Overview A binary search tree is a common tool for storing data that we want to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
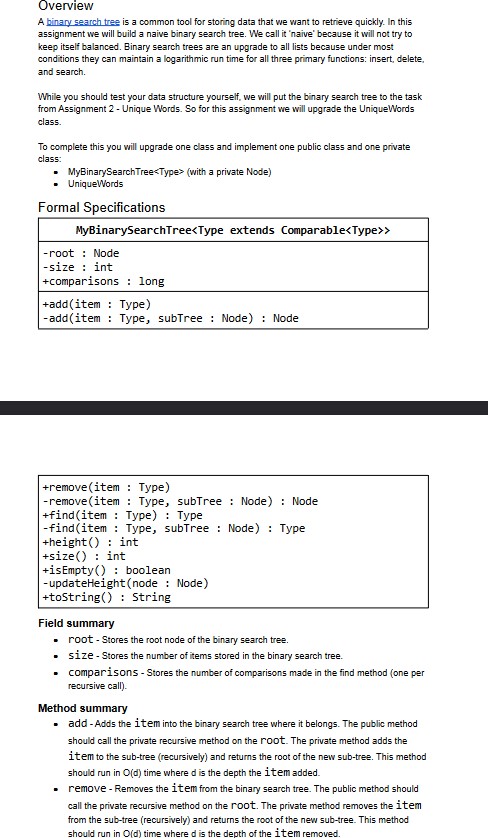
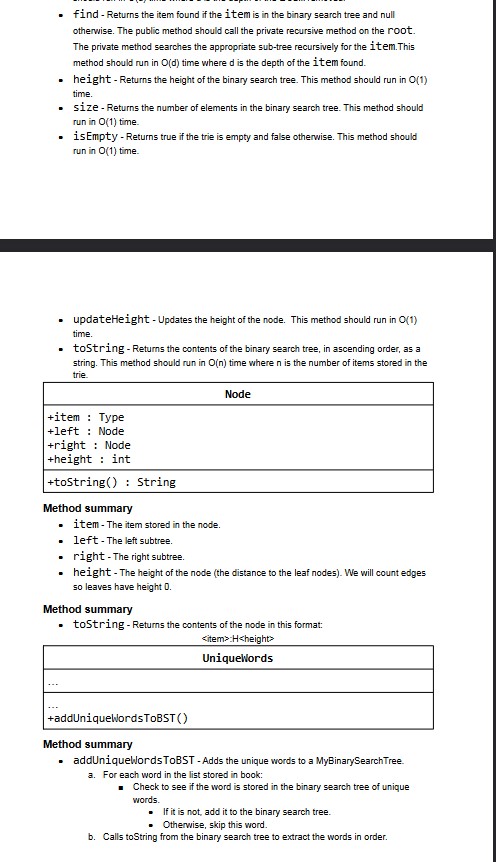
Overview A binary search tree is a common tool for storing data that we want to retrieve quickly. In this assignment we will build a naive binary search tree. We call it 'naive' because it will not try to keep itself balanced. Binary search trees are an upgrade to all lists because under most conditions they can maintain a logarithmic run time for all three primary functions: insert, delete, and search. While you should test your data structure yourself, we will put the binary search tree to the task from Assignment 2 - Unique Words. So for this assignment we will upgrade the Unique Words class. To complete this you will upgrade one class and implement one public class and one private class: ■ MyBinarySearch Tree<Type> (with a private Node) UniqueWords Formal Specifications MyBinarySearchTree<Type extends Comparable<Type>> -rootNode -size: int +comparisons long +add(item Type) -add(item Type, subTreeNode) : Node +remove (item: Type) -remove (item Type, subTree Node) : Node +find(item Type): Type -find(item Type, subTreeNode) : Type +height() int +size() int +isEmpty() boolean. -updateHeight(node: Node) +toString() String Field summary ⚫ root - Stores the root node of the binary search tree. ⚫ size - Stores the number of items stored in the binary search tree. ■ comparisons - Stores the number of comparisons made in the find method (one per recursive call). Method summary ⚫ add - Adds the item into the binary search tree where it belongs. The public method should call the private recursive method on the root. The private method adds the item to the sub-tree (recursively) and returns the root of the new sub-tree. This method should run in O(d) time where d is the depth the item added. ⚫ remove - Removes the item from the binary search tree. The public method should call the private recursive method on the root. The private method removes the item from the sub-tree (recursively) and returns the root of the new sub-tree. This method should run in O(d) time where d is the depth of the item removed. ⚫ find - Returns the item found if the item is in the binary search tree and null otherwise. The public method should call the private recursive method on the root. The private method searches the appropriate sub-tree recursively for the item.This method should run in O(d) time where d is the depth of the item found. height - Returns the height of the binary search tree. This method should run in O(1) time. ⚫ size - Returns the number of elements in the binary search tree. This method should run in O(1) time. ⚫ is Empty - Returns true if the trie is empty and false otherwise. This method should run in O(1) time. . updateHeight - Updates the height of the node. This method should run in O(1) time. ⚫ toString - Returns the contents of the binary search tree, in ascending order, as a string. This method should run in O(n) time where n is the number of items stored in the trie. +item Type +leftNode +right: Node +height: int +toString() String Method summary • item - The item stored in the node. Node ■ left -The left subtree. . right - The right subtree. height - The height of the node (the distance to the leaf nodes). We will count edges so leaves have height 0. Method summary ⚫ toString - Returns the contents of the node in this format: <item>H<height> UniqueWords +addUniqueWordsToBST() Method summary ■ addUniqueWords ToBST - Adds the unique words to a MyBinarySearch Tree. a. For each word in the list stored in book: ■Check to see if the word is stored in the binary search tree of unique words. If it is not, add it to the binary search tree. Otherwise, skip this word. b. Calls toString from the binary search tree to extract the words in order. Overview A binary search tree is a common tool for storing data that we want to retrieve quickly. In this assignment we will build a naive binary search tree. We call it 'naive' because it will not try to keep itself balanced. Binary search trees are an upgrade to all lists because under most conditions they can maintain a logarithmic run time for all three primary functions: insert, delete, and search. While you should test your data structure yourself, we will put the binary search tree to the task from Assignment 2 - Unique Words. So for this assignment we will upgrade the Unique Words class. To complete this you will upgrade one class and implement one public class and one private class: ■ MyBinarySearch Tree<Type> (with a private Node) UniqueWords Formal Specifications MyBinarySearchTree<Type extends Comparable<Type>> -rootNode -size: int +comparisons long +add(item Type) -add(item Type, subTreeNode) : Node +remove (item: Type) -remove (item Type, subTree Node) : Node +find(item Type): Type -find(item Type, subTreeNode) : Type +height() int +size() int +isEmpty() boolean. -updateHeight(node: Node) +toString() String Field summary ⚫ root - Stores the root node of the binary search tree. ⚫ size - Stores the number of items stored in the binary search tree. ■ comparisons - Stores the number of comparisons made in the find method (one per recursive call). Method summary ⚫ add - Adds the item into the binary search tree where it belongs. The public method should call the private recursive method on the root. The private method adds the item to the sub-tree (recursively) and returns the root of the new sub-tree. This method should run in O(d) time where d is the depth the item added. ⚫ remove - Removes the item from the binary search tree. The public method should call the private recursive method on the root. The private method removes the item from the sub-tree (recursively) and returns the root of the new sub-tree. This method should run in O(d) time where d is the depth of the item removed. ⚫ find - Returns the item found if the item is in the binary search tree and null otherwise. The public method should call the private recursive method on the root. The private method searches the appropriate sub-tree recursively for the item.This method should run in O(d) time where d is the depth of the item found. height - Returns the height of the binary search tree. This method should run in O(1) time. ⚫ size - Returns the number of elements in the binary search tree. This method should run in O(1) time. ⚫ is Empty - Returns true if the trie is empty and false otherwise. This method should run in O(1) time. . updateHeight - Updates the height of the node. This method should run in O(1) time. ⚫ toString - Returns the contents of the binary search tree, in ascending order, as a string. This method should run in O(n) time where n is the number of items stored in the trie. +item Type +leftNode +right: Node +height: int +toString() String Method summary • item - The item stored in the node. Node ■ left -The left subtree. . right - The right subtree. height - The height of the node (the distance to the leaf nodes). We will count edges so leaves have height 0. Method summary ⚫ toString - Returns the contents of the node in this format: <item>H<height> UniqueWords +addUniqueWordsToBST() Method summary ■ addUniqueWords ToBST - Adds the unique words to a MyBinarySearch Tree. a. For each word in the list stored in book: ■Check to see if the word is stored in the binary search tree of unique words. If it is not, add it to the binary search tree. Otherwise, skip this word. b. Calls toString from the binary search tree to extract the words in order.
Expert Answer:
Answer rating: 100% (QA)
You can go for this solution Binary Tree in Java Node creation class Node int key Node left right pu... View the full answer

Related Book For 

Introduction to Algorithms
ISBN: 978-0262033848
3rd edition
Authors: Thomas H. Cormen, Charles E. Leiserson, Ronald L. Rivest
Posted Date:
Students also viewed these programming questions
-
Exercise 1 Consider the mass-spring-damper system described by m+c+ky = U where y is the displacement of the mass and u is the force exerted on the mass. 1. Find a minimal state-space realization of...
-
Microkernel operating systems aim to address perceived modularity and reliability issues in traditional "monolithic" operating systems. (i) Describe the typical architecture of a microkernel...
-
resolved first by reducing the raw hash value modulo the size of the array and arranging that each array entry refers to the start of a linked list of (index,value) pairs. Retrieving a value from the...
-
A Contractors Ltd was formed on 1 January 2012 and the following purchases and sales of machinery were made during the first 3 years of operations. Each machine was estimated to last 10 years and to...
-
Refer to the financial information presented in P13.2A for Whistler Ltd., a private company following ASPE. In P13.2A WHISTLER LTD. Income Statement Year Ended November 30, 2018...
-
Two variables have a positive linear correlation. Does the dependent variable increase or decrease as the independent variable increases? What if the variables have a negative linear correlation?
-
Assume that you are responsible for the physical distribution of computers at a web-based company. What would you do to ensure product availability, timely delivery, and quality service for your...
-
1. Calculate the C&F Lisbon price per machine and the CIF Lisbon price per machine. 2. At what point in time, or place, will RAP's responsibilities for arrangements of the shipment end? When does...
-
3) f(x) = x between x = 0 and x = 4 using an upper sum with two rectangles of equal width.
-
Table 1 shows Apple's online orders for the last week. When shoppers place an online order, several "recommended products" (upsells) are shown as at checkout an attempt to upsell See table 2 in cell...
-
99999999999 White Pty Ltd Unadjusted Trial Balance as at 3OJune 2020 Account Debit Credit Cash 12,000 Accounts receivable 68,000 Supplies 18,000 Equipment 1 1 8,000 Accumulated depreciation ?? 1...
-
Consider the $1,474,000 in indirect research and development, human resources, and information technology costs shown in Table 2. Should Wayne's team allocate these costs to the three operating...
-
. Analyze each job advertisement and identify the employability skills each requires: Hint: In being asked to 'analyse' each job advertisement, you are being asked to examine it; take it apart to...
-
The Converting Department of Toren Company had 720 units in work in process at the beginning of the period, which were 30% complete. During the period, 15,200 units were completed and transferred to...
-
This would provide a tangible indication of management's confi- dence in the future. These arguments cut little ice with LA's chief executive. "Ed," she said, "I know that you're the expert on all...
-
Participants will be split into control & treatment based on Costco. They will take a prior survey as to which they prefer (Costco or Grey Goose Vodka). We will then inform the treatment group that...
-
1.What is the product of ? (Round the answer to the nearest ten thousandth.) 2.What is the area of a square that measures on each side? a. b. c. d. 3.A garden in the shape of a square has an area of...
-
g(x) = x 5 5x 6 a. Show that g(x) = 0 has a root, , between x = 1 and x = 2. b. Show that the equation g(x) = 0 can be written as x = (px + q) 1/r , where p, q and r are integers to be found. The...
-
Suppose that the edge weights in a graph are uniformly distributed over the halfopen interval [0, 1]. Which algorithm, Kruskals or Prims, can you make run faster?
-
Is the operation of deletion "commutative" in the sense that deleting x and then y from a binary search tree leaves the same tree as deleting y and then x? Argue why it is or give a counterexample.
-
Prove that the running time of an algorithm is (g (n)) if and only if its worst-case running time is O(g (n)) and its best-case running time is (g (n)).
-
During 2015, Prosperity Oil Company acquired the following leases: In acquiring and exploring these leases, Prosperity Oil Company incurred the following additional costs: Shooting rights, \($3,000\)...
-
Bryant Oil Corporation acquired a lease on October 15, 2015, for \($200,000\) cash. No drilling was done on the lease during the first year. Since Bryant wished to retain the lease, a delay rental of...
-
Railway Oil and Gas Company owned the following unproved property as of the end of 2010: Although no activity took place on Lease A during the year, Railway decided that Lease A was not impaired,...

Study smarter with the SolutionInn App