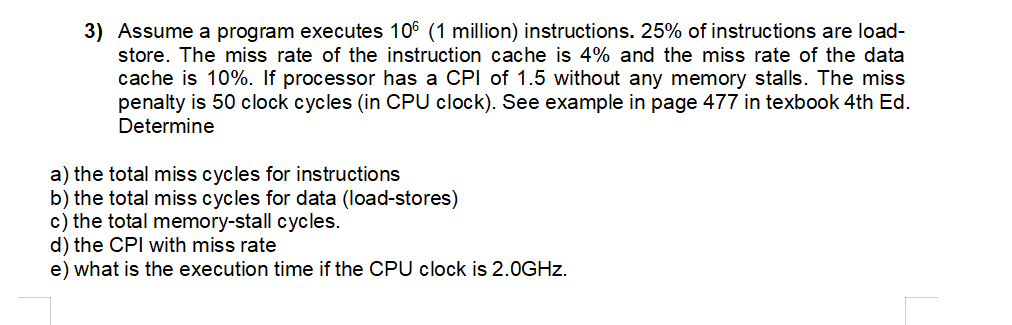
3) Assume a program executes 106 (1 million) instructions. 25% of instructions are load- store. The...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
3) Assume a program executes 106 (1 million) instructions. 25% of instructions are load- store. The miss rate of the instruction cache is 4% and the miss rate of the data cache is 10%. If processor has a CPI of 1.5 without any memory stalls. The miss penalty is 50 clock cycles (in CPU clock). See example in page 477 in texbook 4th Ed. Determine a) the total miss cycles for instructions b) the total miss cycles for data (load-stores) c) the total memory-stall cycles. d) the CPI with miss rate e) what is the execution time if the CPU clock is 2.0GHz. 3) Assume a program executes 106 (1 million) instructions. 25% of instructions are load- store. The miss rate of the instruction cache is 4% and the miss rate of the data cache is 10%. If processor has a CPI of 1.5 without any memory stalls. The miss penalty is 50 clock cycles (in CPU clock). See example in page 477 in texbook 4th Ed. Determine a) the total miss cycles for instructions b) the total miss cycles for data (load-stores) c) the total memory-stall cycles. d) the CPI with miss rate e) what is the execution time if the CPU clock is 2.0GHz.
Expert Answer:
Answer rating: 100% (QA)
This question pertains to computer architecture specifically the impact of cache misses on the performance of a CPU executing a program Lets solve each part step by step a Total miss cycles for instru... View the full answer

Related Book For 

Digital Design and Computer Architecture
ISBN: 978-0123944245
2nd edition
Authors: David Harris, Sarah Harris
Posted Date:
Students also viewed these programming questions
-
The Fielder manufacturing company uses job order costing system. The company uses machine hours to apply overhead cost to jobs. At the beginning of 2020, the company estimated that 7,850 machine...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Tory Company sells a single product. Troy estimates demand and costs at various activity levels as follows: How much profit will Troy have if a price of $45 is charged? Units Sold Price Total...
-
Describe the conflict between the creative department and the research department. Do you think creatives are justified in their hesitancy to subject their work to advertising researchers? Why? Is...
-
Recall, from Exercise 6.36, that stock screeners are automated tools used by investment companies to help clients select a portfolio of stocks to invest in. The data on the annualized percentage...
-
A company's issued share capital consists of 15 million ordinary shares of 50p each and 20 million 7% preference shares of 1 each. The company's pre-tax profit for the year to 31 July 2000 is...
-
Frisbees are produced according to the production function q = 2K + L Where q = Output of Frisbees per hour K = Capital input per hour L = Labor input per hour a. If K = 10, how much L is needed to...
-
The rectifier function r(2 ) = if x r(x) and s(x)
-
. With the information generated from the following table derivate from the Bureau of Economic Analysis (https://apps.bea.gov/iTable/index_nipa.cfm), please do the regression analysis, with the...
-
Jeremy earned $101,600 in salary and $7,600 in interest income during the year. Jeremy's employer withheld $11,00o0 of federal income taxes from Jeremy's paychecks during the year. Jeremy has one...
-
For each of the following threats, give a control that might reduce exposures: a. Pirated software b. Violation of the licensing conditions pertaining to a proprietary database c. Employee use of an...
-
Briefly distinguish between viruses and worms. List two controls over viruses and worms (one for viruses and one for worms) that security administrators might implement to reduce exposures.
-
Give one preventive control and one detective control over the activities of computer hackers.
-
What are the controls of last resort? Briefly explain the nature of each.
-
Briefly describe the major components of an emergency plan.
-
(c) At 31 December 2001 the capital structure of a company was as follows: Ordinary share capital K 100,000 shares of 50n each Share premium account 50,000 180,000 During 2002 the company made a...
-
An 8.0 kg crate is pulled 5.0 m up a 30 incline by a rope angled 18 above the incline. The tension in the rope is 120 N, and the crates coefficient of kinetic friction on the incline is 0.25. a. How...
-
Convert each of the following octal numbers to binary, hexadecimal, and decimal. (a) 23 8 (b) 45 8 (c) 371 8 (d) 2560 8
-
Write an HDL module for the circuit in Exercise 3.31. Data from problem 3.31 Analyze the FSM shown in Figure 3.72. Write the state transition and output tables and sketch the state transition...
-
Design an asynchronously settable D flip-flop using logic gates.
-
Maurice Turner, the owner of a newsletter for managers of hotels and restaurants, has prepared the following condensed amounts from his companys financial statements for 20x6: Given these figures,...
-
What percentage of a general managers time and energy should be devoted to public relations and advocacy?
-
In CVS Corporations annual report in the Supplement to Chapter 1, refer to the balance sheet and the Summary of Significant Accounting Policies in the notes to the financial statements. 1. Examine...

Study smarter with the SolutionInn App