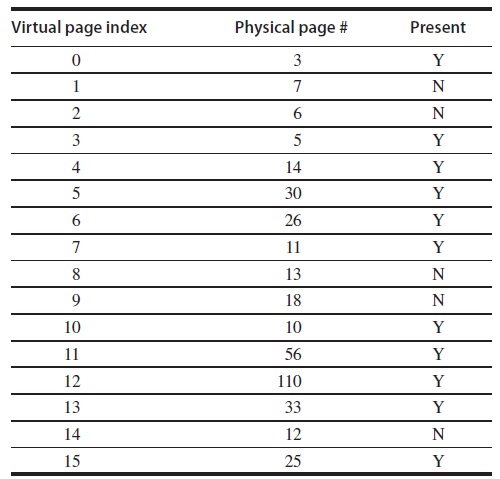
A program is running on a computer with a four-entry fully associative (micro) translation lookaside buffer (TLB):
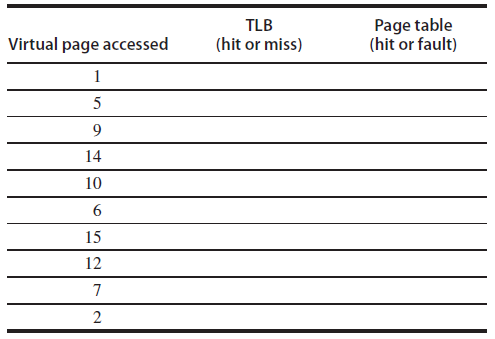
Question:
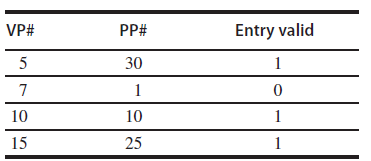
The following is a trace of virtual page numbers accessed by a program. For each access indicate whether it produces a TLB hit/miss and, if it accesses the page table, whether it produces a page hit or fault. Put an X under the page table column if it is not accessed.
Transcribed Image Text:
VP# PP# Entry valid 5 30 10 10 15 25 Virtual page index Physical page # Present 3 3 5 4 14 5 30 26 11 13 18 10 10 11 56 12 110 13 33 14 12 15 25 2. 1,
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 54% (11 reviews)
VP 5 7 10 15 PP 30 1 10 25 Entry Valid 1 0 1 1 Virtual Page Index 0 1 2 3 4 5 ...View the full answer

Answered By

Benish Ahmad
I'm a professional software engineer. I'm lectutrer at GCUF and I have 3 years of teaching experience. I'm looking forward to getting mostly computer science work including:
Programming fundamentals
Object oriented programming
Data structures
object oriented design and analysis
Database system
Computer networks
Discrete mathematics
Web application
I am expert in different computer languages such as C++, java, JavaScript, Sql, CSS, Python and C#. I'm also have excellent knowledge of essay writing and research. I have worked in other Freelancing website such as Fiverr and Upwork. Now I have finally decided to join the SolutionInn platform to continue with my explicit work of helping dear clients and students to achieve their academic dreams. I deliver plagiarism free work and exceptional projects on time. I am capable of working under high pressure.
5.00+
2+ Reviews
10+ Question Solved
Related Book For 

Computer Architecture A Quantitative Approach
ISBN: 978-8178672663
5th edition
Authors: John L. Hennessy, David A. Patterson
Question Posted:
Students also viewed these Computer science questions
-
Consider the following program. #define Size 64 int A[Size; Size], B[Size; Size], C[Size; Size]; int register i, j; for (j = 0; j < Size; j ++) for (i = 0; i < Size; i++) C[i; j] = A[i; j] + B[i; j];...
-
As described in Section 5.7, virtual memory uses a page table to track the mapping of virtual addresses to physical addresses. This exercise shows how this table must be updated as addresses are...
-
An application program is executed on a nine-computer cluster. A benchmark program takes time T on this cluster. Further, 25% of T is time in which the application is running simultaneously on all...
-
Which is found in the java.sql package that come with the standard JDK? A. Only DerbyDriver B. Only MySqlDriver C. Only OracleDriver D. DerbyDriver, MySqlDriver, OracleDriver E. Only DerbyDriver and...
-
At the beginning of the year, Cully Company had 400 units with a cost of $4 per unit in its beginning inventory. The following inventory transactions occurred during the month of January: Jan. 3...
-
Beths Supplies manufactures building tiles in one plant, which has a practical capacity of 25,000 tiles. The variable cost of the tile is $9.00 per unit, and the fixed costs of the plant are $300,000...
-
How should a capital expenditure be recorded? a. Debit capital b. Debit an expense C. Debit a liability d. Debit an asset
-
Peak Entertainment acquires 60 percent of its subsidiary Saddlestone Inc. on January 1,2013. In preparing to consolidate Peak and Saddlestone at December 31,2013, we assemble the following...
-
Give an example of two securities, one issued by a financial institution and another held as an asset by the same financial institution, that reflect intermediation.
-
Henriksen AS manufactures and sells packaging machines. It recently used an activity based approach to refine the job-costing system at its Vejle plant. The resulting job-costing system has one...
-
Excluding some instructions from entering the cache can reduce conflict misses. a. Sketch a program hierarchy where parts of the program would be better excluded from entering the instruction cache....
-
Some memory systems handle TLB misses in software (as an exception), while others use hardware for TLB misses. a. What are the trade-offs between these two methods for handling TLB misses? b. Will...
-
Compute \(x\).hashCode() \% 5 for the single-character strings E A S Y Q U E S T I O N In the style of the drawing in the text, draw the hash table created when the \(i\) th key in this sequence is...
-
S Based on MD5 hash function, if the input is "Under the PRISM program, which started NSA gathers Internet communications from foreign targets from nine major U.S. Internet-based communication ervice...
-
Common Stock ( $ 2 0 par value, 5 0 , 0 0 0 shares issued and outstanding ) Paid - in Capital in Excess of Par - Common Stock Retained Earnings On January 1 , 2 0 2 2 , Cullumber Company had the...
-
Under what circumstances do you think a company would seek private debt ( soliciting from a single party ) rather than public debt ( an open - to - the - public issuance, like a bond ) ?
-
For any string w, let contract(w) denote the string obtained by collapsing each maximal substring of equal symbols to one symbol. For example: contract(010101) = 010101 contract(001110) = 010...
-
Air enters the compressor of an air-standard Brayton cycle with a volumetric flow rate of 60 m3/s at 0.8 bar, 280 K. The compressor pressure ratio is 17.5, and the maximum cycle temperature is 1950...
-
Consider the rock-on-a-string accelerometer in Figure 4.30. What is the accelerometer angle if the airplane has a horizontal acceleration of 1.5 m/s 2 ? Figure 4.30 mg mg T cos 8 -T sin0 mg
-
1. True or False. Pitfalls to consider in a statistical test include nonrandom samples, small sample size, and lack of causal links. 2. Because 25 percent of the students in my morning statistics...
-
A directory controller can send invalidates for lines that have been replaced by the local cache controller. To avoid such messages and to keep the directory consistent, replacement hints are used....
-
One performance optimization commonly used is to pad synchronization variables to not have any other useful data in the same cache line as the synchronization variable. Construct a pathological...
-
The memory consistency model provides a specification of how the memory system will appear to the programmer. Consider the following code segment, where the initial values are a. At the end of the...
-
Consider the following piecewise-defined function. -x+2x-6 if x 4 f(x) = if x > 6 Step 1 of 3: Evaluate this function at x = 7. Express your answer as an integer or simplified fraction. If the...
-
How do contemporary management concepts, such as agile methodologies and transformational leadership, contribute to effective leadership in today\'s rapidly changing business environment?
-
Verify the identity. (1+sinx) (1-sinx)=cos^(2)x

Study smarter with the SolutionInn App