There is a mknod system call in Fig. 1-16 but there is no rmnod call. Does this
Question:
There is a mknod system call in Fig. 1-16 but there is no rmnod call. Does this mean that you have to be very, very careful about making nodes this way because there is no way to every remove them?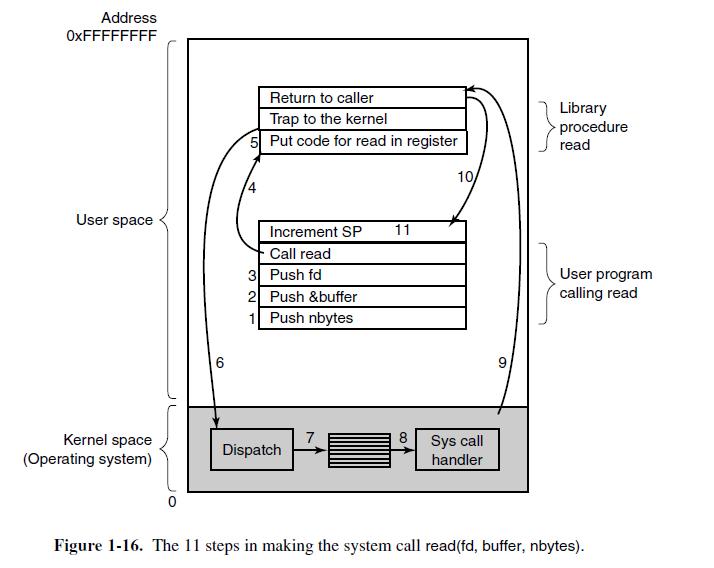
Transcribed Image Text:
Address OxFFFFFFFF User space Kernel space (Operating system) 6 Return to caller Trap to the kernel 5 Put code for read in register Increment SP 11 - Call read 3 Push fd 2 1 Push &buffer Push nbytes Dispatch 7 8 10/ Sys call handler 6 Library procedure read User program calling read Figure 1-16. The 11 steps in making the system call read(fd, buffer, nbytes).
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 40% (5 reviews)
Yes it is true that you have to be very careful about making nodes with the mknod system call becaus...View the full answer

Answered By

Antony Sang
I am a research and academic writer whose work is outstanding. I always have my customer's interests at heart. Time is an important factor in our day to day life so I am always time conscious. Plagiarism has never been my thing whatsoever. I give best Research Papers, Computer science and IT papers, Lab reports, Law, programming, Term papers, English and literature, History, Math, Accounting, Business Studies, Finance, Economics, Business Management, Chemistry, Biology, Physics, Anthropology, Sociology, Psychology, Nutrition, Creative Writing, Health Care, Nursing, and Articles.
5.00+
2+ Reviews
10+ Question Solved
Related Book For 

Operating Systems Design And Implementation
ISBN: 9780131429383
3rd Edition
Authors: Andrew Tanenbaum, Albert Woodhull
Question Posted:
Students also viewed these Computer science questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
John Peters had just arrived at the Memphis branch offices of Bull Steins (BS) brokerage firm. BS is one of the top 50 firms in the industry with a wide range of financial products. Five years prior,...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
In Canada, Canadian teachers and bosses and HIGH AUTHORITY FIGURES are not FEARED but RESPECTED. In CANADA TEACHERS, bosses and AUTHORITY FIGURES encourage feedback, OPINIONS and ENGAGE in discuss....
-
The notes to the Helping Charities financial statements reported the following data on December 31, Year 1 (end of the fiscal year): Helping Charities amortizes bonds by the effective-interest method...
-
An electronic device is cooled by passing air at 27?C through six small tubular passages in parallel drilled through the bottom of the device as shown below. The mass flow rate per tube is 7 x 10??5...
-
What are the advantages of using a safe deposit box to store your personal financial documents?
-
Perdon Corporation manufactures safes'large mobile safes, and large walkin stationary bank safes. As part of its annual budgeting process, Perdon is analyzing the profitability of its two products....
-
A stock has an expected return (?) of 17% per annum and a standard deviation (volatility, ?) of 37% per annum. Under the probability distribution assumptions of the BSM model: A) Compute the me...
-
Suppose that a computer can execute 1 billion instructions/sec and that a system call takes 1000 instructions, including the trap and all the context switching. How many system calls can the computer...
-
Why is the chroot system call limited to the superuser?
-
In Problem perform the indicated operations and simplify. (x - y) 3
-
Romeo (79.0 kg) entertains Juliet (47.0 kg) by playing his guitar from the rear of their boat at rest in still water, 2.70 m away from Juliet, who is in the front of the boat. After the serenade,...
-
The Gilster Company, a machine tooling firm, has several plants. One plant, located in St. Cloud, Minnesota, uses a job order costing system for its batch production processes. The St. Cloud plant...
-
How do you record the readings from a sampling process? Record readings according to organizational requirements, using expert support and advice as required
-
If possible, rewrite the equation in slope-intercept form, y = b+mx, and give the values of b and of m. 5(x+y)=4 NOTE: If it is not possible, indicate that using the check box. Enter exact answers....
-
What is the market value of equity?
-
Marshall Corporation purchased equipment and in exchange signed a three- year promissory note. The note requires Marshall to make equal annual payments of $ 20,000 at the end of each of the next...
-
Listed below are common types of current liabilities, contingencies, and commitments: a. Accounts payable b. Bank loans and commercial paper c. Notes payable d. Dividends payable e. Sales and excise...
-
Show how to implement the stack ADT using only a priority queue and one additional integer instance variable.
-
Hillary claims that a postorder traversal of a heap will list its keys in nonincreasing order. Draw an example of a heap that proves her wrong.
-
Bill claims that a preorder traversal of a heap will list its keys in nondecreasing order. Draw an example of a heap that proves him wrong.
-
In Carr's book The Shallow, does the author mention any social media issues? can you show me which chapter and some example passages in the book if yes
-
APPENDIX D TRIGONOMETRY A33 56. tan x + tan y sin(x + y) COS X Cos y position, as in the figure. Express x and y in terms of 0 and then use the distance formula to compute c.] 57, sin 30+ sin 0 = 2...
-
[x-3 forx

Study smarter with the SolutionInn App