(a) Alice use RSA to send the following message to Bob. 227163 233312 203044 475734 64606...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
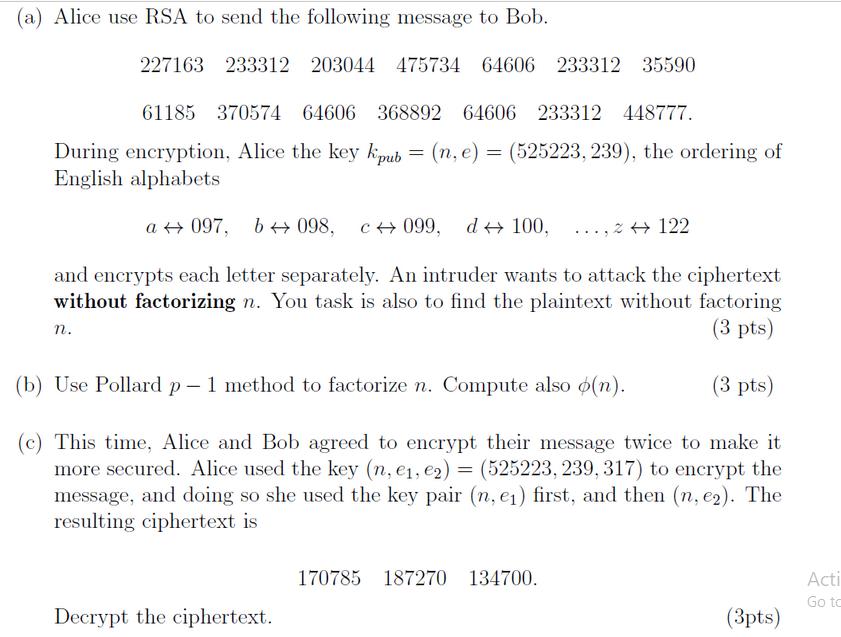
(a) Alice use RSA to send the following message to Bob. 227163 233312 203044 475734 64606 233312 35590 61185 370574 64606 368892 64606 233312 448777. During encryption, Alice the key kipub = (n. e) = (525223, 239), the ordering of English alphabets a097, b→ 098, c099, d 100, ..., 2 → 122 and encrypts each letter separately. An intruder wants to attack the ciphertext without factorizing n. You task is also to find the plaintext without factoring (3 pts) (b) Use Pollard p - 1 method to factorize n. Compute also o(n). (3 pts) This time, Alice and Bob agreed to encrypt their message twice to make it more secured. Alice used the key (n, e₁, e2) = (525223, 239, 317) to encrypt the message, and doing so she used the key pair (n, e₁) first, and then (n, e2). The resulting ciphertext is n. Decrypt the ciphertext. 170785 187270 134700. (3pts) Acti Go to (a) Alice use RSA to send the following message to Bob. 227163 233312 203044 475734 64606 233312 35590 61185 370574 64606 368892 64606 233312 448777. During encryption, Alice the key kipub = (n. e) = (525223, 239), the ordering of English alphabets a097, b→ 098, c099, d 100, ..., 2 → 122 and encrypts each letter separately. An intruder wants to attack the ciphertext without factorizing n. You task is also to find the plaintext without factoring (3 pts) (b) Use Pollard p - 1 method to factorize n. Compute also o(n). (3 pts) This time, Alice and Bob agreed to encrypt their message twice to make it more secured. Alice used the key (n, e₁, e2) = (525223, 239, 317) to encrypt the message, and doing so she used the key pair (n, e₁) first, and then (n, e2). The resulting ciphertext is n. Decrypt the ciphertext. 170785 187270 134700. (3pts) Acti Go to
Expert Answer:
Answer rating: 100% (QA)
a To decrypt the given ciphertext without factoring n we can use the RSA decryption formula m cd mod ... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
Describe the process of normalization in database design. Explain each normal form from 1NF to BCNF with examples. Discuss the types of anomalies normalization aims to prevent and how denormalization...
-
The local outlet of a large home and garden chain store wants to better understand the needs and perceptions of its customers. The general manager is attracted to the option of using an online survey...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
Coronado Industries has adopted the following production budget for the first 4 months of 2022. Each unit requires 4 pounds of raw materials costing $6 per pound. On December 31, 2021, the ending raw...
-
On November 4, 2011, Blue Company acquired an asset (27.5-year residential real property) for $200,000 for use in its business. In 2011 and 2012, respectively, Blue took $642 and $5,128 of cost...
-
Describe how you would manage translation and economic risk.
-
Prepare the operating budget, the financial budget, and the supporting schedules.
-
Some people suggest that the most effective organizations have the strongest cultures. What do we mean by the strength of organizational culture, and what possible problems are there with a strong...
-
CHONE HApplication Directions: For each of the questions in this section, write your answers in the spaces provided. Show all the steps. 17. (4 points) Household smoke detectors contain 200 g of a...
-
Using a computer spreadsheet, set up a cash flow statement to capture the anticipated cash flow in the following case study scenario. Cash Flow Planning Exercise This exercise is an opportunity to...
-
2 = x - Find the equations of the tangent lines to the curve y = x - x - 2 that pass through he point (3,2). Include a sketch to illustrate your solution. (7 marks)
-
Edith was a one-third partner in the DEF partnership with a $700 outside tax basis. On 1/1/2023, DEF had the following balance sheet: TB FMV Assets Cash 300 300 Capital Asset #31 800 600 Capital...
-
The following information is relevant for the year ended 31 December, 2022 for Grace Ltd 2022 2021 GH'000 GH'000 Cash 21,000 10,000 Account receivables 30,000 20,000 Inventories 26,000 30,000 PPE...
-
Burger Queen offers a lunch meal deal for its customers. The customer will get a burger, fry, soft drink, and ice cream for $17. If the customer were to buy each item individually, the cost would be...
-
Below is an extracts from Eco bank and Cal Bank financial statements; Extracts from statements of financial position Equity & Liabilities Eco Bank Cal Bank Assets Eco Bank Cal Bank GHm GHm GHm GHm...
-
Houghton Chemicals, which started operations one year ago, has two divisions: Alloys and Petro. Both divisions invest heavily in R&D, which is assumed to generate benefits for five years. R&D...
-
ETHICS & COMMUNICATION LAWS PRINT MEDIA a.) Enlisted below are two Media Acts that brought significant impacts on the overall Print Media ethical conducts in Malaysia Briefly define, elaborate, an...
-
Rosalie owns 50% of the outstanding stock of Salmon Corporation. In a qualifying stock redemption, Salmon distributes $80,000 to Rosalie in exchange for one-half of her shares, which have a basis of...
-
Consider an RTP session consisting of four users, all of which are sending and receiving RTP packets into the same multicast address. Each user sends v ideo at 100 kbps. a. RTCP will limit its...
-
Suppose the three departmental switches in Figure 5.26 All links are 100 Mbps. Now answer the questions posed in problem P29.
-
Repeat Problem P44 using the graph from Problem P24. Assume that z in the broadcast source, and that the link costs are as shown in Problem P22. In Problem P44 Consider the topology shown in Figure...
-
What is the necessary condition for a share buyback to increase earnings per share? to increase the book value of equity capital per share?
-
In what circumstances does a company have good reason to have a capital decrease?
-
Forgetting tax considerations, can a capital decrease enhance the value of the companys operating assets? the value of its shares?

Study smarter with the SolutionInn App


