In a transposition cipher the encryption and decryption keys are often represented as two one-dimension tables (arrays)
Question:
In a transposition cipher the encryption and decryption keys are often represented as two one-dimension tables (arrays) and the cipher is represented as a piece of software (a program).
a. Show the array for the encryption key in Figure 31.6 in the text.
b. Show the array for the decryption key in Figure 31.6 in the text.
Figure 31.6
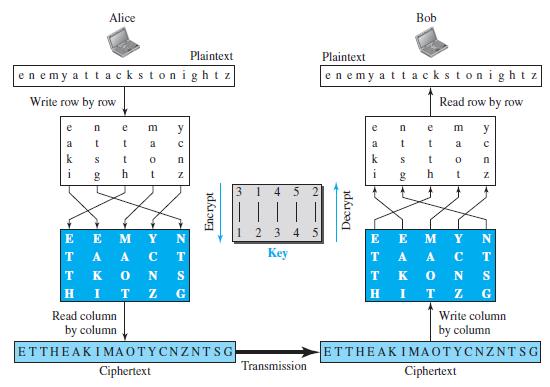
c. Explain, given the encryption key, how we can find the decryption key.
Transcribed Image Text:
Alice Bob Plaintext Plaintext enemy attackstonightz enemy attackstonight z Write row by row Read row by row e e m y m y a a a k k h i h 3. 4 5 123 4 5 E E TA A T K E E M T Кey A A. S T. K H G Read column Write column by column by column ETTHEAKIMAOTYCNZNTSG ETTHEAK IMAOTYCNZNTSG Transmission Ciphertext Ciphertext Z N OT Decrypt Encrypt NZ
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 87% (16 reviews)
The content of each element represents the input col...View the full answer

Answered By

Hassan Imtiaz
The following are details of my Professional Experience. Responsibilities Eight years of demanding teaching experience in the field of finance and business studies at Master’s Level. Completion of the given tasks within given time with quality and efficiency. Marketing professional with practical experience in and solid understanding of a diverse range of management applications, including market analysis, sales and marketing, team building and quality assurance. I have excellent skills to approach deal and sustain corporate clients / customers by demonstrating not only extraordinary communication and interpersonal skills but also high caliber presentation, negotiation and closing skills. Manage and follow up the day-to-day activities. Manage and co-ordinate the inventories. Fulfillment of all the tasks assigned.
The following are details of my Areas of Effectiveness. Finance 1. Corporate Finance 2. Advanced Corporate Finance 3. Management of Financial Institutions 4. International Financial Management 5. Investments 6. Fixed Income 7. Real Estate Investment 8. Entrepreneurial Finance 9. Derivatives 10. Alternative Investments 11. Portfolio Management 12. Financial Statement Analysis And Reporting (US GAAP & IFRS) 13. International Financial Markets 14. Public Finance 15. Personal finance 16. Real estate 17. Financial Planning Quantitative Analysis 1. Time Value Of Money 2. Statistics 3. Probability Distribution 4. Business Statistics 5. Statistical Theory and Methods Economics 1. Principles of Economics 2. Economic Theory 3. Microeconomic Principles 4. Macroeconomic Principles 5. International Monetary Economics 6. Money and Banking 7. Financial Economics 8. Population Economics 9. Behavioral Economics International Business 1. Ethics 2. Business Ethics 3. An introduction to business studies 4. Organization & Management 5. Legal Environment of Business 6. Information Systems in Organizations 7. Operations Management 8. Global Business Policies 9. Industrial Organization 10. Business Strategy 11. Information Management and Technology 12. Company Structure and Organizational Management Accounting & Auditing 1. Financial Accounting 2. Managerial Accounting 3. Accounting for strategy implementation 4. Financial accounting 5. Introduction to bookkeeping and accounting Marketing 1. Marketing Management 2. Professional Development Strategies 3. Business Communications 4. Business planning 5. Commerce & Technology Human resource management 1. General Management 2. Conflict management 3. Leadership 4. Organizational Leadership 5. Supply Chain Management 6. Law 7. Corporate Strategy Creative Writing 1. Analytical Reading & Writing Other Expertise 1. Risk Management 2. Entrepreneurship 3. Management science 4. Organizational behavior 5. Project management 6. Financial Analysis, Research & Companies Valuation 7. And any kind of Excel Queries
4.80+
150+ Reviews
230+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Alice and Bob exchange confidential messages. They share a very large number as the encryption and decryption key in both directions. Is this an example of symmetric-key or asymmetric-key...
-
A general program to implement transposition cipher (encryption and decryption). The input to the program is a flag that demands encryption or decryption, the symmetric key, and the plaintext or...
-
A general program to implement substitution (additive) cipher (encryption and decryption). The input to the program is a flag that demands encryption or decryption, the symmetric key, and the...
-
Perform computational experiments to verify that the average path length in a ring graph on \(V\) vertices is \(\sim 1 / 4 V\). Then, repeat these experiments, but add one random edge to the ring...
-
Differentiate between ordinary and subliminal advertising using examples to illustrate.
-
Kyla and Joan are classmates analyzing the same set of data. There are two nominal independent variables and one interval-level dependent variable. Kyla chooses to conduct a two-way ANOVA, while Joan...
-
What insights into the role of information in management control do the different perspectives outlined in the chapter give? To what extent do you consider them to be complementary or competing?
-
Sentry Transport Inc. of Atlanta provides in-town parcel delivery services in addition to a full range of passenger services. Sentry engaged in the following activities during the current year: a....
-
onsider the geometric and traffic characteristics shown below. North South East West Approach (Width) (56 ft) (56 ft) (68 ft) (68 ft) Peakhour Approach Volumes Left Turn 133 73 168 134 Through...
-
Evaluate R eq looking into each set of terminals for each of the circuits shown in Fig. 2.103 . a. b. 62 ww- 3 k2 2 k2 6 k2 ww 6 k2
-
In a cipher, all As in the plaintext have been changed to Ds in the ciphertext and all Ds in the plaintext have been changed to Hs in the ciphertext. Is this a monoalphabetic or polyalphabetic...
-
Distinguish between a substitution cipher and a transposition cipher.
-
If MTTF represents the Mean Time to Failure, what Greek letter is used to represent the frequency of MTTF ?
-
How did the Blackberry Panic of 2008 help or hinder the financial crisis? How were these two things intertwined? Was it the failing of one that lead the other? Include at least 5 scholarly apa...
-
Following difficult trading conditions in the Eurozone, Unique has seen an increase in demand for its range of Truffles. It has determined that at current prices, the demand for its ginger, cranberry...
-
Regarding the case study: " Tie Declared In Battle Over Navistar Retiree Benefits" December 18, 1992|By Stephen Franklin 1. Who is most severely affected by rising employee healthcare costs?...
-
Pertaining to the benefits and disadvantages of organizational structures, organizational structure, and span of control? Do you have any recommendations for a new organizational structure? Is there...
-
how to find a Financial ratio analysis for Kohl's Kohls: https://docs.google.com/spreadsheets/d/e/2PACX-1vRx4OVmi8-8k3p80UzDWqjymuwehiIZJwd6Jc-p1z4MGq1W0WZRnPj9BQSRq_nAjQqHYXcqaU6VkTJi/pubhtml
-
Use the substitution in Exercise 59 to transform the integrand into a rational function of t and then evaluate the integral. 1 /2 dx /3 1 + sin os x
-
Marc Company assembles products from a group of interconnecting parts. The company produces some of the parts and buys some from outside vendors. The vendor for Part X has just increased its price by...
-
State whether each of the following is true or false. If false, explain why. a) An algorithm is a procedure for solving a problem in terms of the actions to execute and the order in which these...
-
Write four different C# statements that each add 1 to int variable x.
-
Write C# statements to accomplish each of the following tasks: a) Assign the sum of x and y to z, and increment x by 1 with ++. Use only one statement and ensure that the original value of x is used...
-
Dr. Minn is selling her physical therapy practice after owning the practice for 20 years. Dr. Linn is going to buy the radiology practice at a higher price because Dr. Minn has over 500 patients and...
-
Dr. Tier owns a non-profit agency in the local community that provides food, shelter, and counseling for disadvantaged youth and families. At the end of the year, the non-profit agency's difference...
-
Comparative financial statements for Weller Corporation, a merchandisi ompany, for the year ending December 31 appear below. The company did not issue any new common stock during the year. A total of...

Study smarter with the SolutionInn App


