(a) An n n matrix K is the encryption matrix for the Hill cipher. Give...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
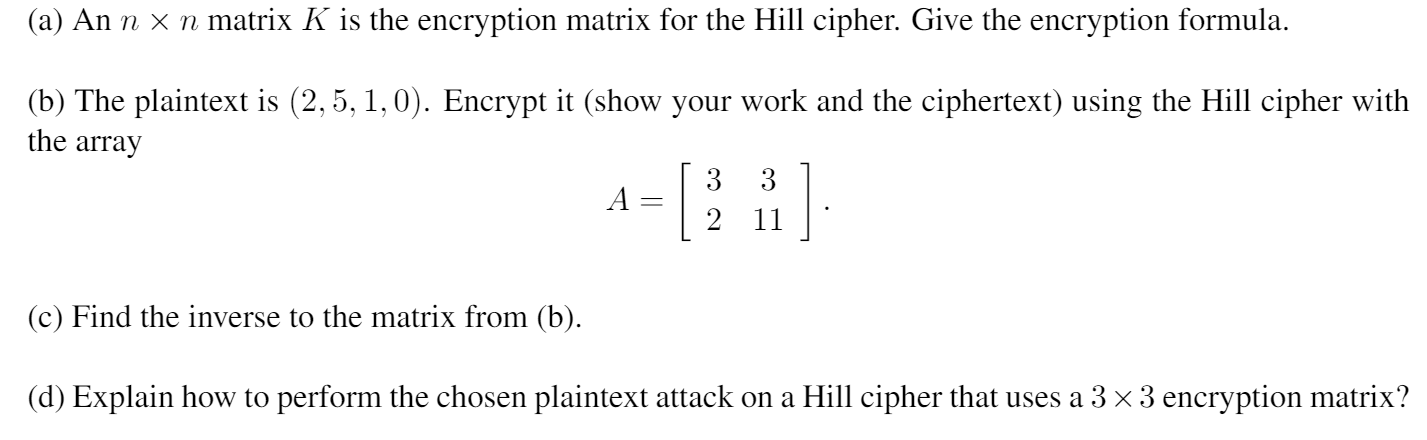
(a) An n × n matrix K is the encryption matrix for the Hill cipher. Give the encryption formula. (b) The plaintext is (2, 5, 1,0). Encrypt it (show your work and the ciphertext) using the Hill cipher with the array (c) Find the inverse to the matrix from (b). A = 3 3 2 11 (d) Explain how to perform the chosen plaintext attack on a Hill cipher that uses a 3 × 3 encryption matrix? (a) An n × n matrix K is the encryption matrix for the Hill cipher. Give the encryption formula. (b) The plaintext is (2, 5, 1,0). Encrypt it (show your work and the ciphertext) using the Hill cipher with the array (c) Find the inverse to the matrix from (b). A = 3 3 2 11 (d) Explain how to perform the chosen plaintext attack on a Hill cipher that uses a 3 × 3 encryption matrix?
Expert Answer:
Answer rating: 100% (QA)
Solution Hill cipher is a polygraphic cipher which is based on Linear Alg... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Encrypt the following words using a Caesar cipher with a distance value of 5. Provide an algorithm written in python to generate the cypher. So Python Much cipher Wow Write a program to open...
-
Please show your work and write out your solutions in detail by giving formulas and a short summary at the end. Please do not just post about financial calc or excel without explaining how you got...
-
The ciphertext OIKYWVHBX was produced by encrypting a plaintext message using the Vigenre cipher with key HOT. What is the plaintext message?
-
Identify and discuss three ways that tourism and hospitality businesses can maintain a long-term relationship with their clients
-
Long-term Treasury bonds currently are selling at yields to maturity of nearly 8%. You expect interest rates to fall. The rest of the market thinks that they will remain unchanged over the coming...
-
The Carry-Haul Truck Rental firm has accumulated extra trucks at three of its truck leasing outlets, as shown: Leasing Outlet Extra Trucks 1. Toronto .............................................. 70...
-
Construct a 95% prediction interval for an individual response when x = 20. Exercises 610 refer to the following data set: x 25 13 16 19 29 19 16 30 y 40 20 33 30 50 37 34 37
-
Equity method entries. Hanna Company purchased 100% of the common stock of Denver Company on January 2 for $550,000. The common stock of Denver Company at this date was $200,000, and the retained...
-
Dillard's is listed on the NYSE so its financial information is readily available. Go online and find its Income Statement and Balance Sheet for 2021 and for 2019. (a) For the financial reports that...
-
Q1. Review the following accounts, subtotals, and totals; (1) describe your observations; and then (2) identify what your observations indicate. A response is given for PPE, net to help with...
-
How to convert a decimal number to binary in Java?
-
Explain how the two companies have continued to evolve their ERP systems over time, what lessons can be learned from Amazon and Apple's ERP integration experiences, and how can these lessons be...
-
Indifference curves analysis has revolutionised the way modern economists analyse consumer behaviour. a) With the aid of a relevant diagram explain what you understand by indifference curves in...
-
An appraiser inspected a two story home 25' x 50', with a full unfinished basement and an attached single story garage on slab 24' x 36'. What is this building's GLA?
-
A formula for calculating the magnitude of an earthquake is M E that uses the common = 323 log (5) (base 10) logarithm. This is called the Moment Magnitude Scale (MMS), an alternative to the more...
-
In Bylund's article, there is the quote "To a nation built on immigration it should seem strange to have a president investing in keeping foreigners out, and considering fines on employers hiring...
-
Illustrate how a bill becomes a law by creating a comic strip.
-
One study found that the elderly who do not have children dissave at about the same rate as the elderly who do have children. What might this finding imply about the reason the elderly do not dissave...
-
In a bus CSMA/CD network with a data rate of 10 Mbps, a collision occurs 20 s after the first bit of the frame leaves the sending station. What should the length of the frame be so that the sender...
-
Which of the following is a random-access protocol? a. CSMA/CD b. Polling c. TDMA
-
What is the function of the twisting in twisted-pair cable?
-
The parameters of the transistor in the circuit in Figure P7.40 are \(\beta=100\), \(V_{B E}\) (on) \(=0.7 \mathrm{~V}\), and \(V_{A}=\infty\). Neglect the capacitance effects of the transistor. (a)...
-
In the common-source amplifier in Figure 7.25 (a) in the text, a source bypass capacitor is to be added between the source terminal and ground potential. The circuit parameters are \(R_{S}=3.2...
-
Consider the common-base circuit in Figure P7.42. Choose appropriate transistor parameters. (a) Using a computer analysis, generate the Bode plot of the voltage gain magnitude from a very low...

Study smarter with the SolutionInn App


