If the processor has forwarding, but we forgot to implement the hazard detection unit, what happens when
Question:
If the processor has forwarding, but we forgot to implement the hazard detection unit, what happens when this code executes?
This exercise is intended to help you understand the relationship between forwarding, hazard detection, and ISA design. Problems in this exercise refer to the following sequences of instructions, and assume that it is executed on a 5-stage pipelined datapath: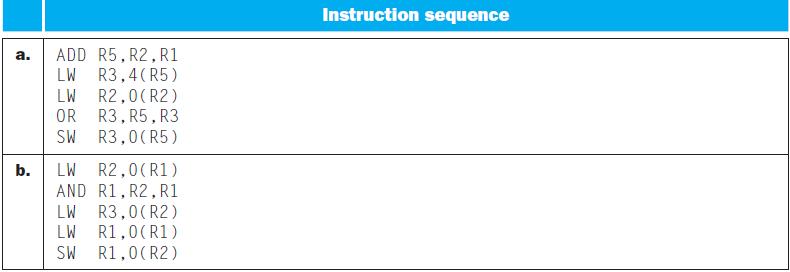
Transcribed Image Text:
a. b. ADD R5, R2, R1 LW R3,4 (R5) LW R2,0(R2) R3, R5, R3 OR SW R3,0(R5) LW R2,0 (R1) AND R1, R2, R1 LW R3,0(R2) LW R1,0 (R1) R1,0 (R2) SW Instruction sequence
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (3 reviews)
In a 5stage pipelined processor the stages typically include Instruction Fetch IF Instruction Decode ID Execute EX Memory Access MEM and Write Back WB ...View the full answer

Answered By

Shubhradeep Maity
I am an experienced and talented freelance writer passionate about creating high-quality content. I have over five years of experience working in the field and have collaborated with several renowned companies and clients in the SaaS industry.
At Herman LLC, an online collective of writers, I generated 1,000+ views on my content and created journal content for 100+ clients on finance topics. My efforts led to a 60% increase in customer engagement for finance clients through revamping website pages and email interaction.
Previously, at Gerhold, a data management platform using blockchain, I wrote and published over 50 articles on topics such as Business Finance, Scalability, and Financial Security. I managed four writing projects concurrently and increased the average salary per page from $4 to $7 in three months.
In my previous role at Bernier, I created content for 40+ clients within the finance industry, increasing sales by up to 40%.
I am an accomplished writer with a track record of delivering high-quality content on time and within budget. I am dedicated to helping my clients achieve their goals and providing exceptional results.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Computer Organization And Design The Hardware Software Interface
ISBN: 9780123747501
4th Revised Edition
Authors: David A. Patterson, John L. Hennessy
Question Posted:
Students also viewed these Computer science questions
-
This exercise is intended to help you understand the relationship between forwarding, hazard detection, and ISA design. Problems in this exercise refer to the following sequence of instructions, and...
-
This exercise is intended to help you understand the relationship between delay slots, control hazards, and branch execution in a pipelined processor. In this exercise, we assume that the following...
-
This exercise is intended to help you understand the cost/complexity/ performance trade-off s of forwarding in a pipelined processor. Problems in this exercise refer to pipelined datapaths from...
-
This case will enable you to practice conducting planning and substantive analytical procedures for accounts in the revenue cycle. When analyzing the financial data, you may assume that the 2015...
-
Gruppa, Inc., has just set up a formal line of credit of $10 million with First Community Commercial Bank. The line of credit is good for up to five years. The bank will charge Gruppa an interest...
-
San Francisco, the city in which Prim launched, has several innovative laundry services. These services include LaundryLocker, where you drop your clothes in a public locker; Sfwash, a delivery...
-
What are trend percentages and how are they calculated? What pitfalls must financial statement users avoid when preparing trend percentages?
-
Felix & Co. reports the following information about its sales and cost of sales. Draw an estimated line of cost behavior using a scatter diagram, and compute fixed costs and variable costs per unit...
-
The number of heart surgeries performed at Heartville General Hospital has increased steadily over the past several years. The hospital's administration is seeking the best method to forecast the...
-
What is the register number supplied to the register files Write register input? Is this register actually written? In this exercise we examine the operation of the single-cycle datapath for a...
-
If energy reduction is paramount, how would you change the pipelined design? What is the percentage reduction in the energy spent by an LW instruction after this change? This exercise explores energy...
-
A small residence has a domestic hot water load of 105 gal/day at a 90F temperature rise. A solar system at the location of the residence can collect, store, and deliver about 1350 Btu/day per square...
-
When making forecasts and analysing the results of a firm, increasing one variable usually means decreasing another. List three of the several possible common trade-offs that should be considered in...
-
A train has a maximum speed of 105 km/h. If the train takes 64 seconds to slow down from maximum speed to a complete stop, how much distance does it cover during this process? Provide your answer in...
-
A student with a mass of 59 kg is standing on the moon. The mass of the moon is 7.35 x 1022 kg and the radius of the moon is 1.737 x 106 m. Calculate the magnitude of the gravitational force, in...
-
Lee's management intends to continue raising 40% of its funds from debt, 10% from preferred equity, and the remainder from common equity.Given this information, and your calculations above, estimate...
-
A circular plane, with a radius of 2.2 m, is immersed in an E-Field with a magnitude of 800 N/C. The field makes an angle of 20 with the plane. What is the magnitude of the flux through the plane?...
-
The scatterplot shows the median annual pay for college-educated men and women in the 50 states in 2005, according to the U.S. Census Bureau. The correlation is 0.834. The regression equation is...
-
Don Griffin worked as an accountant at a local accounting firm for five years after graduating from university. Recently, he opened his own accounting practice, which he operates as a corporation....
-
Repeat Example 25.4 using the service of TCP.
-
You know that the IP address of a computer is 23.14.76.44. Write a statement in Java to create an InetAddress object associated with this address.
-
Why do you think that Java uses an instance of a class instead of just an integer to represent an IP address?
-
You would like to have $7,000.00 in 13 years for a special vacation following graduation by making deposits at the end of each year in an annuity that pays 3.9% compounded annually. How much money...
-
Savings Borrowing Interest rate of China 7% 10% Interest rate of USA 5% 7% USD/CNY Bid Ask Today's spot rate 6.7 6.9 Forward rate (1 year later) 6.4 6.6 What is the profit or loss if you borrow...
-
Companies that use debt in their capital structure are said to be using financial leverage. Using leverage can increase shareholder returns, but leverage also increases the risk that shareholders...

Study smarter with the SolutionInn App