1. Create a class called SecretDecoder 2. Create a main method in SecretDecoder 3. In the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
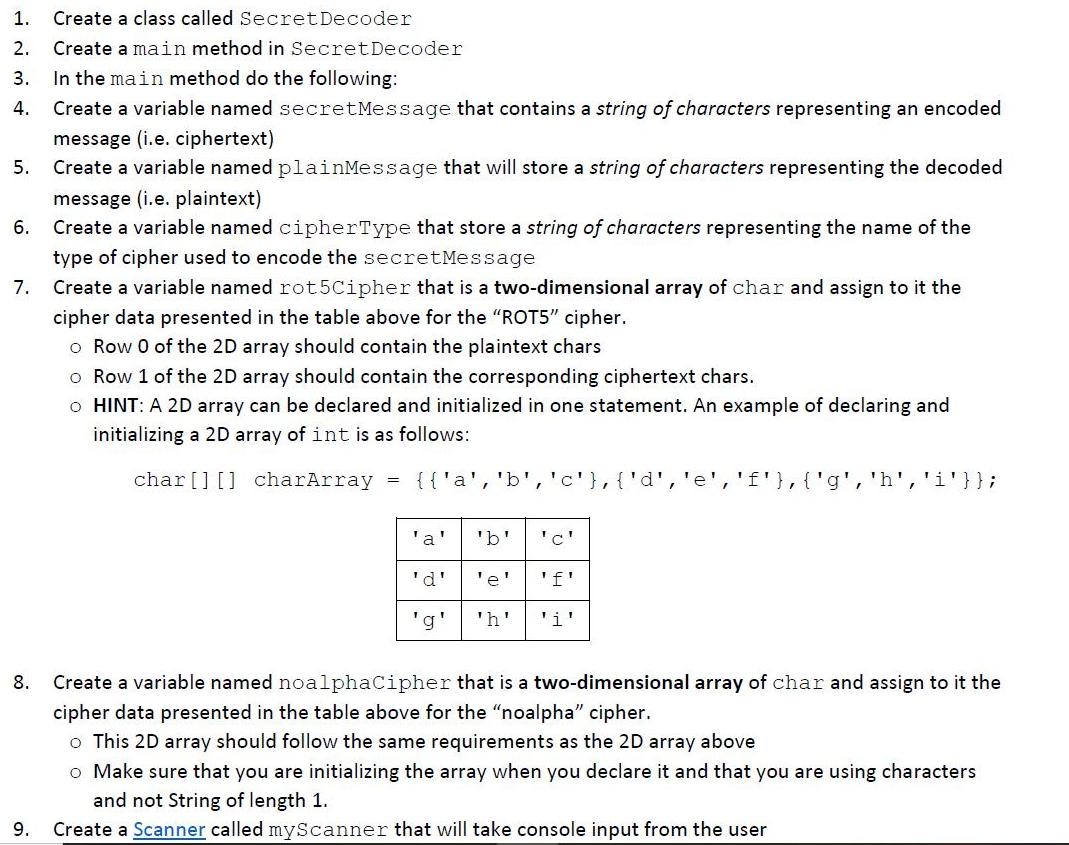
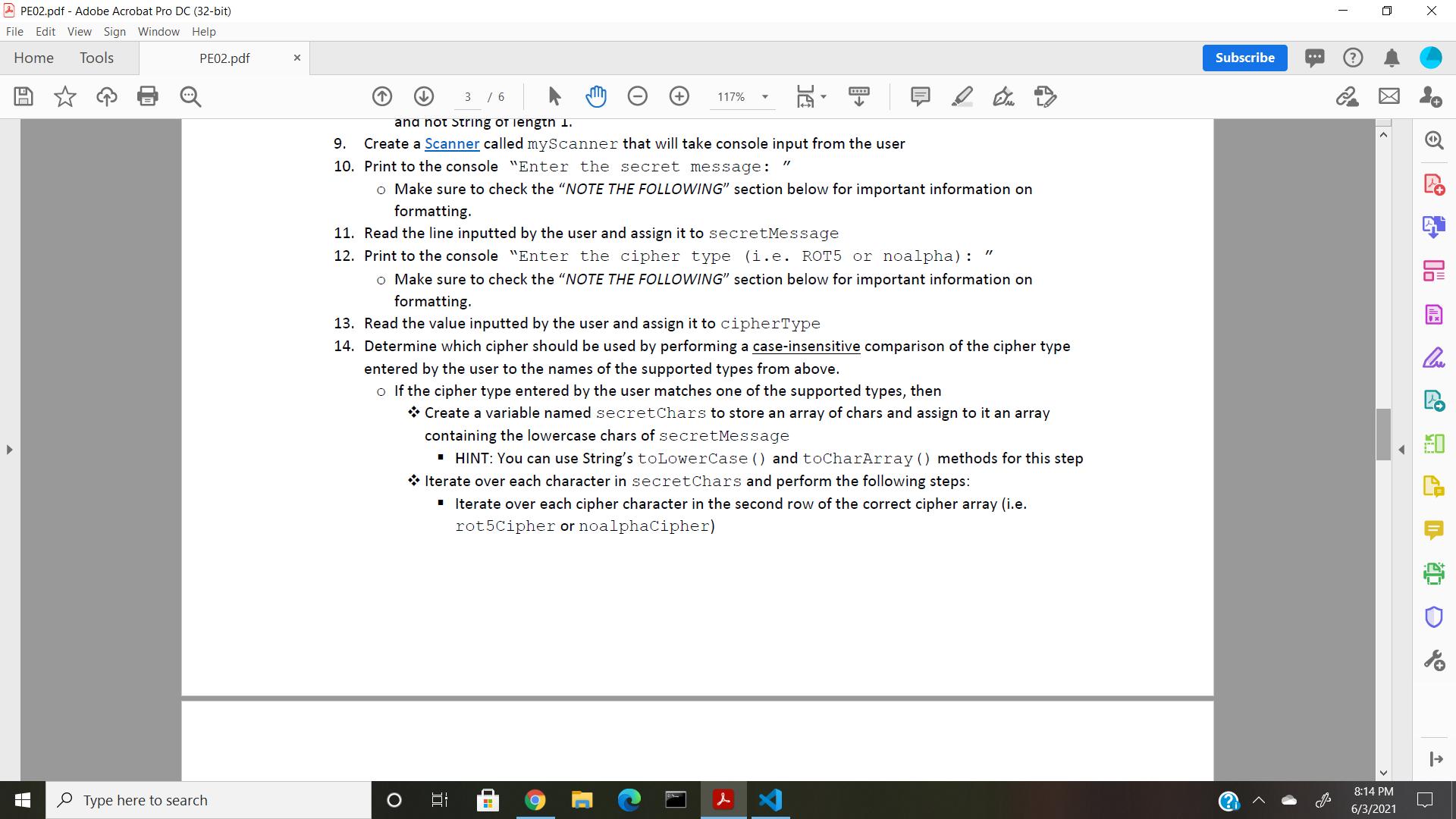
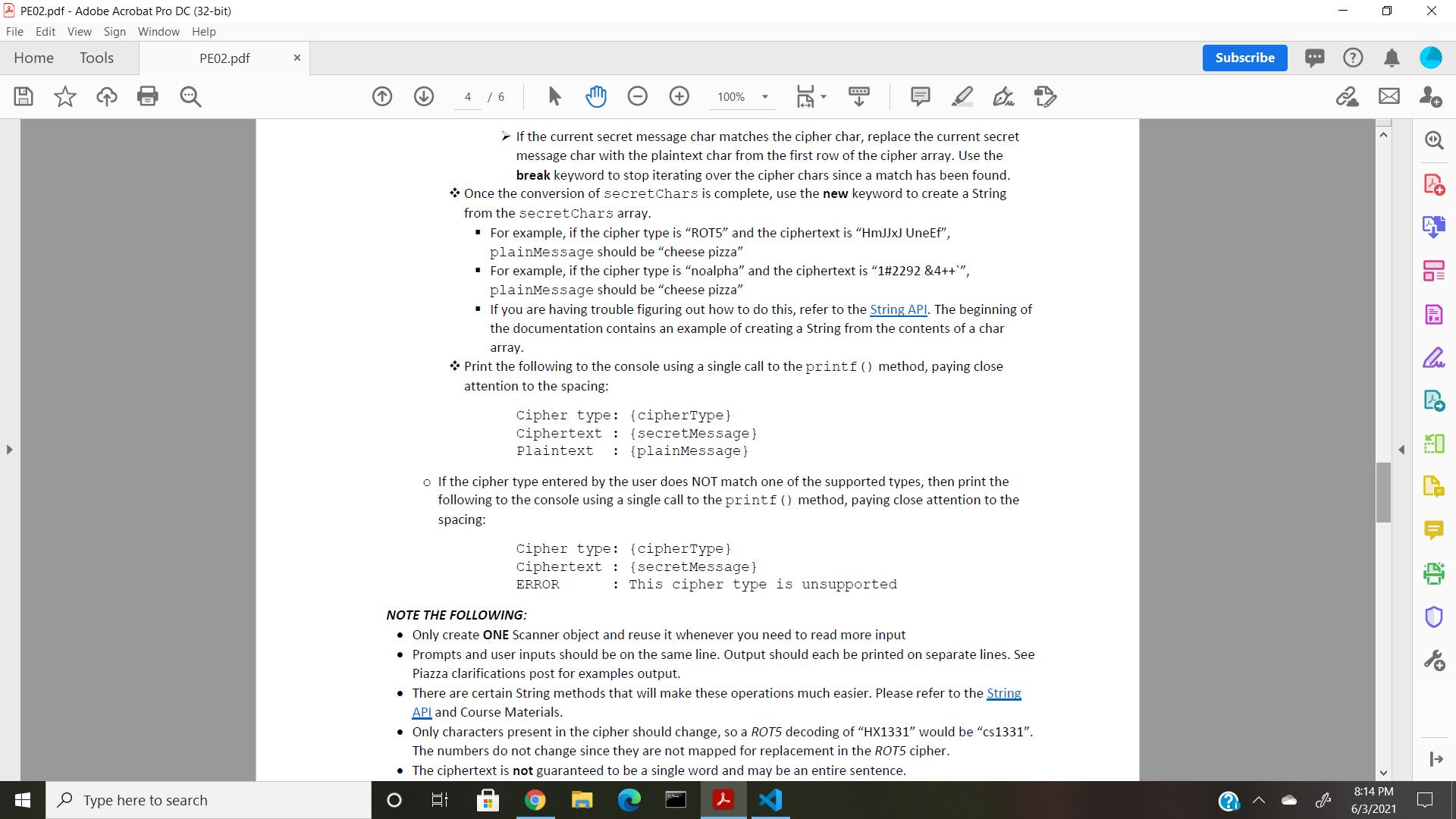
1. Create a class called SecretDecoder 2. Create a main method in SecretDecoder 3. In the main method do the following: 4. Create a variable named secretMessage that contains a string of characters representing an encoded message (i.e. ciphertext) Create a variable named plainMessage that will store a string of characters representing the decoded 5. message (i.e. plaintext) 6. Create a variable named cipherType that store a string of characters representing the name of the type of cipher used to encode the secretMessage 7. Create a variable named rot5Cipher that is a two-dimensional array of char and assign to it the cipher data presented in the table above for the "ROT5" cipher. o Row 0 of the 2D array should contain the plaintext chars o Row 1 of the 2D array should contain the corresponding ciphertext chars. o HINT: A 2D array can be declared and initialized in one statement. An example of declaring and initializing a 2D array of int is as follows: char[] [] charArray {{'a', 'b','c'},{'d','e','f'},{'g', 'h', 'i'}}; 'a' 'b' 'c' 'd' 'e' 'f' 'g' 'h' 'i' 8. Create a variable named noalphaCipher that is a two-dimensional array of char and assign to it the cipher data presented in the table above for the "noalpha" cipher. o This 2D array should follow the same requirements as the 2D array above o Make sure that you are initializing the array when you declare it and that you are using characters and not String of length 1. 9. Create a Scanner called myScanner that will take console input from the user A PE02.pdf - Adobe Acrobat Pro DC (32-bit) File Edit View Sign Window Help Home Tools PE02.pdf Subscribe 3 / 6 117% ana not String of iengtn 1. 9. Create a Scanner called myScanner that will take console input from the user 10. Print to the console "Enter the secret message: o Make sure to check the "NOTE THE FOLLOWING" section below for important information on formatting. 11. Read the line inputted by the user and assign it to secretMessage 12. Print to the console "Enter the cipher type (i.e. ROT5 or noalpha) : o Make sure to check the "NOTE THE FOLLOWING" section below for important information on formatting. 13. Read the value inputted by the user and assign it to cipherType 14. Determine which cipher should be used by performing a case-insensitive comparison of the cipher type entered by the user to the names of the supported types from above. o If the cipher type entered by the user matches one of the supported types, then * Create a variable named secretChars to store an array of chars and assign to it an array containing the lowercase chars of secretMessage · HINT: You can use String's toLowerCase () and toCharArray () methods for this step * Iterate over each character in secretChars and perform the following steps: I Iterate over each cipher character in the second row of the correct cipher array (i.e. rot5Cipher or noalphaCipher) 8:14 PM P Type here to search 6/3/2021 哈 2 PE02.pdf - Adobe Acrobat Pro DC (32-bit) File Edit View Sign Window Help Home Tools PE02.pdf Subscribe 4 / 6 100% > If the current secret message char matches the cipher char, replace the current secret message char with the plaintext char from the first row of the cipher array. Use the break keyword to stop iterating over the cipher chars since a match has been found. * Once the conversion of secretChars is complete, use the new keyword to create a String from the secretChars array. · For example, if the cipher type is "ROT5" and the ciphertext is "HMJJXJ UneEf", plainMessage should be "cheese pizza" · For example, if the cipher type is "noalpha" and the ciphertext is "1#2292 &4++", plainMessage should be "cheese pizza" . If you are having trouble figuring out how to do this, refer to the String API. The beginning of the documentation contains an example of creating a String from the contents of a char array. * Print the following to the console using a single call to the printf () method, paying close attention to the spacing: cipher type: (cipherType} ciphertext : {secretMessage} : {plainMessage} Plaintext o If the cipher type entered by the user does NOT match one of the supported types, then print the following to the console using a single call to the printf () method, paying close attention to the spacing: cipher type: (cipherType} ciphertext : {secretMessage} ERROR : This cipher type is unsupported NOTE THE FOLLOWING: • Only create ONE Scanner object and reuse it whenever you need to read more input • Prompts and user inputs should be on the same line. Output should each be printed on separate lines. See Piazza clarifications post for examples output. • There are certain String methods that will make these operations much easier. Please refer to the String API and Course Materials. • Only characters present in the cipher should change, so a ROT5 decoding of "HX1331" would be "cs1331". The numbers do not change since they are not mapped for replacement in the ROT5 cipher. • The ciphertext is not guaranteed to be a single word and may be an entire sentence. 8:14 PM P Type here to search 6/3/2021 哈 1. Create a class called SecretDecoder 2. Create a main method in SecretDecoder 3. In the main method do the following: 4. Create a variable named secretMessage that contains a string of characters representing an encoded message (i.e. ciphertext) Create a variable named plainMessage that will store a string of characters representing the decoded 5. message (i.e. plaintext) 6. Create a variable named cipherType that store a string of characters representing the name of the type of cipher used to encode the secretMessage 7. Create a variable named rot5Cipher that is a two-dimensional array of char and assign to it the cipher data presented in the table above for the "ROT5" cipher. o Row 0 of the 2D array should contain the plaintext chars o Row 1 of the 2D array should contain the corresponding ciphertext chars. o HINT: A 2D array can be declared and initialized in one statement. An example of declaring and initializing a 2D array of int is as follows: char[] [] charArray {{'a', 'b','c'},{'d','e','f'},{'g', 'h', 'i'}}; 'a' 'b' 'c' 'd' 'e' 'f' 'g' 'h' 'i' 8. Create a variable named noalphaCipher that is a two-dimensional array of char and assign to it the cipher data presented in the table above for the "noalpha" cipher. o This 2D array should follow the same requirements as the 2D array above o Make sure that you are initializing the array when you declare it and that you are using characters and not String of length 1. 9. Create a Scanner called myScanner that will take console input from the user A PE02.pdf - Adobe Acrobat Pro DC (32-bit) File Edit View Sign Window Help Home Tools PE02.pdf Subscribe 3 / 6 117% ana not String of iengtn 1. 9. Create a Scanner called myScanner that will take console input from the user 10. Print to the console "Enter the secret message: o Make sure to check the "NOTE THE FOLLOWING" section below for important information on formatting. 11. Read the line inputted by the user and assign it to secretMessage 12. Print to the console "Enter the cipher type (i.e. ROT5 or noalpha) : o Make sure to check the "NOTE THE FOLLOWING" section below for important information on formatting. 13. Read the value inputted by the user and assign it to cipherType 14. Determine which cipher should be used by performing a case-insensitive comparison of the cipher type entered by the user to the names of the supported types from above. o If the cipher type entered by the user matches one of the supported types, then * Create a variable named secretChars to store an array of chars and assign to it an array containing the lowercase chars of secretMessage · HINT: You can use String's toLowerCase () and toCharArray () methods for this step * Iterate over each character in secretChars and perform the following steps: I Iterate over each cipher character in the second row of the correct cipher array (i.e. rot5Cipher or noalphaCipher) 8:14 PM P Type here to search 6/3/2021 哈 2 PE02.pdf - Adobe Acrobat Pro DC (32-bit) File Edit View Sign Window Help Home Tools PE02.pdf Subscribe 4 / 6 100% > If the current secret message char matches the cipher char, replace the current secret message char with the plaintext char from the first row of the cipher array. Use the break keyword to stop iterating over the cipher chars since a match has been found. * Once the conversion of secretChars is complete, use the new keyword to create a String from the secretChars array. · For example, if the cipher type is "ROT5" and the ciphertext is "HMJJXJ UneEf", plainMessage should be "cheese pizza" · For example, if the cipher type is "noalpha" and the ciphertext is "1#2292 &4++", plainMessage should be "cheese pizza" . If you are having trouble figuring out how to do this, refer to the String API. The beginning of the documentation contains an example of creating a String from the contents of a char array. * Print the following to the console using a single call to the printf () method, paying close attention to the spacing: cipher type: (cipherType} ciphertext : {secretMessage} : {plainMessage} Plaintext o If the cipher type entered by the user does NOT match one of the supported types, then print the following to the console using a single call to the printf () method, paying close attention to the spacing: cipher type: (cipherType} ciphertext : {secretMessage} ERROR : This cipher type is unsupported NOTE THE FOLLOWING: • Only create ONE Scanner object and reuse it whenever you need to read more input • Prompts and user inputs should be on the same line. Output should each be printed on separate lines. See Piazza clarifications post for examples output. • There are certain String methods that will make these operations much easier. Please refer to the String API and Course Materials. • Only characters present in the cipher should change, so a ROT5 decoding of "HX1331" would be "cs1331". The numbers do not change since they are not mapped for replacement in the ROT5 cipher. • The ciphertext is not guaranteed to be a single word and may be an entire sentence. 8:14 PM P Type here to search 6/3/2021 哈
Expert Answer:
Answer rating: 100% (QA)
package Security import javautilScanner Defines class SecretDecode public class SecretDecode main method definition public static void mainString s To store secret message String secretMessage To stor... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Create a class called Heater, that contains four fields, temperature, increment, max and min, all of whose type is double. Make sure you write a description of your new Class in the comments, with...
-
Create a class called Vehicle that will hold a string Medium and int Wheels as public properties. Create a class called Car that is derived from Vehicle and contains a Make property and a Model...
-
Create a class called Printer and a class called Job that will simulate a computer printer. The printer should store a queue of Job objects until they are printed. Each Job should consist of a title...
-
State whether the following statements are true or false. Also, very briefly mention the reason if the statement is false. i. TOFO Surfactants increase the surface tension of water. ii. TOFO The Mach...
-
In virtually all systems that include DMA modules, DMA access to main memory is given higher priority than processor access to main memory. Why?
-
Explain how to calculate the present value and future value of an ordinary annuity and an annuity due.
-
After factory overhead has been applied to work in process, what does a credit balance in Factory Overhead indicate?
-
Glaser Services acquired 30% of the outstanding common stock of Nickels Company on January 1, 2010, by paying $800,000 for the 45,000 shares. Nickels declared and paid $0.30 per share cash dividends...
-
Winners of the Georgia Lotto drawing are given the choice of receiving the winning amount divided equally over 21 years or as alump-sum cash option amount. The cash option amount is determined by...
-
Oakwood Hospital is considering using ABC analysis to classify laboratory SKUs into three categories: those that will be delivered daily from their supplier (Class A items), those that will be...
-
Air (an ideal gas) enters a compressor with a pressure of 14.4 psia, a temperature of 70F, and a volumetric flow rate of 50 ft/s. The air exits to 70 psia, 190F. If the measured power required by the...
-
Of the following, which is the most comprehensive definition of monitoring and controlling? a. To monitor plan resources and make replacements as needed b. To check for variances from the plan and...
-
Complete the following statements. (a) Receptance is the frequency-domain ratio of _________________ to __________________ . (b) Mobility is the frequency-domain ratio of _____________________ to...
-
An activity performed by the project manager on a daily basis is communicating with individual team members, the team, company personnel, vendors, and customers. What is the approximate percentage of...
-
The project manager of the retooling project has been replaced by the company in an effort to finish the project within budget. The replacement project manager wants to determine the rate at which...
-
Find three commercial suppliers of dynamic signal analyzers for modal testing.
-
how do i estimate the parameters of the linear regression model
-
You are a U.S. investor who purchased British securities for 2,000 one year ago when the British pound cost U.S. $1.50. What is your total return (based on U.S. dollars) if the value of the...
-
Let A be a nilpotent matrix (that is, Am = 0 for some m > 1). Show that = 0 is the only eigenvalue of A.
-
Classify each of the quadratic forms in Exercises 1-3 as positive definite, positive semidefinite, negative definite, negative semidefinite, or indefinite. 1. 2. 3. - 2x2 - 2y2 + 2xy xi 2x2
-
a. Prove that a graph is bipartite if and only if its vertices can be labeled so that its adjacency matrix can be partitioned as b. Using the result in part (a), prove that a bipartite graph has no...
-
Paths (a) and (b) are each paths in some larger network. In each case, decide whether the path is an augmenting path, and if so, use the method suggested by (7)-(10) to augment the path. (a) Exercise...
-
Check the constraint (a) of (1) for the augmented flow \(f_{\epsilon}\), defined by (10).
-
Show that if, in the maximal flow algorithm, the breadth-first search cannot label the sink, then there is no augmenting path from source to sink. (Hint: Suppose that one did exist. Consider the...

Study smarter with the SolutionInn App