(a) An n n matrix K is the encryption matrix for the Hill cipher. Give...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
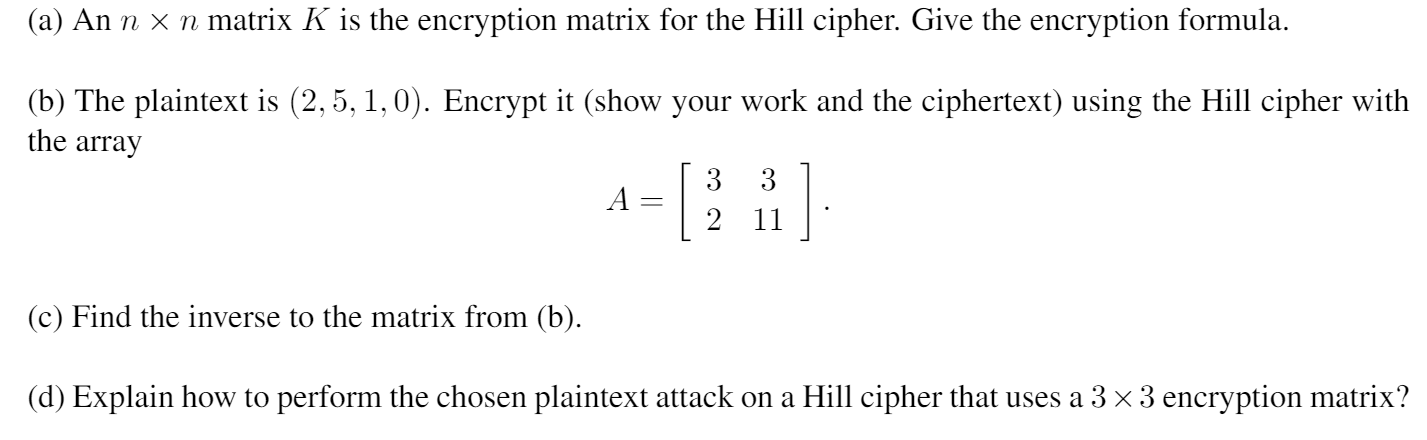
(a) An n × n matrix K is the encryption matrix for the Hill cipher. Give the encryption formula. (b) The plaintext is (2, 5, 1,0). Encrypt it (show your work and the ciphertext) using the Hill cipher with the array (c) Find the inverse to the matrix from (b). A = 3 3 2 11 (d) Explain how to perform the chosen plaintext attack on a Hill cipher that uses a 3 × 3 encryption matrix? (a) An n × n matrix K is the encryption matrix for the Hill cipher. Give the encryption formula. (b) The plaintext is (2, 5, 1,0). Encrypt it (show your work and the ciphertext) using the Hill cipher with the array (c) Find the inverse to the matrix from (b). A = 3 3 2 11 (d) Explain how to perform the chosen plaintext attack on a Hill cipher that uses a 3 × 3 encryption matrix?
Expert Answer:
Answer rating: 100% (QA)
Solution Hill cipher is a polygraphic cipher which is based on Linear Alg... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Encrypt the following words using a Caesar cipher with a distance value of 5. Provide an algorithm written in python to generate the cypher. So Python Much cipher Wow Write a program to open...
-
Please show your work and write out your solutions in detail by giving formulas and a short summary at the end. Please do not just post about financial calc or excel without explaining how you got...
-
The ciphertext OIKYWVHBX was produced by encrypting a plaintext message using the Vigenre cipher with key HOT. What is the plaintext message?
-
Identify and discuss three ways that tourism and hospitality businesses can maintain a long-term relationship with their clients
-
Provide some examples of front-of-the-house and back-of-the-house service operations.
-
How does channel positioning relate to channel design and in turn to differential advantage via channel design?
-
Discuss ways in which securities issued by state and local governments are similar to corporate bonds.
-
The management of the just Like Home restaurant has asked you to analyze some of its processes. One of these processes is making a single-scoop ice cream cone. Cones can be ordered by a server (for...
-
Required information Use the following information for the Exercises below. (Algo) [The following information applies to the questions displayed below.] A manufactured product has the following...
-
Ben Rawiller, a resident taxpayer operates an electrical goods store. During the 2021/22 tax year, Ben had the following transactions: Sales Purchases of Trading Stock Stock-1 July 2020 $ 2,927,800...
-
! Required information [The following information applies to the questions displayed below.] AirPro Corporation reports the following for this period. Actual total overhead Standard overhead applied...
-
What is the function of the international monetary system?
-
Suppose that on January 1, the price of one hundred yen was 80 and PPP held. Over the year, the Japanese inflation rate was 5 percent, and the U.S. inflation rate was 10 percent. If the exchange rate...
-
Following are the proportions of the United States population that is female for five age groups. a. Is this a relative frequency table? Explain why or why not? b. Would it be appropriate to...
-
What connections exist between the current account and the capital account?
-
What were the key accomplishments of the Bretton Woods conference?
-
Ethics and Qualitative Research Review the American Psychological Association's (APA) " Ethical Principles of Psychologists and Code of Conduct. " Describe a hypothetical research situation related...
-
One study found that the elderly who do not have children dissave at about the same rate as the elderly who do have children. What might this finding imply about the reason the elderly do not dissave...
-
In a bus CSMA/CD network with a data rate of 10 Mbps, a collision occurs 20 s after the first bit of the frame leaves the sending station. What should the length of the frame be so that the sender...
-
Which of the following is a random-access protocol? a. CSMA/CD b. Polling c. TDMA
-
What is the function of the twisting in twisted-pair cable?
-
Claudia Vargas is contemplating the purchase of a machine that would be used in her business. The following estimates are available: Required: Determine the payback period for the machine purchase....
-
Cesar Nieto is contemplating the purchase of a machine that would be used in his business. The following estimates are available: Required: Determine the payback period for the machine purchase....
-
Veronica Torres is considering opening a ceramic studio. She has determined that it would require an investment of $14,000 to open the store. She believes that the cash inflows would grow each year...

Study smarter with the SolutionInn App


