Use the formula for the vector potential of the quantized radiation field to derive the radiation Hamiltonian:
Question:
Use the formula for the vector potential of the quantized radiation field to derive the radiation Hamiltonian:
to derive the radiation Hamiltonian: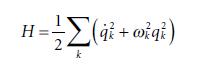 See Section for an outline of the necessary steps.
See Section for an outline of the necessary steps.
Transcribed Image Text:
1 A(r,t)=, - Νεον k qu(t)ük(r)
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 87% (8 reviews)
HUEUB Step 7 Substitute the expressions for UE and UB from Step 4 into the radiation ...View the full answer

Answered By

Surendar Kumaradevan
I have worked with both teachers and students to offer specialized help with everything from grammar and vocabulary to challenging problem-solving in a range of academic disciplines. For each student's specific needs, I can offer explanations, examples, and practice tasks that will help them better understand complex ideas and develop their skills.
I employ a range of techniques and resources in my engaged, interesting tutoring sessions to keep students motivated and on task. I have the tools necessary to offer students the support and direction they require in order to achieve, whether they need assistance with their homework, test preparation, or simply want to hone their skills in a particular subject area.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Sciences questions
-
Use the formula for the joint density of Y1 and Yn shown in Exercise 8.52 and the transformation technique of Section 7.4 to find an expression for the joint density of Y1 and the sample range R = Yn...
-
Use the formula for the sampling distribution of 8 X on page 253 to show that for random samples of size n = 3 the median is an unbiased estimator of the parameter of a uniform population with = ...
-
Use the formula for computing SSE to verity that r2 = 1 - SSE / SST?
-
Poppins Company has the following: If 9,000 units are on hand at December 31, the cost of the ending inventory under FIFO is: (a) $99,000. (b) $108,000. (c) $113,000. (d) $117,000. Inventory, Jan. 1...
-
The piston in a master cylinder has a radius of 0.570 in. and the radius of each of the two brake cylinder pistons is 1.75 in. (a) How much pressure is created in the master cylinder if a driver...
-
Two products X and Y are made using similar equipment and methods. The data for last period are Calculate the overheads to be absorbed per unit of each product based on: a. Conventional absorption...
-
\((90-101)^{3}\) Perform the indicated calculation.
-
Everett Co. was organized on July 1, 2015. Quarterly financial statements are prepared. The unadjusted and adjusted trial balances as of September 30 are shown below. Instructions (a) Journalize the...
-
(1) Performing any bookkeeping services always impairs the independence of: (a) A CPA who audits the financial statements of a publicly held company. (b) A CPA who audits the financial statements o...
-
The work function of Cs is 2.14 eV. Find the maximum kinetic energy of electrons ejected by light of wavelength 400 nm.
-
Show that the classical Hamiltonian in Equation 2.54 is consistent with the Lorentz force To proceed, calculate the force in the x direction, F x = mx, the help of the following expressions from...
-
Explain whether the following situations, taken independently, would be favorable or unfavorable: (a) Increase in gross profit percentage, (b) Decrease in inventory turnover ratio , (c) Increase in...
-
Briefly explain the contribution of the following areas to information systems auditing: a. Traditional auditing b. Information systems management c. Behavioral science d. Computer science
-
Loss of which of the following files is likely to have the most serious consequences for a manufacturing organization: a. Inventory file b. Material requirements planning file c. Job routing file d....
-
Computer abuse is best defined as: a. Malicious damage carried out to hardware and software b. Any incident associated with computer technology whereby a victim suffered loss and a perpetrator gained...
-
Incorrect data in a computer system is likely to have more serious consequences for a(an): a. Strategic planning system b. Expert system c. Personal decision support system d. Management control...
-
Relative to general fraud and embezzlement, computer fraud and embezzlement seems to be: a. Unaffected by deterrent administrative controls b. Smaller in size c. Larger in size d. Easier to prosecute...
-
Figure 13.12 shows what happens if the AE curve shifts out temporarily and the central bank raises the real interest rate. Now suppose the same shock occurs but the central bank keeps the interest...
-
The activities listed in lines 2125 serve primarily as examples of A) Underappreciated dangers B) Intolerable risks C) Medical priorities D) Policy failures
-
Propose a structure for a compound with molecular formula C 4 H 8 O that exhibits the following 13 C NMR and FTIR spectra. Carbon NMR 67.7- 25.4- 80 30 20 100 90 70 60 40 10 Chemical shift (ppm) 100...
-
Propose a structure for a compound with molecular formula C 4 H 10 O that exhibits the following 1 H NMR spectrum. Proton NMR 2 3.0 4.0 2.5 Chemical shift (ppm) 2.0 3.5 1.5 1.0
-
Predict the product of the following reaction. M 1) LIAID, 2) H20 Me
-
The company is considering paying the retail coordinator an incentive commission of $0.10 per pair of earrings. This will be on top of the salespeople's commission and there will be no change in...
-
. TB MC Qu. 16-86 Carmen Company has an asset that cost... Carmen Company has an asset that cost $11,000 and currently has accumulated depreciation of $7,000. Suppose the firm sold the asset for...
-
(LO3) In 2012, Carow sold 3,000 units at $500 each. Variable expenses were $250 per unit, and fixed expenses were $250,000. The same selling price is expected for 2013. Carow is tentatively planning...

Study smarter with the SolutionInn App