You suspect that there's a spy within your group. In order to avoid precious information to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
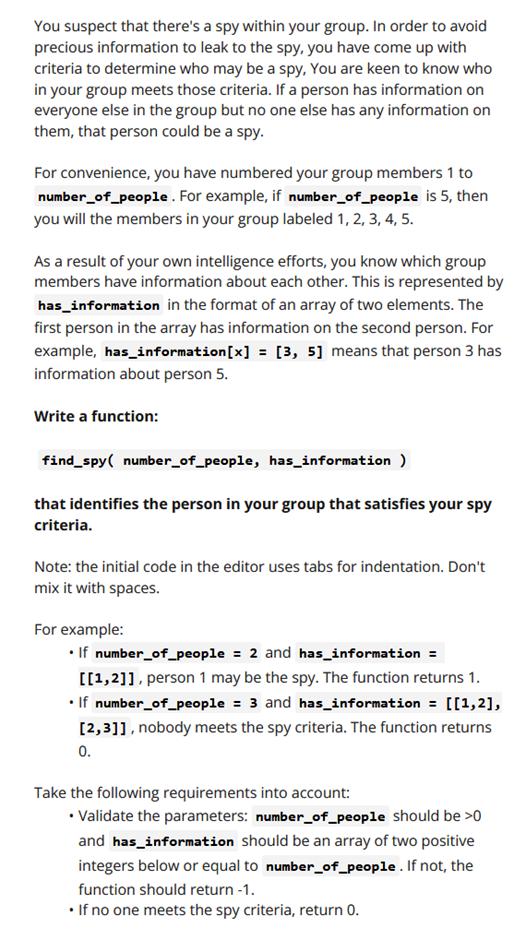
You suspect that there's a spy within your group. In order to avoid precious information to leak to the spy, you have come up with criteria to determine who may be a spy, You are keen to know who in your group meets those criteria. If a person has information on everyone else in the group but no one else has any information on them, that person could be a spy. For convenience, you have numbered your group members 1 to number_of_people. For example, if number_of_people is 5, then you will the members in your group labeled 1, 2, 3, 4, 5. As a result of your own intelligence efforts, you know which group members have information about each other. This is represented by has_information in the format of an array of two elements. The first person in the array has information on the second person. For example, has_information[x] = [3, 5] means that person 3 has information about person 5. Write a function: find_spy number_of_people, has_information ) that identifies the person in your group that satisfies your spy criteria. Note: the initial code in the editor uses tabs for indentation. Don't mix it with spaces. For example: If number_of_people = 2 and has_information = [[1,2]], person 1 may be the spy. The function returns 1. If number_of_people = 3 and has_information = [[1,2], [2,3]], nobody meets the spy criteria. The function returns 0. Take the following requirements into account: Validate the parameters: number_of_people should be >0 and has_information should be an array of two positive integers below or equal to number_of_people. If not, the function should return -1. If no one meets the spy criteria, return 0. You suspect that there's a spy within your group. In order to avoid precious information to leak to the spy, you have come up with criteria to determine who may be a spy, You are keen to know who in your group meets those criteria. If a person has information on everyone else in the group but no one else has any information on them, that person could be a spy. For convenience, you have numbered your group members 1 to number_of_people. For example, if number_of_people is 5, then you will the members in your group labeled 1, 2, 3, 4, 5. As a result of your own intelligence efforts, you know which group members have information about each other. This is represented by has_information in the format of an array of two elements. The first person in the array has information on the second person. For example, has_information[x] = [3, 5] means that person 3 has information about person 5. Write a function: find_spy number_of_people, has_information ) that identifies the person in your group that satisfies your spy criteria. Note: the initial code in the editor uses tabs for indentation. Don't mix it with spaces. For example: If number_of_people = 2 and has_information = [[1,2]], person 1 may be the spy. The function returns 1. If number_of_people = 3 and has_information = [[1,2], [2,3]], nobody meets the spy criteria. The function returns 0. Take the following requirements into account: Validate the parameters: number_of_people should be >0 and has_information should be an array of two positive integers below or equal to number_of_people. If not, the function should return -1. If no one meets the spy criteria, return 0.
Expert Answer:

Related Book For 

Managerial accounting
ISBN: 978-0471467854
1st edition
Authors: ramji balakrishnan, k. s i varamakrishnan, Geoffrey b. sprin
Posted Date:
Students also viewed these operating system questions
-
3. Where would you go on campus to dormir? Responses a. la residencia estudiantil a. la residencia estudiantil b. el saln b. el saln c. de clasesel gimnasio
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
Again review information about your own university. Create generalization/specialization hierarchies using the domain model class diagram notation for (1) Types of faculty, (2) Types of students, (3)...
-
In the market for flash memory drives (a normal good), explain whether the following events would cause an increase or a decrease in demand or an increase or a decrease in the quantity demanded. Also...
-
To tell the current memory allocation of a MINIX 3 process you can use the command chmem +0 a.out but this has the annoying side effect of rewriting the file, and thus changing its date and time...
-
You want to save \($2,000\) for college by working over the summer. You can fi nd a job that will pay you for 40 hours per week at regular rates plus an average of 10 hours per week at overtime rates...
-
1. Identify possible actors and use cases involved in Personal Trainers operations. 2. Create an object relationship diagram for the Personal Trainer information system. 3. Create a use case diagram...
-
Please help.Thank you. Yamato's Big Peace Chocolate purchases and sells chocolates to malls, local stores, and other customers in the Pacific Rim. They only sell chocolates and have different kinds...
-
Your uncle's company is considering financing for its new office building. He has asked you to help him select the bank, based on the terms they are offering. Bank A has offered to lend the required...
-
Give examples of mergers of the vertical, horizontal and conglomerate types. Use your own examples and explain why in each case. In what situations would a merger be a good idea? Why are the fixed...
-
What is a legal Issue as it relates to the process of legal analysis? How important do you think it is to identify and create the legal issue or Question Presented compared to the other components of...
-
1. Describe the issue the company is facing 2. Calculate the costs for the four favors using ABC, reproduce the income statement, and calculate the new profit margin for each flavor 3. Compare the...
-
Show that f(x) = 2000x4 and g(x) = 200x4 grow at the same rate.
-
The process that every adult performs, seeking to maximize gains and minimize losses, practicing some abilities and ignoring others is known as:?
-
Mr Jones, married, 6 6 spouse\'s NIFTP ( earned ) $ 7 , 6 0 0 spouse\'s age 5 8 2 0 2 3 Gross salary $ 4 1 , 2 5 0 CPP contributions $ 2 , 2 4 6 EI premiums $ 1 , 1 7 6 Employee RPP contributions $ 1...
-
Extend Algorithms 3.4 and 3.5 to include as output the first and second derivatives of the spline at the nodes.
-
Randy Quench manages the Science Station in Lansing, Michigan. One of the stations key attractions is a big-screen IMAX theater. As stated in the IMAX Web site, The IMAX experience is the worlds most...
-
Bruce Jaffee, the wholesaler of spices from the previous exercise, purchases most of his products on credit; he estimates that he pays 60% of his accounts payable in the month of purchase, 30% in the...
-
Frans Custom Motors uses a job-order costing system. The firm had two jobs in process at the start of the April: job no. 401 (cost : $211,250) and job no. 402 (cost: $53,400). The following...
-
Puffin Industries acquired 90 percent of Sunset Coast Digitals stock on January 1, 2014, for \($3,150,000.\) At that time, Sunset Coasts stockholders equity totaled \($1,400,000,\) and the estimated...
-
Bottling Company acquired a 75 percent interest in Regional Bottling Partnership on January |, 2008. Assume the following information related to this acquisition: The excess of fair value over book...
-
Comparative consolidated balance sheets and the intervening income statement for Prime Casinos and its subsidiary Saratoga International Hotels are shown below: Additional information (in millions):...

Study smarter with the SolutionInn App