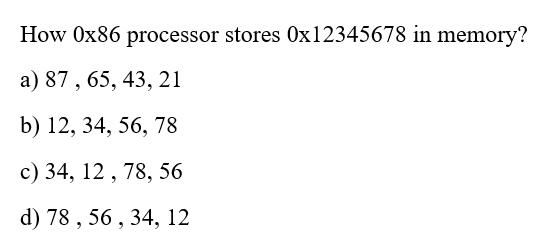
How Ox86 processor stores 0x12345678 in memory? a) 87, 65, 43, 21 b) 12, 34, 56,...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
How Ox86 processor stores 0x12345678 in memory? a) 87, 65, 43, 21 b) 12, 34, 56, 78 c) 34, 12 , 78, 56 d) 78 , 56 , 34, 12 How Ox86 processor stores 0x12345678 in memory? a) 87, 65, 43, 21 b) 12, 34, 56, 78 c) 34, 12 , 78, 56 d) 78 , 56 , 34, 12
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these programming questions
-
How are prices set for computer processor chips? At one time, the frequency was a good indicator of the processing speed; however, more recently manufacturers have developed alternative ways to...
-
1. C and D jointly organized Z corporation. C transfers in property Z in exchange for $500 in cash and 45 shares of Z's stcok. D transfers $500 in cash to Z in exchange for the other half of Z's...
-
A plastic bar of diameter d = 56 mm is to be twisted by torques T (see figure) until the angle of rotation between the ends of the bar is 4.0. If the allowable shear strain in the plastic is 0.012...
-
In Exercises 8486, use a graphing utility to graph f and g in the same [-8, 8, 1] by [-5, 5, 1] viewing rectangle. In addition, graph the line y = x and visually determine if f and g are inverses....
-
Assume the exchange of Schoettler shares for Stevens shares as outlined in Problem 2. a. What is the share exchange ratio? b. Compare the earnings per Stevens share before and after the merger....
-
For the unity feedback system shown in Figure 8.3, where do the following: a. Sketch the root locus. b. Find the value of K that will yield a 10% overshoot. c. Locate all nondominant poles. What can...
-
What is kiting? How can one spot a kiting scheme?
-
Equipment replacement decisions and performance evaluation. Bob Moody manages the Knoxville plant of George Manufacturing. He has been approached by a representative of Darda Engineering regarding...
-
It is your responsibility as team leader to deal with the immediate situation. You are supervising a team of employees preparing for an event/service. You and your colleague overhear a team member...
-
1. What might Lewis have done to avoid the result in this case? Discuss. 2. Suppose that Lewis had already been reimbursed for the two vehicles that had been sold, and Whitney sought to obtain the...
-
Dates do go through the 28th I just could not crop it all.Please help! Thank you Account Debited (a) 9 11 16 20 23 (b) Specific Account (c) Effect IncreaseSelected transactions for M. Acosta, an...
-
The Alpine House, Incorporated, is a large retailer of snow skis. The company assembled the information shown be ended March 31: Sales Selling price per pair of skis. Variable selling expense per...
-
Develop a Health and Safety Plan to address Hazard Assessment, Analysis and Control. The Occupational Health and Safety Act and related regulations set out minimum requirements reflecting accepted...
-
Suppose a phone number, stored as a ten-character string (of digits only) called phoneNumber, must be converted into a string that has parentheses around the area code. Which statement below will do...
-
Forensic Auditing Techniques and Their Application in Managerial Audits 1. Understanding Forensic Auditing: Forensic auditing involves the examination of financial records and transactions to uncover...
-
Simplify 516x11 completely. Write answer in radical form. Assume Answer = Entry Tip: To enter an answer like 50x4x2, type 50x^4*root(3) answer before submitting! Question Help: Message instructor...
-
As part of a grant you are writing, you need to order 25 cases of paper. A company sells paper for $27.30 per case. How much money will you need to request to cover the cost of paper? A. $2.30 B....
-
The following processes constitute the air-standard Diesel cycle: 12: isentropic compression,23: constant-volume energy addition (T and P increase),34: constant-pressure energy addition (v...
-
How should a corporation respond to a large-scale loss of customer data?
-
(a) What is fraud? Be specific. (b) What is click fraud? (c) How do criminals engage in online extortion?
-
a) What is DRM? Give an example of how DRM works. b) Why is DRM desirable? c) Give some examples of use restrictions that a company may wish to impose on a document. d) How can many DRM protections...
-
A lessee is evaluating whether a lease term is a major part of the remaining life of an asset in order to determine the proper lease classification. The lessee leases office space through a lease...
-
On January 1, 2020, Lessee Company leases a vehicle with a fair value of \(\$ 30,000\) from Lessor Company for 3 years, with no renewal options. The estimated life of the vehicle is 6 years and...
-
For each of the following four separate finance lease scenarios, determine the lease payment that the lessee should use to determine the appropriate lease classification. a. Lease payments are \(\$...

Study smarter with the SolutionInn App