s 0 (t) = 0, 0 < t < T, for a '0' bit. The received signal is the transmitted...
-
a. Design the network of Fig. 2.182 to maintain VL at 12V for a load variation (IL) from 0 mA to 200 mA. That is, determine RS and VZ. b. Determine PZmax, for the Zener diode of part (a). 16 V
-
How many different truth tables exist for Boolean functions of N variables?
-
In this problem, you will explore the design of a 32-bit prefix adder. (a) Sketch a schematic of your design. (b) Design the 32-bit prefix adder in an HDL. Simulate and test your adder to prove that...
-
Analysis takes place from a _________ perspective and design takes place from a _________ perspective. (a) User and Developer (b) Developer and User (c) User and Designer (d) Designer and Developer
-
How does a financial defalcation differ from fraudulent financial reporting? Explain. Do the auditors responsibilities differ for detecting these two types of client fraud?
-
Describe how the objectives approach to evaluating the adequacy of controls in an accounting application is implemented.
-
Residual audit risk is most closely related to the concept of: a. Control risk b. Audit risk c. Detection risk d. Inherent risk
-
What is the difference between a standard external audit report on internal control and the newly designed SysTrust report on computer controls? Why is this difference important?
-
Why are the SEC and other regulatory agencies pushing for more external reporting on a companys internal controls?
-
In international lending, what is meant by the phrase rescheduling of sovereign loans? Why has rescheduling of loans become a problem to international lenders? What countries are involved?
-
After Theorem 1.5 we note that multiplying a row by 0 is not allowed because that could change a solution set. Give an example of a system with solution set S0 where after multiplying a row by 0 the...
-
Show that n i=1 i/2 i < 2.
-
Show that log b f (n) is (log f (n)) if b > 1 is a constant.
-
In Section 5.2 we prove by induction that the number of lines printed by a call to drawInterval(c) is 2 c 1. Another interesting question is how many dashes are printed during that process. Prove by...
-
Charles was a jewellery designer and placed the following advertisement in West Noon Post on 1 November 2021. For Sale Handmade "88-shaped" necklace on display HK$10,000 Come to my shop and buy it...
-
ASSESSMENT 1 BRIEF Objective of the task The purpose of this task is to demonstrate your knowledge of how to use commercial kitchen equipment to prepare a range of different food types with very...
-
A man drops a rock into a well. (a) The man hears the sound of the splash 2.23 s after he releases the rock from rest. The speed of sound in air (at the ambient temperature) is 336 m/s. How far below...

Study smarter with the SolutionInn App