An old MST method, called Baruvka?s algorithm, works as follows on a graph G having n vertices
Question:
An old MST method, called Baruvka?s algorithm, works as follows on a graph G having n vertices and m edges with distinct weights:
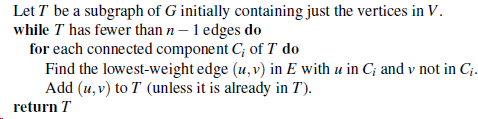
Prove that this algorithm is correct and that it runs in O(mlogn) time.
Transcribed Image Text:
Let T be a subgraph of G initially containing just the vertices in V. while T has fewer than n – 1 edges do for each connected component C; of T do Find the lowest-weight edge (u,v) in E with u in C; and v not in ;. Add (u, v) to T (unless it is already in T). return T
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 81% (11 reviews)
Baruvkas algorithm is a minimum spanning tree MST algorithm that works by constructing the tree one ...View the full answer

Answered By

Dulal Roy
As a tutor, I have gained extensive hands-on experience working with students one-on-one and in small group settings. I have developed the ability to effectively assess my students' strengths and weaknesses, and to customize my teaching approach to meet their individual needs.
I am proficient at breaking down complex concepts into simpler, more digestible pieces, and at using a variety of teaching methods (such as visual aids, examples, and interactive exercises) to engage my students and help them understand and retain the material.
I have also gained a lot of experience in providing feedback and guidance to my students, helping them to develop their problem-solving skills and to become more independent learners. Overall, my hands-on experience as a tutor has given me a deep understanding of how to effectively support and encourage students in their learning journey.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Question Posted:
Students also viewed these Computer science questions
-
Suppose we represent a graph G having n vertices and m edges with the edge list structure. Why, in this case, does the insertVertex method run in O(1) time while the removeVertex method runs in O(m)...
-
Let G be an undirected graph with n vertices and m edges. Describe an O(n+m)-time algorithm for traversing each edge of G exactly once in each direction.
-
An Euler tour of a directed graph G with n vertices and m edges is a cycle that traverses each edge of G exactly once according to its direction. Such a tour always exists if G is connected and the...
-
Show that the angular wave number k for a non-relativistic free particle of mass m can be written as in which K is the particle's kineticenergy 27 V2mK k =
-
Wong Computer Games Inc. (WCG) was incorporated in the state of Illinois in the last decade. The founding shareholder, Mr. Andrew Wong, is an inventor of computer simulation models. His products...
-
Provide correct journal entries for these The following information relates to the debt investments of Concord Inc. during a recent year: 1 . On February 1 , the company purchased Gibbons Corp. 1 0 %...
-
New automobiles are often equipped with artificial intelligence capabilities that support the driver up to the point of allowing fully autonomous operations. The inspection process of these vehicles...
-
Root Company produces uniforms. The company allocates manufacturing overhead based on the machine hours each job uses. Root Company reports the following cost data for 2008: Requirements 1. Compute...
-
Agarwal, Bergeron, and Cishek have been in partnership for a number of years. The partners allocate all profits and losses on a 4 : 2 : 2 basis, respectively. Recently, each partner has become...
-
Analysis of famous case study - Godiva Chocolatier and Godiva Gems This paper answers the following questions on the case study - 1) Define the product offered by Godiva. Identify the different...
-
Our implementation of shortestPathLengths in Code Fragment 14.13 relies on use of ?infinity? as a numeric value, to represent the distance bound for vertices that are not (yet) known to be reachable...
-
Use an adjacencymatrix to implement a class supporting a simplified graph ADT that does not include update methods. Your class should include a constructor method that takes two collectionsa...
-
Give initial guesses for the geometry (bond lengths, bond angles, and dihedral angles) of the likely conformers of each of the following ground-state molecules. (a) CH3OH; (b) C2H4; (c) CH3NH2; (d)...
-
A bare module cost is needed for a stainless steel clad distillation column (pressure vessel) with a diameter of 10 feet and a height of 45 feet. The operating pressure is 12 barg. Determine the...
-
The Fire Safety Check sheet can be of use to develop or evaluate a fire safety management policy. Go through the checklist while you reflect on your current or previous company, and discuss the...
-
Stealth bank has deposits of $700 million. It holds reserves of $20 million and has purchased government bonds worth $350 million. The banks loans, if sold at current market value, would be worth...
-
Brunswick Sdn. Bhd. (Brunswick) has just started its business in the beginning of Year 2019. Brunswick manufactures and sells a single product, barrel. The income statement for Brunswick presented...
-
How do financial institutions employ complex derivatives such as interest rate swaps and credit default swaps to manage their exposure to interest rate and credit risk, and what are the associated...
-
What are the four goals of effective metrics? In your own words explain your understanding of the metric and where and how it can be beneficial.
-
Refer to Exercise 8.S.I. Construct a scatterplot of the data. Does the appearance of the scatterplot indicate that the pairing was effective? Explain. Exercise 8.S.I. A volunteer working at an animal...
-
Define the following terms in the context of SNMP: managing server, managed device, network management agent and MIB.
-
Suppose ASs X and Z are not directly connected but instead are connected by AS Y. Further suppose that X has a peering agreement with Y, and that Y has a peering agreement with Z. Finally, suppose...
-
What two types of ICMP messages are received at the sending host executing the Trace route program?
-
Quad Enterprises is considering a new 3 - year expansion project that requires an initial fixed asset investment of $ 2 . 8 million. The fixed asset falls into the 3 - year MACRS class ( MACRS Table...
-
payout of $1,215? % (Round to two decimal places.) Which is the best investment choice? (Select the best response.) O Investment one O Investment two O Investment three
-
the four key quantitative metrics used in the assessment of financial resilience and performance of investment projects by a firm

Study smarter with the SolutionInn App