A combination lock is installed on the entrance door of a room to ensure that only...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
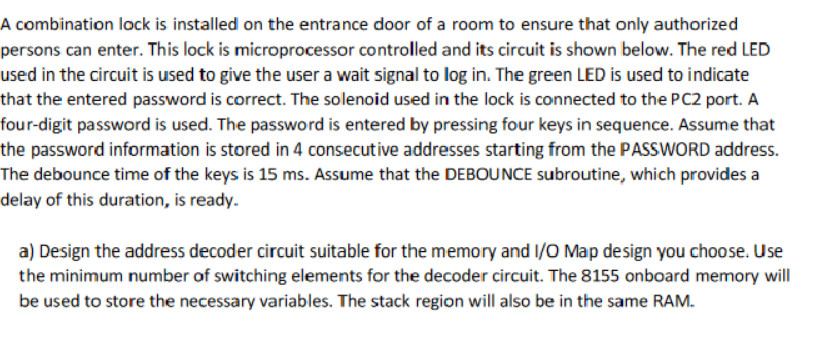
A combination lock is installed on the entrance door of a room to ensure that only authorized persons can enter. This lock is microprocessor controlled and its circuit is shown below. The red LED used in the circuit is used to give the user a wait signal to log in. The green LED is used to indicate that the entered password is correct. The solenoid used in the lock is connected to the PC2 port. A four-digit password is used. The password is entered by pressing four keys in sequence. Assume that the password information is stored in 4 consecutive addresses starting from the PASSWORD address. The debounce time of the keys is 15 ms. Assume that the DEBOUNCE subroutine, which provides a delay of this duration, is ready. a) Design the address decoder circuit suitable for the memory and I/O Map design you choose. Use the minimum number of switching elements for the decoder circuit. The 8155 onboard memory will be used to store the necessary variables. The stack region will also be in the same RAM. A combination lock is installed on the entrance door of a room to ensure that only authorized persons can enter. This lock is microprocessor controlled and its circuit is shown below. The red LED used in the circuit is used to give the user a wait signal to log in. The green LED is used to indicate that the entered password is correct. The solenoid used in the lock is connected to the PC2 port. A four-digit password is used. The password is entered by pressing four keys in sequence. Assume that the password information is stored in 4 consecutive addresses starting from the PASSWORD address. The debounce time of the keys is 15 ms. Assume that the DEBOUNCE subroutine, which provides a delay of this duration, is ready. a) Design the address decoder circuit suitable for the memory and I/O Map design you choose. Use the minimum number of switching elements for the decoder circuit. The 8155 onboard memory will be used to store the necessary variables. The stack region will also be in the same RAM.
Expert Answer:
Answer rating: 100% (QA)
To design the address decoder circuit for the memory and IO map we first need to determine the numbe... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Section 3. Feedstuffs Sampling (3 pts) List 3 types of devices (or tools) that can be used to facilitate sampling of feedstuffs from bulk bags and from bulk trucks. Explain or describe how ONE of the...
-
Dissertation Topic: "The Effects of Cybersecurity Measures on the Productivity and Well-being of Teleworkers in the Healthcare Industry". Introduction Draft no more than TWO paragraphs here -...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Write a program that takes two integer command-line arguments x and y and prints the Euclidean distance from the point (x, y) to the origin (0, 0).
-
How strong are the competitive forces confronting Under Armour, Nike, and The adidas Group? Do a five-forces analysis to support your answer.
-
Derive the magnification equation, m = h / h = q / p, for a convex mirror. Draw a ray diagram as part of the solution.
-
Suppose that we are trying to value a three-period call option on a stock that will either go up by 7 percent or down by 4 percent per period, that the exercise price of the option is $35, that the...
-
StarGaze Company leased a truck for three months. Accounting guidance classifies the lease as an operating lease. StarGaze makes lease payments of $800 at the end of each month. What journal entry...
-
Graph the exponential function. y=2(x-5) Identify the graph of the function y = 2(x-5) Z Z
-
Pat and Mandy are married and have a son, Steve, age 8. Mandy, age 29, earns $40,000 annually from her job. Pat, age 31, earns $50,000 annually from his job. Assume that Pat will die before Mandy....
-
Suppose that you buy a 12x24 FRA contract, that is, the settlement date is exactly a year from now and the maturity date is 2 years from now, with a notional principal of 1 million. The rate on the...
-
Which of the following statements about the k-nearest neighbors classifier is true? a. The decision boundary corresponding to a k-nearest neighbor classifier is a linear function of the input...
-
For 10,000 observations, suppose a classifier generates 235 false positives, 138 false negatives, 9,432 true negatives, and 195 true positives.What is the classifiers precision?
-
A sports betting company is testing the effectiveness of its online ads and has developed a classification model that predicts whether a potential customer will respond to its offer using information...
-
Which of the following statements about random forests is false? a. The predictive performance of a random forest is often competitive with a boosting ensemble, and it is computationally much...
-
Please write the expression of entropy increase through normal shock wave. Why is there an increase in entropy?
-
The Himalaya Company provides landscaping services to corporations and businesses. All its landscaping work requires Himalaya to use landscaping equipment. Its landscaping equipment has the capacity...
-
SBS Company have received a contract to supply its product to a Health Care Service Hospital. The sales involve supplying 1,250 units every quarter, the sales price is RM 85 per unit. The Client...
-
Examine the two pieces of criteria that classify that a disaster has occurred: the organization is unable to contain or control the impact of an incident, or the level of damage or destruction from...
-
Recall that once an incident has been confirmed and classified properly, the IR plan moves into the detection phase. Summarize the action steps for reacting to incidents. They include: Notifying key...
-
Emphasize to students that the most common IP breaches involve the unlawful use or duplication of software-based intellectual property, known as software piracy. Outline that in addition to the laws...
-
What are Porters generic strategies?
-
What is the link between the balanced scorecard and strategy?
-
How can the lifecycle approach be used to maximise return from a product?

Study smarter with the SolutionInn App


