Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
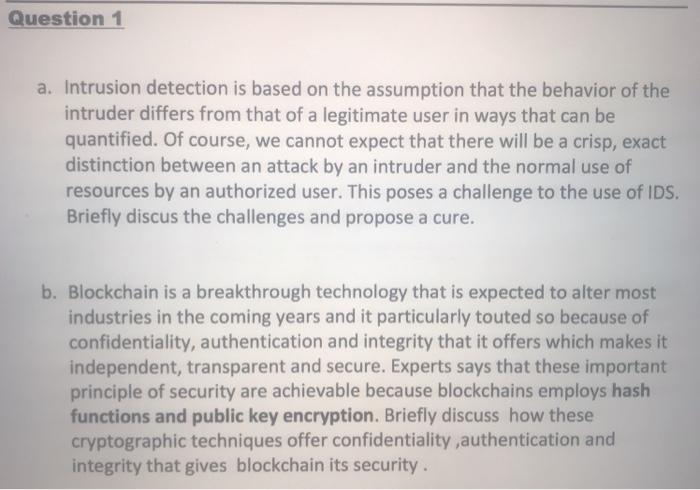
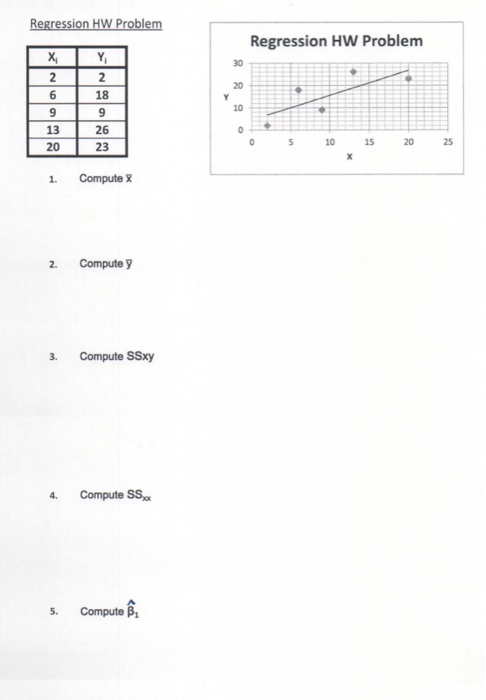
Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25 Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25 Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25
Expert Answer:

Related Book For 

Auditing and Assurance Services A Systematic Approach
ISBN: 978-0077732509
10th edition
Authors: William Messier Jr, Steven Glover, Douglas Prawitt
Posted Date:
Students also viewed these programming questions
-
1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there...
-
1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there...
-
In the previous problem, assume the equity increases by 1,500 solaris due to retained earnings. If the exchange rate at the end of the year is 1.24 solaris per dollar, what does the balance sheet...
-
On July 1, 2016, Apache Company, a real estate developer, sold a parcel of land to a construction company for 53,000,000. The book value of the land on Apache's books was $1,200,000. Terms of the...
-
What are the main elements of an effective enterprise risk management (ERM) framework in the banking sector, and how do they help to mitigate operational and systemic risks ?
-
Which of the following terms describe the types of adjusting entries? a. Deferrals and depreciation b. Expenses and revenues C. Deferrals and accruals d. Prepaid expenses and prepaid revenues
-
During 2015, LeBron Corporation accepts the following notes receivable. a. On April 1, LeBron provides services to a customer on account. The customer signs a four-month, 9% note for $7,000. b. On...
-
In late 2000, AOL and Time Warner announced one of the biggest mergers of the dot-com era - a deal valued at $350 billion. Before the merger, there were high expectations on how the two companies...
-
This problem continues the process of preparing the Kipley Company's Employee Payroll Register for the pay period ending January 8th, 20--. In previous chapters, gross wages were computed for each...
-
two cables are tied together at A and loaded at shows.draw the free body diagram of the setup shown, determine the tension in cable AC if 859 mm is a lenght and 181N , determine the tension in cable...
-
Suppose that a 1-year zero-coupon bond with the face value of $100 currently sells at $94.34, while a 2-year zero sells at $84.99. You are considering the purchase of a 2-year-maturity bond making...
-
What is Weber's definition of the juristic person? What is the role of such a person in Weber's sociology of law?
-
Andrew Buckner earns $ 1 , 6 8 0 per week. He is married and files jointly. What is Andrew's federal income tax? Use the percentage method.
-
How Fiscal Policy does it impact an economy in times of recession? Explain.
-
Salsa Company is considering an investment in technology to improve its operations. The investment costs $250,000 and will yield the following net cash flows. Management requires a 7% return on...
-
4. Give the product of the following reactions and in each case give a detailed reaction mechanism by which it is formed. (50 pts) (a) (e) CH3O H3O+ HO, heat CH C5HO4 + CHN+ (b) NaOH, HO EtOH 1....
-
Find the area of the surface generated by revolving the para- metric curve x = cos 1, y = sin? 1 (0 < I sa/2) about the y-axis.
-
The "Accounts Receivable-Confirmation Statistics" working paper shown on the next page was prepared by an audit assistant for the 2015 audit of Lewis County Water Company, Inc., a continuing audit...
-
Phung, CPA, has been engaged to audit the financial statements of Vernon Distributors, Inc., a continuing audit client, for the year ended September 30. After obtaining an understanding of Vernon's...
-
Distinguish among the three categories of expenses. Provide an example of each type of expense.
-
True or False. For an undamped system, the velocity leads the acceleration by \(\pi / 2\).
-
True or False. Coulomb damping can be called constant damping.
-
True or False. The motion diminishes to zero in both underdamped and overdamped cases.

Study smarter with the SolutionInn App