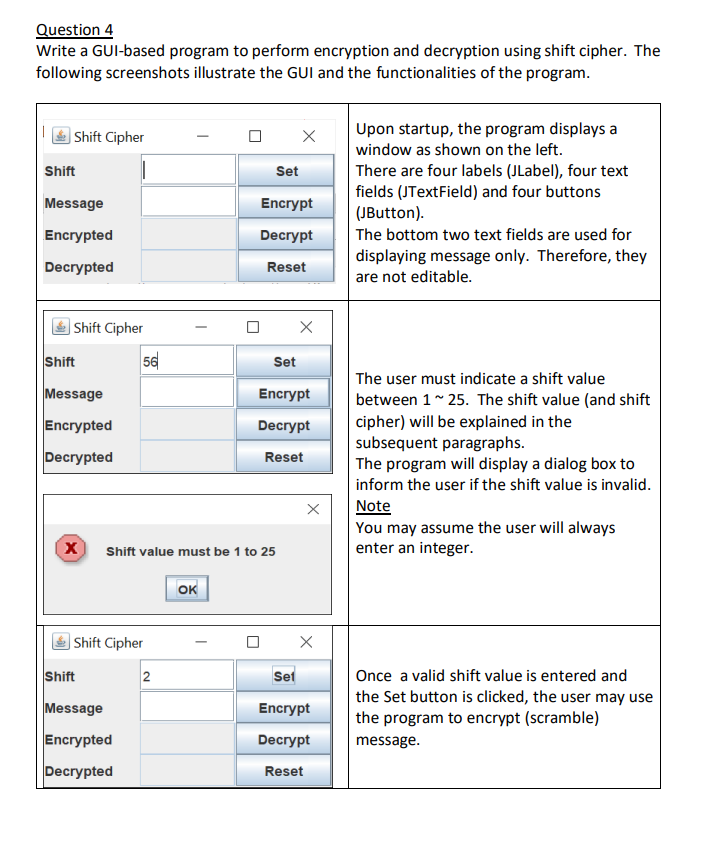
Question 4 Write a GUI-based program to perform encryption and decryption using shift cipher. The following...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
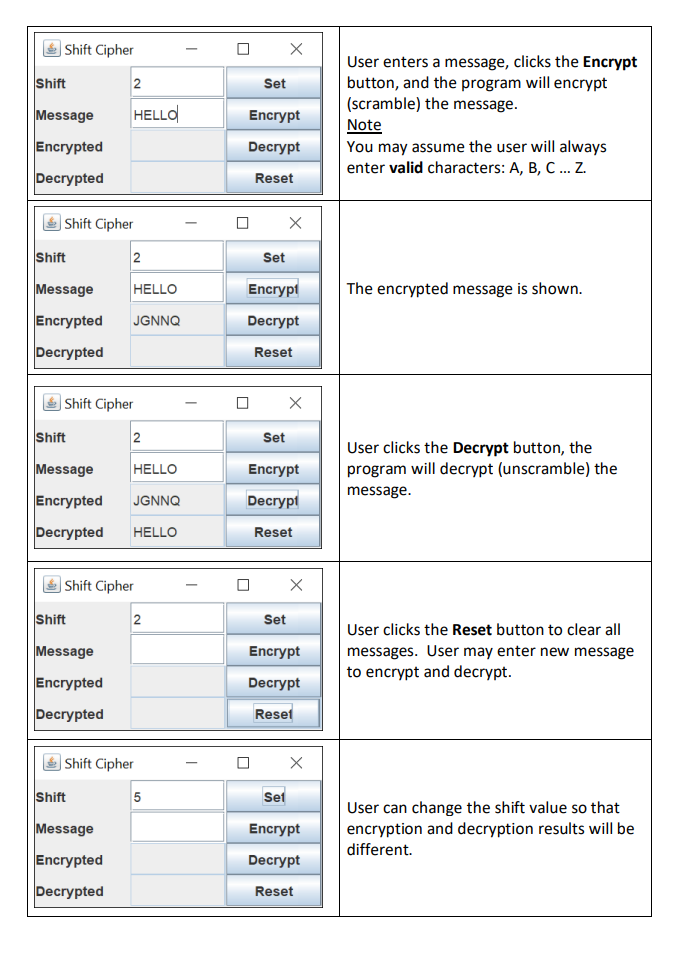
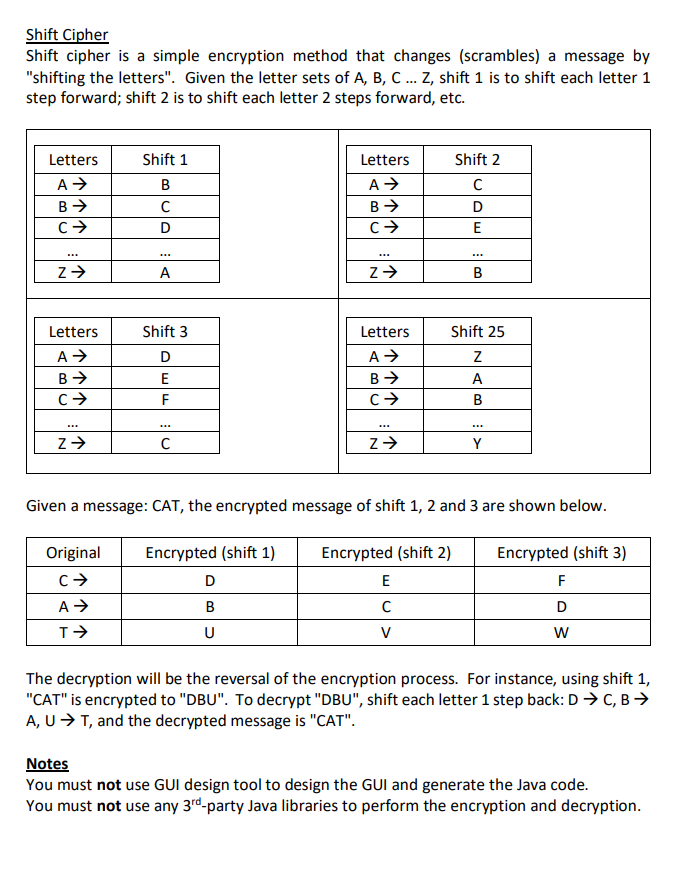
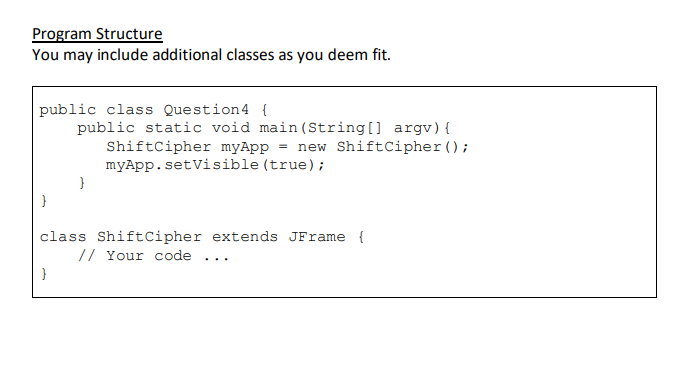
Question 4 Write a GUI-based program to perform encryption and decryption using shift cipher. The following screenshots illustrate the GUI and the functionalities of the program. Shift Cipher Shift Message Encrypted Decrypted Shift Cipher Shift Message Encrypted Decrypted X Shift 56 Shift Cipher Message Encrypted Decrypted Shift value must be 1 to 25 2 OK X Set Encrypt Decrypt Reset X Set Encrypt Decrypt Reset X X Set Encrypt Decrypt Reset Upon startup, the program displays a window as shown on the left. There are four labels (JLabel), four text fields (JTextField) and four buttons (JButton). The bottom two text fields are used for displaying message only. Therefore, they are not editable. The user must indicate a shift value between 1 ~ 25. The shift value (and shift cipher) will be explained in the subsequent paragraphs. The program will display a dialog box to inform the user if the shift value is invalid. Note You may assume the user will always enter an integer. Once a valid shift value is entered and the Set button is clicked, the user may use the program to encrypt (scramble) message. Shift Cipher Shift Message Encrypted Decrypted Shift Shift Cipher Message HELLO Encrypted JGNNQ Decrypted Shift 2 Shift Cipher HELLO 2 Message HELLO Encrypted JGNNQ Decrypted HELLO Shift Message Encrypted Decrypted 2 Shift Cipher Shift Message Encrypted Decrypted Shift Cipher 2 5 Set Encrypt Decrypt Reset X Set Set Encrypt Decrypt Reset X Set X Encrypt Decrypt Reset X Encrypt Decrypt Reset X Set Encrypt Decrypt Reset User enters a message, clicks the Encrypt button, and the program will encrypt (scramble) the message. Note You may assume the user will always enter valid characters: A, B, C... Z. The encrypted message is shown. User clicks the Decrypt button, the program will decrypt (unscramble) the message. User clicks the Reset button to clear all messages. User may enter new message to encrypt and decrypt. User can change the shift value so that encryption and decryption results will be different. Shift Cipher Shift cipher is a simple encryption method that changes (scrambles) a message by "shifting the letters". Given the letter sets of A, B, C... Z, shift 1 is to shift each letter 1 step forward; shift 2 is to shift each letter 2 steps forward, etc. Letters A B C *** Z Letters A B C Z Shift 1 B D Original C A T *** A Shift 3 D E F C Encrypted (shift 1) Letters A B C D B U Z Letters A B C Z Given a message: CAT, the encrypted message of shift 1, 2 and 3 are shown below. Encrypted (shift 2) E C Shift 2 C D E V B Shift 25 Z A B Y Encrypted (shift 3) F D W The decryption will be the reversal of the encryption process. For instance, using shift: "CAT" is encrypted to "DBU". To decrypt "DBU", shift each letter 1 step back: D C, B A, U T, and the decrypted message is "CAT". Notes You must not use GUI design tool to design the GUI and generate the Java code. You must not use any 3rd-party Java libraries to perform the encryption and decryption. Program Structure You may include additional classes as you deem fit. public class Question4 { public static void main (String[] argv) { ShiftCipher myApp = new ShiftCipher (); myApp.setVisible (true); } class Shift Cipher extends JFrame { // Your code } Question 4 Write a GUI-based program to perform encryption and decryption using shift cipher. The following screenshots illustrate the GUI and the functionalities of the program. Shift Cipher Shift Message Encrypted Decrypted Shift Cipher Shift Message Encrypted Decrypted X Shift 56 Shift Cipher Message Encrypted Decrypted Shift value must be 1 to 25 2 OK X Set Encrypt Decrypt Reset X Set Encrypt Decrypt Reset X X Set Encrypt Decrypt Reset Upon startup, the program displays a window as shown on the left. There are four labels (JLabel), four text fields (JTextField) and four buttons (JButton). The bottom two text fields are used for displaying message only. Therefore, they are not editable. The user must indicate a shift value between 1 ~ 25. The shift value (and shift cipher) will be explained in the subsequent paragraphs. The program will display a dialog box to inform the user if the shift value is invalid. Note You may assume the user will always enter an integer. Once a valid shift value is entered and the Set button is clicked, the user may use the program to encrypt (scramble) message. Shift Cipher Shift Message Encrypted Decrypted Shift Shift Cipher Message HELLO Encrypted JGNNQ Decrypted Shift 2 Shift Cipher HELLO 2 Message HELLO Encrypted JGNNQ Decrypted HELLO Shift Message Encrypted Decrypted 2 Shift Cipher Shift Message Encrypted Decrypted Shift Cipher 2 5 Set Encrypt Decrypt Reset X Set Set Encrypt Decrypt Reset X Set X Encrypt Decrypt Reset X Encrypt Decrypt Reset X Set Encrypt Decrypt Reset User enters a message, clicks the Encrypt button, and the program will encrypt (scramble) the message. Note You may assume the user will always enter valid characters: A, B, C... Z. The encrypted message is shown. User clicks the Decrypt button, the program will decrypt (unscramble) the message. User clicks the Reset button to clear all messages. User may enter new message to encrypt and decrypt. User can change the shift value so that encryption and decryption results will be different. Shift Cipher Shift cipher is a simple encryption method that changes (scrambles) a message by "shifting the letters". Given the letter sets of A, B, C... Z, shift 1 is to shift each letter 1 step forward; shift 2 is to shift each letter 2 steps forward, etc. Letters A B C *** Z Letters A B C Z Shift 1 B D Original C A T *** A Shift 3 D E F C Encrypted (shift 1) Letters A B C D B U Z Letters A B C Z Given a message: CAT, the encrypted message of shift 1, 2 and 3 are shown below. Encrypted (shift 2) E C Shift 2 C D E V B Shift 25 Z A B Y Encrypted (shift 3) F D W The decryption will be the reversal of the encryption process. For instance, using shift: "CAT" is encrypted to "DBU". To decrypt "DBU", shift each letter 1 step back: D C, B A, U T, and the decrypted message is "CAT". Notes You must not use GUI design tool to design the GUI and generate the Java code. You must not use any 3rd-party Java libraries to perform the encryption and decryption. Program Structure You may include additional classes as you deem fit. public class Question4 { public static void main (String[] argv) { ShiftCipher myApp = new ShiftCipher (); myApp.setVisible (true); } class Shift Cipher extends JFrame { // Your code }
Expert Answer:
Answer rating: 100% (QA)
import javaxswing import javaawteventActionEvent import javaawteventActionListener import javautilLo... View the full answer

Related Book For 

Data Structures and Algorithms in Python
ISBN: 978-1118290279
1st edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Posted Date:
Students also viewed these programming questions
-
Hamilton company uses job order costing. Factory overhead is applied to production at rate of 150% of direct- labor cost. Any over -orunderapplied factory overhead is closed to the cost of goods sold...
-
Data for Case Study 5.1 Probability Distribution for Repair Cost Type of Repair Probability Repair Cost (in $) None 0.76 Minor 0.13 80 Major 0.08 320 Catastrophic 0.03 500
-
READ THE INSTRUCTIONS AND NO PLAGlARISM FOR THE "BACKGROUND OF THE LITERATURE" YOU MUST USE YOUR 0WN PERSPECTIVE BASE ON WHAT YOU UNDERSTAND ON THE CHOSEN LITERATURE C. Types of Literature 1. Oral...
-
Reverse the order of integration in the following integrals. S.S. f(x, y) dx dy 0 1
-
A closed-loop system has a loop transfer function (a) Determine the gain K so that the phase margin is 60°. (b) For the gain K selected in part (a), determine the gain margin of the system. LS)...
-
Write an SQL statement to display the WarehouseID and the sum of QuantityOnHand grouped by WarehouseID. Omit all SKU items that have 3 or more items on hand from the sum, and name the sum...
-
Variable and fixed cost pattern analysis} The cost behavior patterns graphed on page 193 are lettered A through H. The vertical axes of the graphs represent total dollars of expense, and the...
-
On April 30, the bank reconciliation of Westbrook Company shows three outstanding checks: no. 254, $650; no. 255, $620; and no. 257, $410. The May bank statement and the May cash payments journal...
-
The assets and liabilities of Thompson Computer Services at March 3 1 , the end of the current year, and its revenue and expenses for the year follow. The common stock was $ 1 2 0 , 0 0 0 and the...
-
What is the value of CP's revised offer on December 8 (before CP "sweetened" its offer by adding the CVR security)? In your analysis, assume the following: a) A valuation date of December 31, 2015,...
-
Find the monthly payment necessary to amortize the following home mortgages. $314,900, 6 3/4%, 15 years
-
Question 3: Your good friend Roger has just been offered a job with Rightmove but knows very little about accounting. Please write a report to Roger analysing the latest financial position and...
-
The molecule shown below is Efavirenz, which is a reverse transcriptase inhibitor drug used for the treatment of HIV infection. In this question we will explore some of the chemistry that occurs...
-
How does process modeling contribute to the optimization of complex industrial systems, and what methodologies are typically employed to represent and simulate these processes ?
-
I have arranged to borrow $11,000 from my parents toward a holiday. I will repay the loan over 3 years in equal year-end payments. If the interest rate is 14.3% p.a. compounding monthly, my annual...
-
"Sales increased by 20%, so cash inflows must also have increased by 20%." Do you agree with this statement? Why or why not?
-
eBook Pearson Motors has a target capital structure of 40% debt and 60% common equity, with no preferred stock. The yield to maturity on the company's outstanding bonds is 9%, and its tax rate is...
-
a) Calculate the goodwill that was paid by Major Ltd on the acquisition of Minor Ltd. [10 marks] b) Prepare the consolidated statement of financial position for Major Ltd at 31 July 20X8. [30 marks]...
-
Write a short Python function that takes a sequence of integer values and determines if there is a distinct pair of numbers in the sequence whose product is odd.
-
Write a Python program that can simulate a simple calculator, using the console as the exclusive input and output device. That is, each input to the calculator, be it a number, like 12.34 or 1034, or...
-
Consider a situation in which a user has numeric keys and wishes to have a priority queue that is maximum-oriented. How could a standard (minoriented) priority queue be used for such a purpose?
-
Talias Tutus bought a new sewing machine for $40,000 that will be depreciated using the MACRS depreciation schedule for a 5-year recovery period. a. Find the depreciation charge each year. b. If the...
-
Sec uses 60 000 tons of salt over a 50-week working year. It costs 100 to order salt and delivery follows two weeks later. Storage costs for the salt are expected to be 0.10 per ton per year. The...
-
Calculate the following values assuming a discount rate of 12 per cent: (a) 500 compounded for five years; (b) the present value of 500 to be received in five years time; (c) the present value of 500...

Study smarter with the SolutionInn App


