Consider that your cache is a direct mapped memory. It can hold up to 256 byte...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
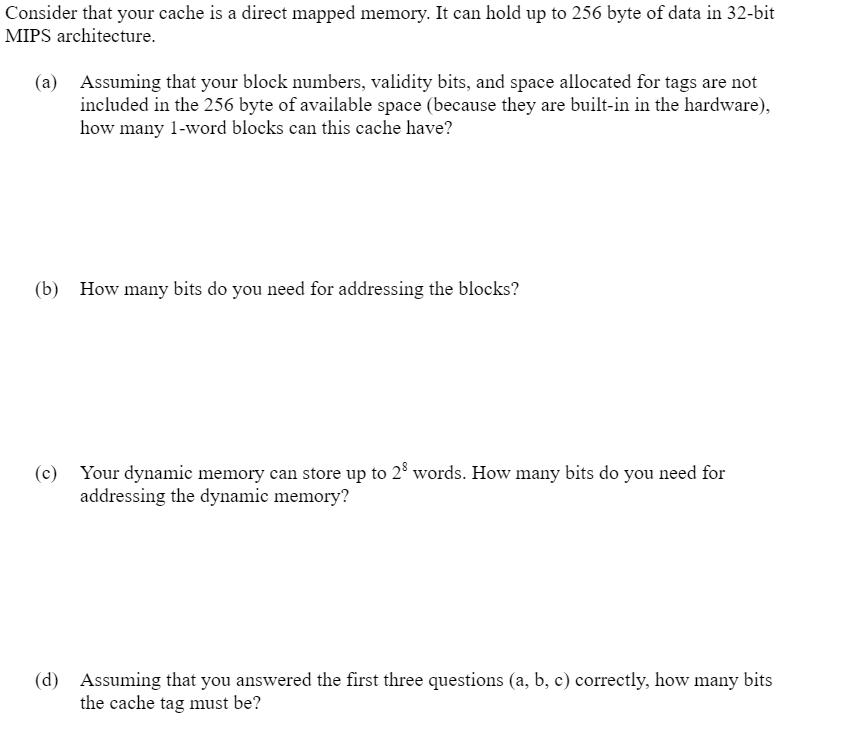
Consider that your cache is a direct mapped memory. It can hold up to 256 byte of data in 32-bit MIPS architecture. (a) Assuming that your block numbers, validity bits, and space allocated for tags are not included in the 256 byte of available space (because they are built-in in the hardware), how many 1-word blocks can this cache have? (b) How many bits do you need for addressing the blocks? (c) Your dynamic memory can store up to 28 words. How many bits do you need for addressing the dynamic memory? (d) Assuming that you answered the first three questions (a, b, c) correctly, how many bits the cache tag must be? Consider that your cache is a direct mapped memory. It can hold up to 256 byte of data in 32-bit MIPS architecture. (a) Assuming that your block numbers, validity bits, and space allocated for tags are not included in the 256 byte of available space (because they are built-in in the hardware), how many 1-word blocks can this cache have? (b) How many bits do you need for addressing the blocks? (c) Your dynamic memory can store up to 28 words. How many bits do you need for addressing the dynamic memory? (d) Assuming that you answered the first three questions (a, b, c) correctly, how many bits the cache tag must be?
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Compare Christ s Golden Rule with Hobbes Golden Rule. Which do you think is more effective in getting people to obey the laws, and why?
-
Portray in words what transforms you would have to make to your execution to some degree (a) to accomplish this and remark on the benefits and detriments of this thought.You are approached to compose...
-
answer the question clearly You are building a flight-control system for which a convincing safety case must be made. Would you assign the tasks of safety requirements engineering, test case...
-
11. Calculate the expected return and standard deviation for the risky portfolio on the CAL (with or without borrowing) and for the investor's complete portfolio on the CAL. 8(,1)% Std dev= 30 25 18...
-
Classify each of the following species as a weak or strong base: (a) LiOH, (b) CN-, (c) H2O, (d) ClO4-, (e) NH2-.
-
To smooth out swings in the business cycle, the government influences the economy through its fiscal and monetary policies. Discuss the monetary and fiscal policies that have been applied in response...
-
Why is the accounting different for nonconvertible bonds with detachable stock purchase warrants and nonconvertible bonds with nondetachable stock purchase warrants?
-
Angelo Bank is planning to replace some old ATM machines and has decided to use the York Machine. Anita Chavez, the controller, has prepared the analysis shown here. She has recommended the purchase...
-
EBIT of the company before interest and taxes - 2 million $,interest on current debts - 0.4 million $, the number of ordinaryshares - 5000, the income tax rate - 20%.The company needs 3million $ to 2...
-
Imax Corporation is a large entertainment technology company, with headquarters in New York and Toronto, and theatres worldwide. Its share price, which was as high as Can.$ 13.89 on the Toronto Stock...
-
3. (c) Nabil Ahmad quite interested in purchase a European call option on Ali Baba industry, with a strike price of RM35 and 2 years 9 months until expiration. Ali Baba's share is currently trading...
-
How do materialized views enhance query performance and support complex analytics in data warehousing environments by precomputing and caching aggregated or derived data from underlying tables, and...
-
How do emerging trends in cloud computing, edge computing, and hybrid infrastructure architectures impact the design and implementation of backup and recovery solutions, reshaping traditional...
-
How do advanced backup and recovery strategies transcend traditional notions of data protection, encompassing holistic approaches to disaster resilience, business continuity planning, and regulatory...
-
How do you ensure compliance with regulatory requirements and industry standards related to data integrity, including the implementation of data governance frameworks and data quality assurance...
-
How do you ensure data integrity in federated and distributed databases, including the implementation of consensus protocols or Byzantine fault-tolerant algorithms to reach agreement on the...
-
A machine costing $214,800 with a four-year life and an estimated $18,000 salvage value is installed in Luther Company's factory on January 1. The factory manager estimates the machine will produce...
-
Q:1 Take any product or service offered in Pakistan and apply all determinents of customer Perceived value ?
-
A highway construction zone has a posted speed limit of 40 miles per hour. Workers working at the site claim that the mean speed of vehicles passing through this construction zone is at least 50...
-
A statistical experiment has 10 equally likely outcomes that are denoted by 1, 2, 3, 4, 5, 6, 7, 8, 9, and 10. Let event A = {3, 4, 6, 9} and event B = {1, 2, 5}. a. Are events A and B mutually...
-
The recommended acidity levels for sweet white wines (e.g., certain Rieslings, Port, Eiswein, Muscat) is .70% to .85% (www.grapestompers.com/articles/measure_acidity.htm). A vintner (winemaker) takes...
-
List the three parts which normally comprise a code of professional conduct, and state the purpose of each.
-
Explain the need for a code of professional ethics for public accountants. In which ways should the public accoun tants' code of ethics be similar to and different from that of other professional...
-
What are the four facets of independence discussed in the chapter? Explain why each is a necessary component of a public accountant's independence.

Study smarter with the SolutionInn App