John keeps a list on his cell phone of all the passwords he uses to access...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
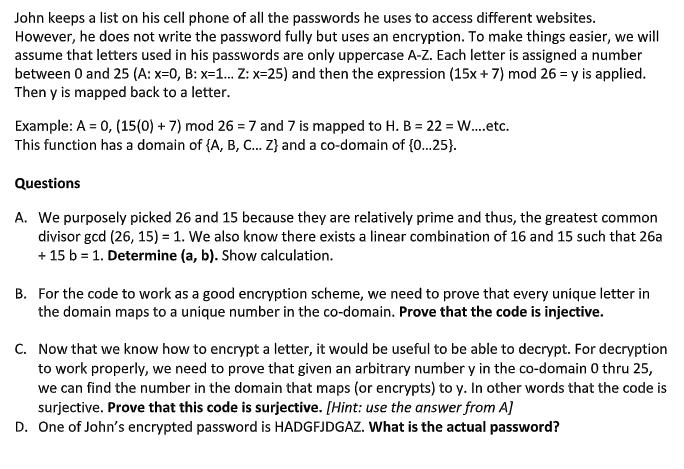
John keeps a list on his cell phone of all the passwords he uses to access different websites. However, he does not write the password fully but uses an encryption. To make things easier, we will assume that letters used in his passwords are only uppercase A-Z. Each letter is assigned a number between 0 and 25 (A: x=0, B: x=1... Z: x=25) and then the expression (15x+7) mod 26 = y is applied. Then y is mapped back to a letter. Example: A = 0, (15(0) + 7) mod 267 and 7 is mapped to H. B = 22 = W....etc. This function has a domain of {A, B, C... Z} and a co-domain of {0...25}. Questions A. We purposely picked 26 and 15 because they are relatively prime and thus, the greatest common divisor gcd (26, 15) = 1. We also know there exists a linear combination of 16 and 15 such that 26a + 15 b = 1. Determine (a, b). Show calculation. B. For the code to work as a good encryption scheme, we need to prove that every unique letter in the domain maps to a unique number in the co-domain. Prove that the code is injective. C. Now that we know how to encrypt a letter, it would be useful to be able to decrypt. For decryption to work properly, we need to prove that given an arbitrary number y in the co-domain 0 thru 25, we can find the number in the domain that maps (or encrypts) to y. In other words that the code is surjective. Prove that this code is surjective. [Hint: use the answer from A] D. One of John's encrypted password is HADGFJDGAZ. What is the actual password? John keeps a list on his cell phone of all the passwords he uses to access different websites. However, he does not write the password fully but uses an encryption. To make things easier, we will assume that letters used in his passwords are only uppercase A-Z. Each letter is assigned a number between 0 and 25 (A: x=0, B: x=1... Z: x=25) and then the expression (15x+7) mod 26 = y is applied. Then y is mapped back to a letter. Example: A = 0, (15(0) + 7) mod 267 and 7 is mapped to H. B = 22 = W....etc. This function has a domain of {A, B, C... Z} and a co-domain of {0...25}. Questions A. We purposely picked 26 and 15 because they are relatively prime and thus, the greatest common divisor gcd (26, 15) = 1. We also know there exists a linear combination of 16 and 15 such that 26a + 15 b = 1. Determine (a, b). Show calculation. B. For the code to work as a good encryption scheme, we need to prove that every unique letter in the domain maps to a unique number in the co-domain. Prove that the code is injective. C. Now that we know how to encrypt a letter, it would be useful to be able to decrypt. For decryption to work properly, we need to prove that given an arbitrary number y in the co-domain 0 thru 25, we can find the number in the domain that maps (or encrypts) to y. In other words that the code is surjective. Prove that this code is surjective. [Hint: use the answer from A] D. One of John's encrypted password is HADGFJDGAZ. What is the actual password?
Expert Answer:

Related Book For 

Quantitative Analysis for Management
ISBN: 978-0132149112
11th Edition
Authors: Barry render, Ralph m. stair, Michael e. Hanna
Posted Date:
Students also viewed these programming questions
-
(b) Does it make sense to interpret the y-intercept? Explain. Choose the correct answer below. A. Yeslong dashit makes sense to interpret the y-intercept because an x-value of 0 is within the realm...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
List three specific parts of the Case Guide, Objectives and Strategy Section (See below) that you had the most difficulty understanding. Describe your current understanding of these parts. Provide...
-
Suppose that there is parity between the Australian dollar and the United States dollar. Let x be a positive number and assume that the United States dollar increases by 100x % in Australian dollars....
-
In n independent experimental trials, the relative frequency of event A is How large should n be to ensure that the confidence interval estimate has confidence coefficient 0.9? Pn (A).
-
Evaluate the integral. x - 2x - 4 .3 x - 2x dx
-
Ms. Adams has received a job offer from a large investment bank as an assistant to the vice president. Her base salary will be \($35,000.\) She will receive her first annual salary payment one year...
-
You are evaluating the results of a nonstatistical sample of 85 accounts receivable confirmations for the Bohrer Company. Information on the sample and population are included below. An overstatement...
-
. The following table shows the demand for fans manufactured by Leonard's Fan Company. The holding cost for that item is $2 per month and each setup costs $80. Lead time is 0 months. Calculate the...
-
(a) A loop of wire in the shape of a rectangle of width w and length L and a long, straight wire carrying a current I lie on a tabletop as shown in Figure P31.9. (a) Determine the magnetic flux...
-
Cash flows related to three mutually exclusive capital equipment projects are given in table below. Alternative Initial Cost Uniform annual Salvage Value $750 A $1000 $125 B $800 $120 $500 C $600...
-
What are the evolutionary advantages and molecular adaptations associated with extremophiles thriving in environments with extreme conditions, such as high temperatures, acidity, or salinity ?
-
a) How much must you pay for that option (which is based on 100 shares)? b) (8) Assume IBM stock today is at $79.15 per share, and a "January 70 put" is priced at $2.60. If IBM is $80 when the put...
-
Assume an elderly person owns a $350,000 home that is free and clear of mortgage debt. A lender has agreed to a $350,000 reverse mortgage with monthly payments. The loan term is 15 years.The annual...
-
Define the term Balanced Scorecard. Explain how the Balanced Scorecard is important to the Control function.
-
How do advances in molecular genetics, particularly CRISPR-Cas9 gene editing technology, revolutionize our ability to manipulate and engineer genomes for various applications, including biomedicine,...
-
If lim f (x)= 2-2 +2 3 and lim g(x) = 8, evaluate: lim f(x)9(x)+2 x-2 2f(x)+1-9(2)
-
H Corporation has a bond outstanding. It has a coupon rate of 8 percent and a $1000 par value. The bond has 6 years left to maturity but could be called after three years for $1000 plus a call...
-
Ray Bond, from Problem 1-15, is trying to find a new supplier that will reduce his variable cost of production to $15 per unit. If he was able to succeed in reducing this cost, what would the...
-
A company has decided to order 360 units whenever the on-hand inventory falls to 90 units. There appears to be no seasonal fluctuation to the demand, but it does fluctuate daily and is approximately...
-
What are the major differences between PERT and CPM?
-
An anonymous e-mail is sent to an internal auditor that there is fraud in the inventory/ warehousing cycle. Suggest some appropriate audit steps.
-
Go to the Internet and listen to the song by Johnny Cash called "One Piece at a Time." Outline some lessons from the song.
-
During a brainstorming session, a suggestion is made that the most likelihood of fraud in a particular division is in the area of acquisition and payment cycle. Outline five audit steps to help find...

Study smarter with the SolutionInn App