You have an i.i.d. sample {(, X, X2i): i = 1,...,n). You want to estimate the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
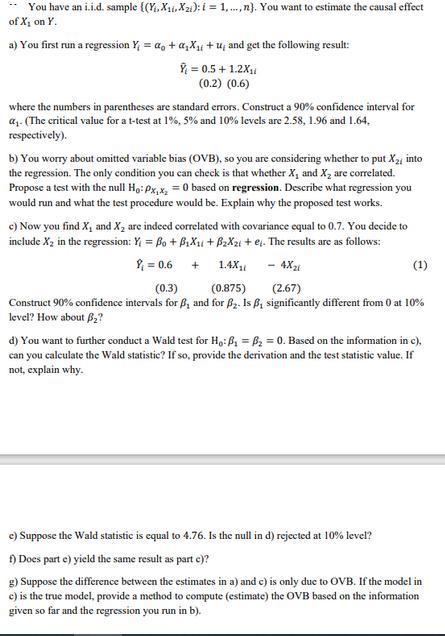
You have an i.i.d. sample {(₁, X₁, X2i): i = 1,...,n). You want to estimate the causal effect of X, on Y. a) You first run a regression Y₁ = a + a₁X₁ +u, and get the following result: = 0.5 +1.2X₁ (0.2) (0.6) where the numbers in parentheses are standard errors. Construct a 90% confidence interval for a₁. (The critical value for a t-test at 1%, 5% and 10% levels are 2.58, 1.96 and 1.64. respectively). b) You worry about omitted variable bias (OVB), so you are considering whether to put X₂, into the regression. The only condition you can check is that whether X, and X₂ are correlated. Propose a test with the null Ho: Px,x₂ = 0 based on regression. Describe what regression you would run and what the test procedure would be. Explain why the proposed test works. c) Now you find X₁ and X₂ are indeed correlated with covariance equal to 0.7. You decide to include X₂ in the regression: Y = Bo + B₂X₁ + B2X2 + e. The results are as follows: 0.6 + - 4Xzi 1.4X₁1 (0.3) (0.875) (2.67) Construct 90% confidence intervals for B, and for B₂. Is B, significantly different from 0 at 10% level? How about B₂? (1) d) You want to further conduct a Wald test for Ho: B₁ B₂ = 0. Based on the information in c), can you calculate the Wald statistic? If so, provide the derivation and the test statistic value. If not, explain why. e) Suppose the Wald statistic is equal to 4.76. Is the null in d) rejected at 10% level? f) Does parte) yield the same result as part e)? g) Suppose the difference between the estimates in a) and c) is only due to OVB. If the model in c) is the true model, provide a method to compute (estimate) the OVB based on the information given so far and the regression you run in b). You have an i.i.d. sample {(₁, X₁, X2i): i = 1,...,n). You want to estimate the causal effect of X, on Y. a) You first run a regression Y₁ = a + a₁X₁ +u, and get the following result: = 0.5 +1.2X₁ (0.2) (0.6) where the numbers in parentheses are standard errors. Construct a 90% confidence interval for a₁. (The critical value for a t-test at 1%, 5% and 10% levels are 2.58, 1.96 and 1.64. respectively). b) You worry about omitted variable bias (OVB), so you are considering whether to put X₂, into the regression. The only condition you can check is that whether X, and X₂ are correlated. Propose a test with the null Ho: Px,x₂ = 0 based on regression. Describe what regression you would run and what the test procedure would be. Explain why the proposed test works. c) Now you find X₁ and X₂ are indeed correlated with covariance equal to 0.7. You decide to include X₂ in the regression: Y = Bo + B₂X₁ + B2X2 + e. The results are as follows: 0.6 + - 4Xzi 1.4X₁1 (0.3) (0.875) (2.67) Construct 90% confidence intervals for B, and for B₂. Is B, significantly different from 0 at 10% level? How about B₂? (1) d) You want to further conduct a Wald test for Ho: B₁ B₂ = 0. Based on the information in c), can you calculate the Wald statistic? If so, provide the derivation and the test statistic value. If not, explain why. e) Suppose the Wald statistic is equal to 4.76. Is the null in d) rejected at 10% level? f) Does parte) yield the same result as part e)? g) Suppose the difference between the estimates in a) and c) is only due to OVB. If the model in c) is the true model, provide a method to compute (estimate) the OVB based on the information given so far and the regression you run in b).
Expert Answer:
Answer rating: 100% (QA)
ANSWER The total cost of producing and selling 500 bags is Cost of materials 100... View the full answer

Related Book For 

Mathematical Applications for the Management Life and Social Sciences
ISBN: 978-1305108042
11th edition
Authors: Ronald J. Harshbarger, James J. Reynolds
Posted Date:
Students also viewed these economics questions
-
d) For die casting processes: 1. What are the most common metals processed using die casting and discuss why other metals are not commonly die casted? 2. Which die casting machines usually have a...
-
The Following are the tasks you are given in the casting department: a) In a tensile test on a metal specimen, true strain = 0.08 at a stress = 265 MPa. When the flow stress = 325 MPa, the true...
-
c) A riser in the shape of a sphere is to be designed for a sand casting mold. The casting is a rectangular plate, with length = 300 mm, width 150 mm, and thickness = 20 mm. If the total...
-
Solve the inequalities and show the solution sets on the real line. -2x > 4
-
Control of the attitude q of a missile by controlling the tin angle f , as shown in Figure P11.16, involves controlling an inherently unstable plant. Consider the G p (s) = Q (s) / F (s) = 1 / s 2 5...
-
Bubba Inc. would like to have an investment that would provide cash flows of $46,897 per year for the next 10 years.. If the annual interest rate is 4%, how much should Bubba expect to pay today for...
-
Equilibrium data for extraction of methylcyclohexane (A) from nheptane (D) into aniline (S) are given in Table 13-8. Compare batch extractions of \(20 \mathrm{~kg}\) of \(40 \mathrm{wt} \%\)...
-
1. Which of the following is not a component of aggregate demand? a. Consumption b. Investment c. Government expenditures d. The supply of money e. Net exports 2. In the Great Depression, prices in...
-
The data given to the right includes data from 44 candies, and 8 of them are red. The company that makes the candy claims that 32% of its candies are red. Use the sample data to construct a 95%...
-
The misery is not miserly phenomenon refers to a sad persons spending judgment going haywire. In a recent study, 31 young adults were given $10 and randomly assigned to either a sad or a neutral...
-
The Backflushers Manufacturing Corp. uses a Raw and In Process Inventory account and expenses all conversion costs to the cost of goods sold account. At the end of each month, all inventories are...
-
a. Write a Java method named readWords that allows the user to enter five words one by one via the keyboard and save them in an ArrayList. The main method will call this method to get the word list;...
-
Write me a letter of resignation from a bank teller post, company bank south pacific the reason for my resignation is to go study abroad and broaden my education & career give 30 days notice to bank...
-
How will culminating projects assess learning objectives tied to Common Core State Standards for Kindergarten? What three learning objectives align with state standards for students' culminating...
-
Expand in taylor series, up to the lowest possible order, The following functions. Around x = -1 and x=0 b). f(x) = x+4 d). f (x)= In (x-4) f). ex-3 a) f (x) = = = = / 1 1 x-1 2 c). g(x) = +1 e). ex
-
11 LW 12. ADDI DOR 14 DW 15 SUB 11: DW 43 13. OR 14: LW IS: SUB Question & MIPS &-Stage Pipetine For this qontin 11: B, Kha) 12,811, 2 ht. B, 34-4(2) 22 mb , Fi, 844 kyland architecture Show...
-
Why is it essential to record assessment information accurately? A) To make informed instructional decisions. B) To ensure students compete with each other more effectively. C) To inflate students'...
-
What is a content filter? Where is it placed in the network to gain the best result for the organization?
-
Maximize f = 3x + 5y subject to 2x + 4y 8 3x + y 7 y 4 Solve the following linear programming problems. Restrict x 0 and y 0.
-
Use the matrix and initial probability vector in Problem 10 and find the resulting 18th probability vector. 0.5 0.5 B = 0.9 0.1
-
Employees of a firm receive annual reviews. In a certain department, 4 employees received excellent ratings, 15 received good ratings, and 1 received a marginal rating. If 3 employees in this...
-
Which of the following techniques involves the creation and use of a pair of public and private keys? a. hashing c. symmetric encryption b. asymmetric encryption d. key escrow
-
Which of the following is a preventive control? a. penetration testing c. training b. patch management d. log analysis
-
The approach to perimeter defense that involves examining only information in the packet header of each individual IP packet is referred to as a. deep packet inspection c. stateful packet filtering...

Study smarter with the SolutionInn App


