Write code for a bounded buffer using the protected object mechanism of Ada 95.
Question:
Write code for a bounded buffer using the protected object mechanism of Ada 95.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 71% (7 reviews)

Answered By

Marvine Ekina
Marvine Ekina
Dedicated and experienced Academic Tutor with a proven track record for helping students to improve their academic performance. Adept at evaluating students and creating learning plans based on their strengths and weaknesses. Bringing forth a devotion to education and helping others to achieve their academic and life goals.
PERSONAL INFORMATION
Address: , ,
Nationality:
Driving License:
Hobbies: reading
SKILLS
????? Problem Solving Skills
????? Predictive Modeling
????? Customer Service Skills
????? Creative Problem Solving Skills
????? Strong Analytical Skills
????? Project Management Skills
????? Multitasking Skills
????? Leadership Skills
????? Curriculum Development
????? Excellent Communication Skills
????? SAT Prep
????? Knowledge of Educational Philosophies
????? Informal and Formal Assessments
0.00
0 Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Using Figure 17.12 as a guide, write a mechanism for the BaeyerVilliger oxidation of cyclohexyl methyl ketone by peroxybenzoic acid.
-
Using Figure 17.12 as a guide, write a mechanism for the Baeyer-Villiger oxidation of cyclohexyl methyl ketone by peroxybenzoic acid.
-
Write out a mechanism for every reaction depicted in Problem 38. (a) (b) (c) O .LiAID 2. H, H,O CH3CH O 1.LIAIH 2D D.O LiAID CH,CH>
-
What is the significance of communication between managers and their subordinates, and how does it impact employee performance?
-
Reconsider Prob. 8-109. Using EES (or other) software, investigate the effect of the state of the steam at the inlet of the feedwater heater on the ratio of mass flow rates and the reversible power....
-
A ray of light strikes a flat 2.00-cm-thick block of glass (n = 1.50) at an angle of 30.0 with the normal (Figure). Trace the light beam through the glass, and find the angles of incidence and...
-
\(\pi\) Identify each number as a natural number, an integer, a rational number, or a real number.
-
Thakin Industries Inc. manufactures dorm furniture in separate processes. In each process, materials are entered at the beginning, and conversion costs are incurred uniformly. Production and cost...
-
Assignment P 13.6 Thank you. Assignment Problem Thirteen - 6 (Comprehensive Corporate Tax Payable With CCA) Oland Led. is a Canadian controlled private corporation with a December 31 year end. For...
-
A company sells precision grinding machines to four customers in four different countries. It has just signed a contract to sell, two months from now, a batch of these machines to each customer. The...
-
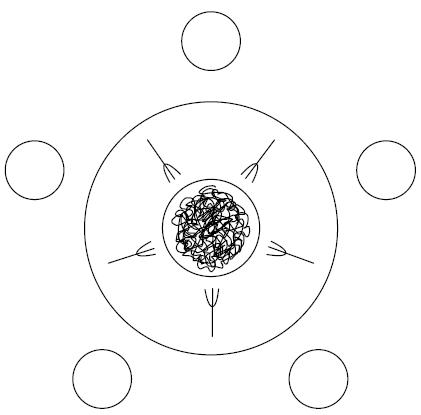
Repeat the previous exercise in Java using synchronized statements or methods. Try to make your solution as simple and conceptually clear as possible. You will probably want to use notify All.
-
Show how general semaphores can be implemented with conditional critical regions in which all threads wait for the same condition, thereby avoiding the overhead of unproductive wake-ups.
-
Wiater Company operates a small manufacturing facility. On January 1, 2017, an asset account for the company showed the following balances: Manufacturing...
-
The X hotel desires to earn after-tax income of $150,000 in 2021. Its average daily rate (ADR) is $70, and its variable costs per room sold equal $40. Its annual fixed costs total $160,000, and its...
-
Write a Javascript program to display the list of Student names whose name starts with 'A' For example, you have an array of students names Khadija Ali ahmed List of name starts with alphabet 'A' or...
-
Discuss the effect of fiscal policy on inflation. Discuss the effect of persistent fiscal stimulus on the economy in the long run. Describe the mechanism of how changes in fiscal policy affect output...
-
A neon sign includes a long neon-filled glass tube with electrodes at each end across which an electric field of 20,000 N/C. is placed. This large field accelerates free electrons which collide with...
-
Describe three different nationally accepted quality measures and benchmarks in your chosen practice setting. Explain the significance of these measures and benchmarks. Identify appropriate...
-
When Marcel Henry took over as leader of a new product development team, he was both excited and apprehensive. "I wonder," he said to himself on the first day in his new assignment, "if I can meet...
-
The cash records of Holly Company show the following four situations. 1. The June 30 bank reconciliation indicated that deposits in transit total $720. During July, the general ledger account Cash...
-
Assume PPP is in the authentication phase, show payload exchanged between the nodes if PPP is using a. PAP b. CHAP
-
Define piggybacking and its benefit.
-
Assume the only computer in the residence uses PPP to communicate with the ISP. If the user sends 10 network-layer packets to ISP, how many frames are exchanged in each of the following cases: a....
-
ID_T2_Q3: Which statement best summarizes the table? O The province from largest to smallest are Western, Southern, Eastern, Northern and Kigali City There are more females than males in Rwanda,...
-
What do I have to do? Please address the following items: Setting up a wireless LAN for a campus network would typically demand a wireless distribution system. Research the wireless distribution...
-
What industrial target (industry, busineChapter 7 in the book identifies targets, and attack methods. In chapter 7 "Attack Targets" (Table 7.2, page 175) select three targets identifying what...

Study smarter with the SolutionInn App