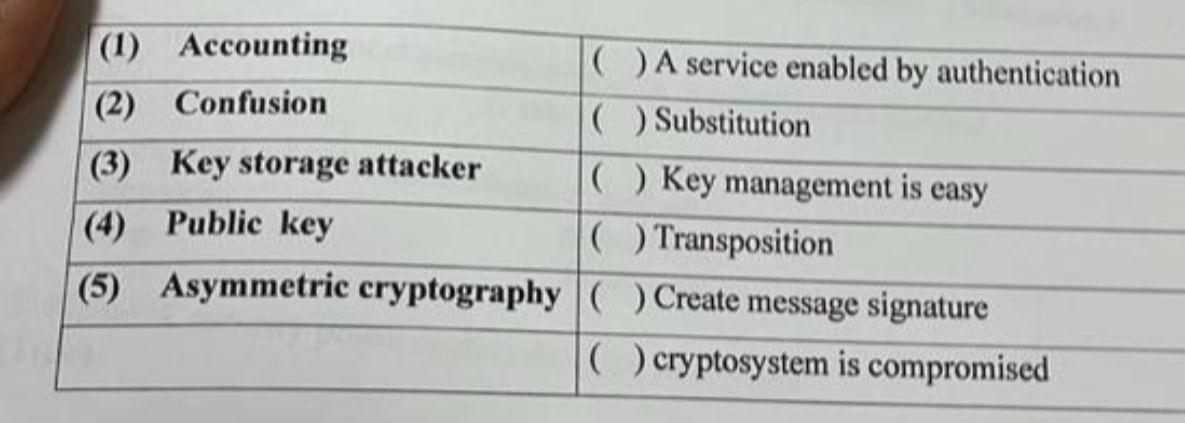
( ) A service enabled by authentication (1) Accounting (2) Confusion ( ) Substitution (3) Key...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
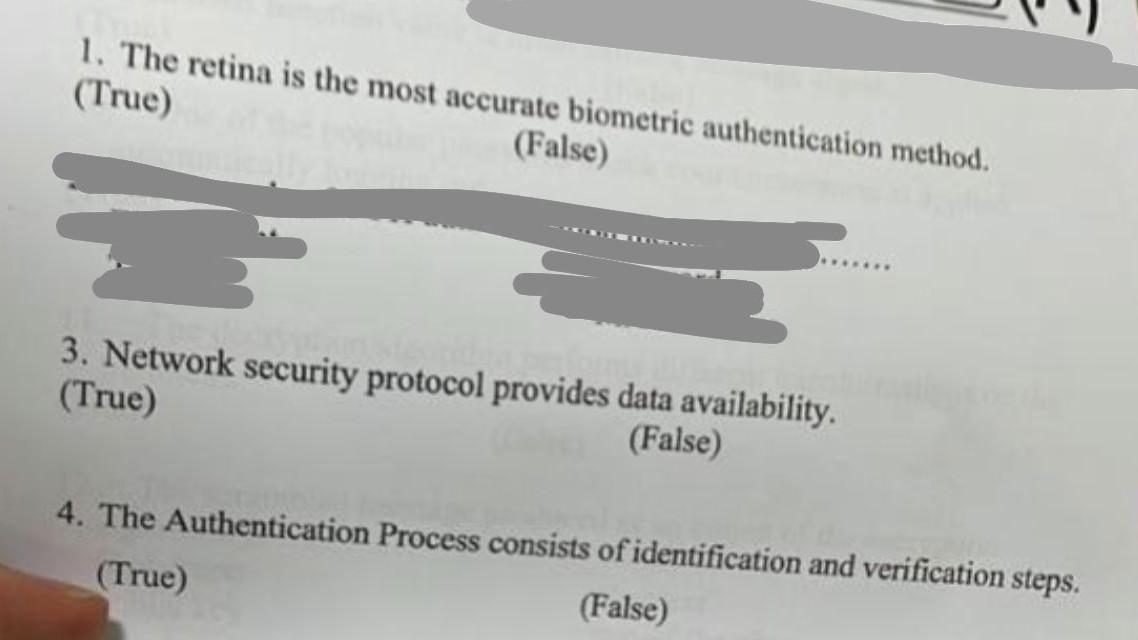
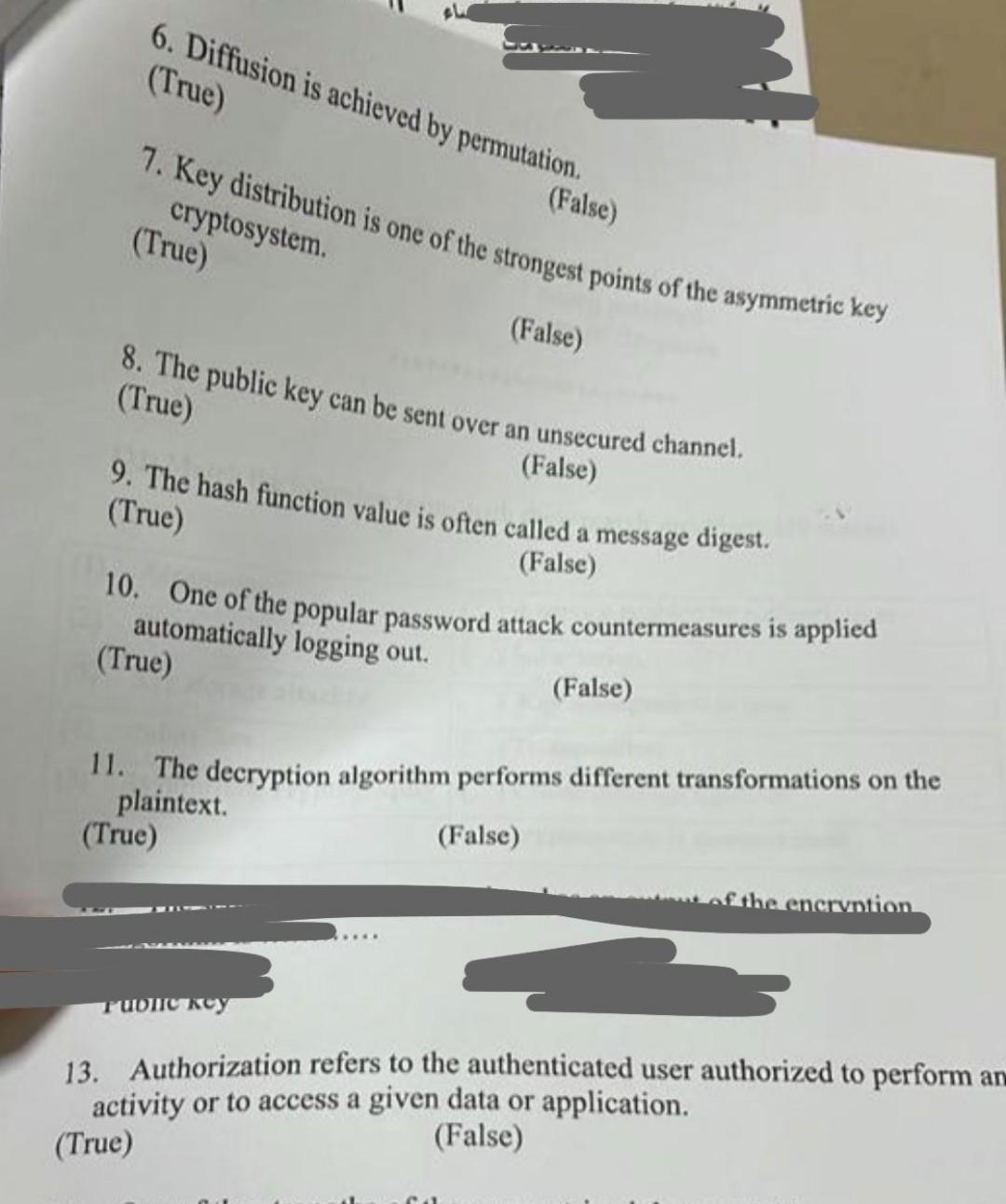
( ) A service enabled by authentication (1) Accounting (2) Confusion ( ) Substitution (3) Key storage attacker ( ) Key management is easy (4) Public key ( ) Transposition (5) Asymmetric cryptography ( ) Create message signature () cryptosystem is compromised 1. The retina is the most accurate biometric authentication method. (True) (False) 3. Network security protocol provides data availability. (True) (False) 4. The Authentication Process consists of identification and verification steps. (True) (False) 6. Diffusion is achieved by permutation. (True) 7. Key distribution is one of the strongest points of the asymmetric key cryptosystem. (True) (False) (False) 8. The public key can be sent over an unsecured channel. (True) (False) 9. The hash function value is often called a message digest. (True) (False) 10. One of the popular password attack countermeasures is applied automatically logging out. (True) Tublic key (False) 11. The decryption algorithm performs different transformations on the plaintext. (True) (False) encryption 13. Authorization refers to the authenticated user authorized to perform and activity or to access a given data or application. (True) (False) ( ) A service enabled by authentication (1) Accounting (2) Confusion ( ) Substitution (3) Key storage attacker ( ) Key management is easy (4) Public key ( ) Transposition (5) Asymmetric cryptography ( ) Create message signature () cryptosystem is compromised 1. The retina is the most accurate biometric authentication method. (True) (False) 3. Network security protocol provides data availability. (True) (False) 4. The Authentication Process consists of identification and verification steps. (True) (False) 6. Diffusion is achieved by permutation. (True) 7. Key distribution is one of the strongest points of the asymmetric key cryptosystem. (True) (False) (False) 8. The public key can be sent over an unsecured channel. (True) (False) 9. The hash function value is often called a message digest. (True) (False) 10. One of the popular password attack countermeasures is applied automatically logging out. (True) Tublic key (False) 11. The decryption algorithm performs different transformations on the plaintext. (True) (False) encryption 13. Authorization refers to the authenticated user authorized to perform and activity or to access a given data or application. (True) (False)
Expert Answer:
Answer rating: 100% (QA)
There i am providing the answer for all True and False The retina is the most accurate biometric authentication method Explanation False While the retina is considered a highly accurate biometric auth... View the full answer

Related Book For 

Accounting Information Systems The Crossroads of Accounting & IT
ISBN: 978-0132991322
2nd Edition
Authors: Donna Kay, Ali Ovlia
Posted Date:
Students also viewed these programming questions
-
After reading "No, I Do Not Want to Pet Your Dog," consider the organization of the essay. This essay seems to have a delayed thesis statement, delivered in paragraph 10 when the author says, "But...
-
1. Public keys are shared, usually by using _____ certificates A. public key B. private key C. symmetric D. root 2. _____ is a type of certificate that starts with an asterisk (*). It...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
In the late 1980s, various states and the US Congress debated placing limits on sulfur emissions to reduce the impact of acid rain. Utilities that generated electricity using coal-powered plants felt...
-
Consider again the same scenario as in the previous problem, but suppose that packets from R6 destined for 0 are switched via R6-R4-R3, while packects from R5 destined to D are switched via...
-
Your bank offers you a $140,000 line of credit with an interest rate of 2.30 percent per quarter. The loan agreement also requires that 7 percent of the unused portion of the credit line be deposited...
-
Applying the Cost of Goods Sold Model} The following amounts were obtained from the accounting records of Steed Company. \section*{Required:} Compute the missing amounts. Exercise 2016 2017 2018...
-
Job costing, accounting for manufacturing overhead, budgeted rates. The Lynn Company uses a job-costing system at its Minneapolis plant. The plant has a Machining Department and an Assembly...
-
I am having trouble with these problems on my homework I keep coming up with the wrong answers. We have a program that allows you to check your work and I am striking out. I have the formulas but I...
-
The NCAA is making plans for distributing tickets to the upcoming regional basketball championships. Up to 10,000 available seats will be divided between the media, the competing universities, and...
-
1 5 4 3 2 A 2 3 4 6 The graph above shows the function f x The graph below shows g x 6 5 4 3 2 B q g x is a transformation of f xIwhere g x Af Bx where 4 S 6
-
In this scenario, the most successful pricing plan would evolve as the product progresses through its life cycle. In our current scenario of launching new bike designs and stores, an initial method...
-
What can be a recommended alternative strategy for implementation to achieve optimal competitive positioning for the company Patagonia ? What revisions to the corporate structure should be made to...
-
Demand (in kilograms) in the market for cabbages is given by the function, QD = 76 - 4P Find the price elasticity of demand when the price is $6 per kilogram. (Round your answer to 3 decimal places.)
-
Describes the distinct phases that a consumer progresses throughout the life of a consumer?
-
1. Discuss the responsibilities of the Onboard Convention Services /Group Coordinator Manager. 2. Discuss three advantages of cruising that is offered when holding a Meeting or Event at Sea. 3....
-
Minor Electric has received a special one-time order for 900 light fixtures (units) at $20 per unit. Minor currently produces and sells 4,500 units at $21.00 each. This level represents 75% of its...
-
You've been asked to take over leadership of a group of paralegals that once had a reputation for being a tight-knit, supportive team, but you quickly figure out that this team is in danger of...
-
Discuss the role of accounting systems and business intelligence in assisting organizations to improve sustainability.
-
What are the three objectives of COSOs Internal ControlIntegrated Framework? Why are these important for internal control?
-
Why is knowledge of XBRL important to accounting professionals? Explain.
-
Bank Reconciliation} Shortly after July 31, Towanda Corporation received a bank statement containing the following information: July cash transactions and balances on Towanda's records are shown in...
-
Quality Review. Charalambos Viachoutsicos is assigned the responsibility of setting up a quality review programme at his St Petersburg, Russia, audit firm, Levenchuk. Required A. What should the...
-
Bank Reconciliation} Darjeeling Corporation received the bank statement shown below for the month of October: The cash records of Darjeeling Corporation provide the following information: The items...

Study smarter with the SolutionInn App