1. 2. The Student Loan Application Office (SLAO) of Country A's Government has decided to build...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
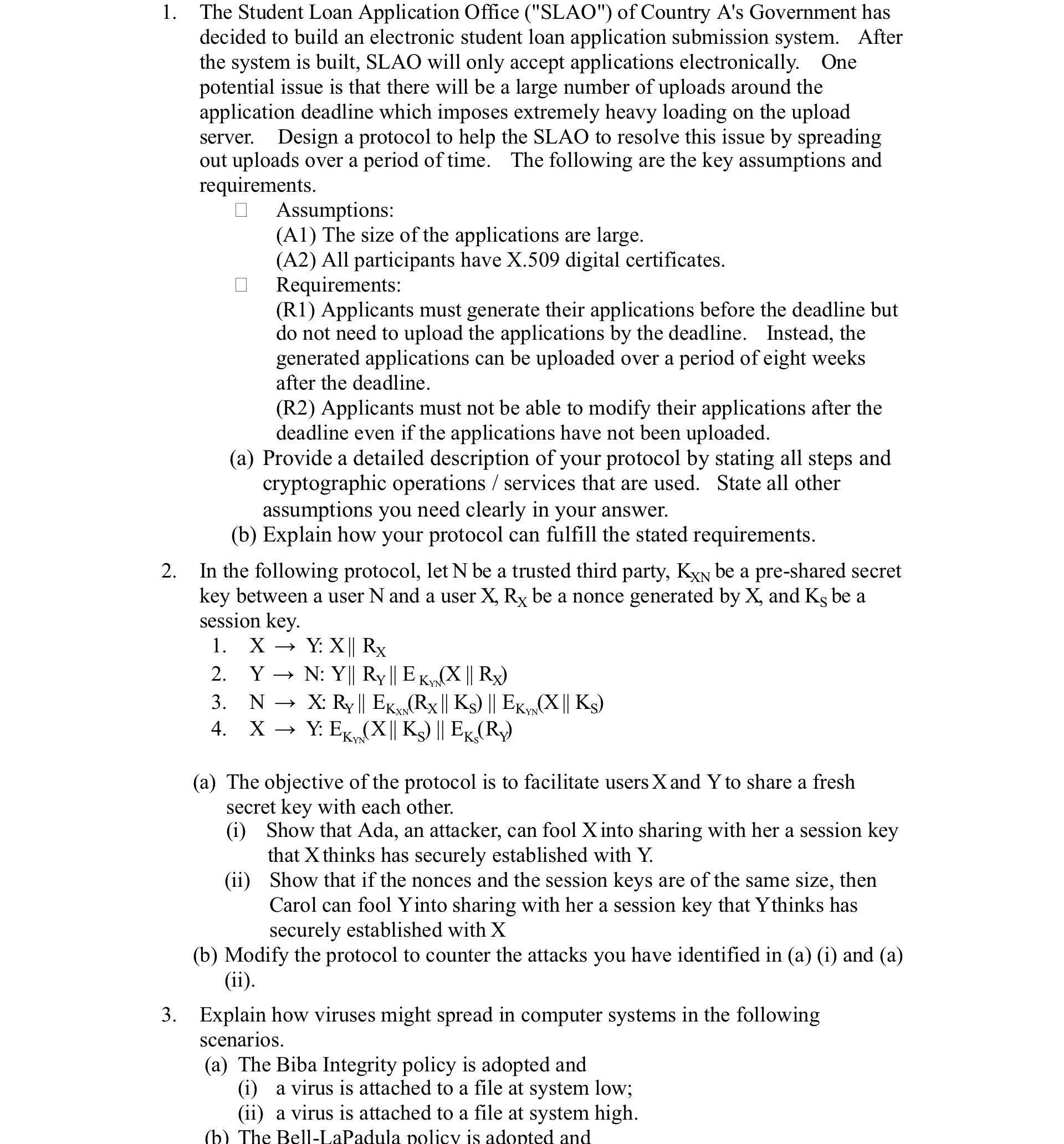
1. 2. The Student Loan Application Office ("SLAO") of Country A's Government has decided to build an electronic student loan application submission system. After the system is built, SLAO will only accept applications electronically. One potential issue is that there will be a large number of uploads around the application deadline which imposes extremely heavy loading on the upload server. Design a protocol to help the SLAO to resolve this issue by spreading out uploads over a period of time. The following are the key assumptions and requirements. Assumptions: (A1) The size of the applications are large. (A2) All participants have X.509 digital certificates. Requirements: (R1) Applicants must generate their applications before the deadline but do not need to upload the applications by the deadline. Instead, the generated applications can be uploaded over a period of eight weeks after the deadline. (R2) Applicants must not be able to modify their applications after the deadline even if the applications have not been uploaded. (a) Provide a detailed description of your protocol by stating all steps and cryptographic operations/services that are used. State all other assumptions you need clearly in your answer. (b) Explain how your protocol can fulfill the stated requirements. In the following protocol, let N be a trusted third party, KXN be a pre-shared secret key between a user N and a user X, Rx be a nonce generated by X, and Ks be a session key. 1. XY: X|| Rx 2. Y N: Y|| Ry || EK (X || Rx) 3. 4. XY: EK NX: Ry || EK (Rx || Ks) || EK, (X|| Ks) XN Y: EK (X|| Ks) || EK, (Ry) YN (a) The objective of the protocol is to facilitate users X and Y to share a fresh secret key with each other. (i) Show that Ada, an attacker, can fool X into sharing with her a session key that X thinks has securely established with Y. (ii) Show that if the nonces and the session keys are of the same size, then Carol can fool Yinto sharing with her a session key that Ythinks has securely established with X (b) Modify the protocol to counter the attacks you have identified in (a) (i) and (a) (ii). 3. Explain how viruses might spread in computer systems in the following scenarios. (a) The Biba Integrity policy is adopted and (i) a virus is attached to a file at system low; (ii) a virus is attached to a file at system high. (b) The Bell-LaPadula policy is adopted and 1. 2. The Student Loan Application Office ("SLAO") of Country A's Government has decided to build an electronic student loan application submission system. After the system is built, SLAO will only accept applications electronically. One potential issue is that there will be a large number of uploads around the application deadline which imposes extremely heavy loading on the upload server. Design a protocol to help the SLAO to resolve this issue by spreading out uploads over a period of time. The following are the key assumptions and requirements. Assumptions: (A1) The size of the applications are large. (A2) All participants have X.509 digital certificates. Requirements: (R1) Applicants must generate their applications before the deadline but do not need to upload the applications by the deadline. Instead, the generated applications can be uploaded over a period of eight weeks after the deadline. (R2) Applicants must not be able to modify their applications after the deadline even if the applications have not been uploaded. (a) Provide a detailed description of your protocol by stating all steps and cryptographic operations/services that are used. State all other assumptions you need clearly in your answer. (b) Explain how your protocol can fulfill the stated requirements. In the following protocol, let N be a trusted third party, KXN be a pre-shared secret key between a user N and a user X, Rx be a nonce generated by X, and Ks be a session key. 1. XY: X|| Rx 2. Y N: Y|| Ry || EK (X || Rx) 3. 4. XY: EK NX: Ry || EK (Rx || Ks) || EK, (X|| Ks) XN Y: EK (X|| Ks) || EK, (Ry) YN (a) The objective of the protocol is to facilitate users X and Y to share a fresh secret key with each other. (i) Show that Ada, an attacker, can fool X into sharing with her a session key that X thinks has securely established with Y. (ii) Show that if the nonces and the session keys are of the same size, then Carol can fool Yinto sharing with her a session key that Ythinks has securely established with X (b) Modify the protocol to counter the attacks you have identified in (a) (i) and (a) (ii). 3. Explain how viruses might spread in computer systems in the following scenarios. (a) The Biba Integrity policy is adopted and (i) a virus is attached to a file at system low; (ii) a virus is attached to a file at system high. (b) The Bell-LaPadula policy is adopted and
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below Answer 1 Protocol for Spreading out Student Loan Application Uploads a Detailed Protocol Description Assumptions A1 Large application sizes ... View the full answer

Related Book For 

Posted Date:
Students also viewed these operating system questions
-
When the researcher starts with a guess or prior probability about the cause of an event, he/she is using ______ inference. A. chi B. Bayesian C. sequential D. natural
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Kenny operates a store, where he sells feed and other supplies to farmers. Heather purchases a $20,000 tractor from Kenny and pays Kenny with $18,000 in cash and $2,000 in corn. How much gross income...
-
Selected transactions for Thyme Advertising Company, Inc. are listed here. 1. Issued common stock to investors in exchange for cash received from investors. 2. Paid monthly rent. 3. Received cash...
-
X, Y and Z have been in partnership for several years, sharing profits and losses in the ratio 3 : 2 : 1. Their last balance sheet which was prepared on 31 October 20X9 is as follows: Despite making...
-
It is \(8: 00\). What time will it be in 70 hours?
-
Jill has decided that the BackPack Company must have very good customer service. She has asked you to develop a level aggregate plan using inventories but not back orders. All demand must be met each...
-
Consider a? five-year, default-free bond with annual coupons of 5% and a face value of $1,000 and assume? zero-coupon yields on? default-free securities are as summarized in the following? tab...
-
You are the manager of a U.S. company situated in Los Angeles and manages the import/export division of the company. The company distributes (resells) a variety of consumer products imported to the...
-
When interest earned each period is added to the principal for purposes of computing interest for the next period, this is known as __________________ interest. When interest earned each period is...
-
Direct materials Polaski Company manufactures and sells a single product called a Ket. Operating at capacity, the company can produce and sell 30,000 Rets per year. Costs associated with this level...
-
find the mean and standard deviation of the sample of housefly wing lengths list all the data values that are within 2 standard deviations of the mean. justify how you obtained those data values....
-
The purpose of the independent audit during project closeout is to get an objective and comprehensive assessment of the quality of all project deliverables. True False
-
Given the information below, what is the gross profit? Sales revenue Accounts receivable Ending inventory Cost of goods sold Sales returns $ 345,000 60,000 118,000 239,000 30,000
-
Sheridan Company manufactures outdoor fireplaces. For the first 9 months of 2020, the company reported the following operating results while operating at 80% of plant capacity: Sales (82,300 units)...
-
The Back2Life budgeted to market and sell 5,000 of these work stations at $200,000 per station in 2021. They budgeted $200,000 fixed costs/year and $80.00 variable cost per station. They ended up...
-
What is beacon marketing? What are digital wallets?
-
All transactions involving Notes Payable and related accounts of Pearl Company during 2010 are as follows: Determine the amount of the transactions affecting financing activities and show how they...
-
Annas, Inc., has a $350,000, 4 percent bond issue that was issued a number of years ago at face value. There are now 10 years left on the bond issue, and the market increase rate is 8 percent....
-
Daize Corp. is analyzing a proposal to switch its factory over to a lights-out operation similar to the one discussed in this chapters Decision Point. To do so, it must acquire a fully automated...
-
Explain how property and liability insurance protect.
-
Describe how insurance uses different risk management methods to reduce risk.
-
Explain the difference between actual cash value and replacement value.

Study smarter with the SolutionInn App