Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
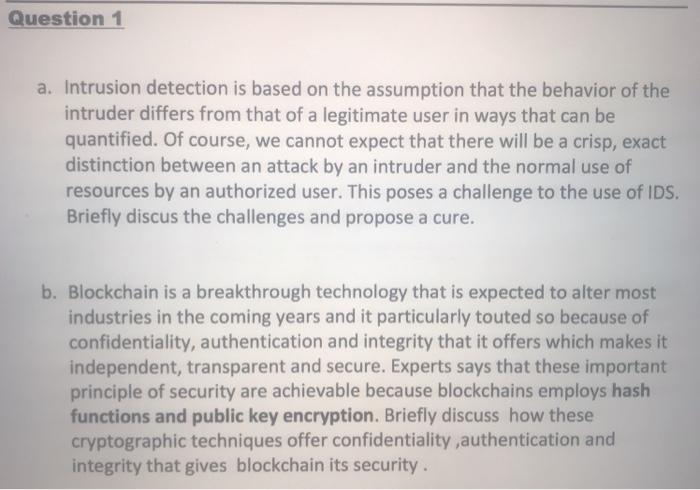
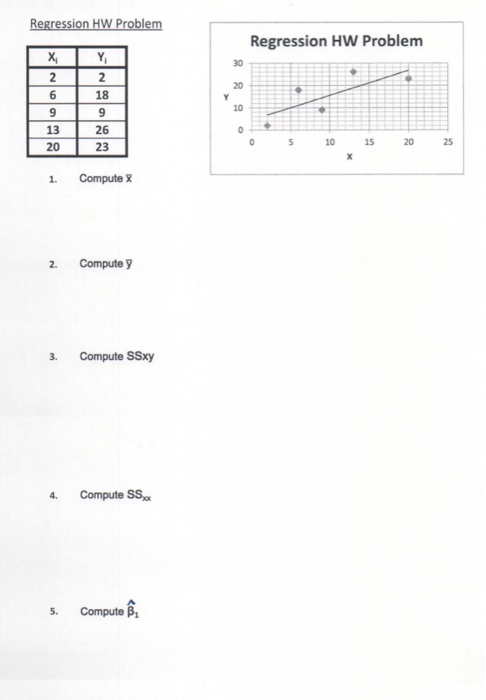
Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25 Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25 Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25
Expert Answer:

Related Book For 

Auditing and Assurance Services A Systematic Approach
ISBN: 978-0077732509
10th edition
Authors: William Messier Jr, Steven Glover, Douglas Prawitt
Posted Date:
Students also viewed these programming questions
-
ine Tollowing information pertains to Hagen Metal works ending inventory for the current year. Unit Market Item C Quantity 290 Unit Cost Value $10 $6 D 280 12 9 K 76 8 M 71 5 12 8 Required a....
-
1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there...
-
1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there...
-
In the previous problem, assume the equity increases by 1,500 solaris due to retained earnings. If the exchange rate at the end of the year is 1.24 solaris per dollar, what does the balance sheet...
-
Let W V with dim V = n. Suppose w1........wn, is an orthogonal basis for W and wm+1,... wn is an orthogonal basis for W. (a) Prove that the combination w1,...,wn forms an orthogonal basis of V. (b)...
-
Question 12 6 Points What is the differential height of water between the two pipe sections in the figure? Air flows through the pipe at a rate of 200 l/s. The pipe consists of two sections of...
-
Improved computer security measures create their own set of problems: user antagonism, sluggish response time, and hampered performance. Many professionals believe that the most effective way to...
-
At December 31, 2008, the available-for-sale equity portfolio for Steffi Graf, Inc. is as follows. On January 20, 2009, Steffi Graf, Inc. sold security A for $15,100. The sale proceeds are net of...
-
Question 6 Case Study Analysis (6 marks) SuffiEffi (which stands for Sufficient and Efficient) is a manufacturing company that sells its products to one major customer (a large distributor) who later...
-
How do Journal this and Trial Balance it and T balance Module 02 Accounting Cycle Part I Taylors Creative Design PART 1 You are an employee at a full-service bookkeeping and auditing firm called...
-
Write a java program to print below pattern?
-
Vaughn, Inc. has 6300 shares of 6%, $100 par value, noncumulative preferred stock and 12600 shares of $1 par value common stock outstanding at December 31, 2020. There were no dividends declared in...
-
A mixture sample containing 80% NaHCO 3 and 20% NaCl was marketed for certain food preparations. As an analytical chemist, you took a 2.00 g of the mixture and heated it until the decomposition...
-
Management of Mittel Company wants to reduce the elapsed time from when a customer places an order to when it is shipped. It provided the following data for a recent quarter: Inspection time Wait...
-
There are several projects that have used education as an ID credit. Find a specific example and summarize it. Do you think this will be applicable to all projects, or is it only specific to certain...
-
a) What is the expected annual profit of the project for each year? b) What is the project's expected Net Present Value (NPV)? c) Is the project's expected Internal Rate of Return (IRR) greater,...
-
What will be the final value of DI after executing the following piece of code? Execute the instructions dependently one after another. CLD MOU CX,OFOH MOU AX.02874H MOU DI,01000H MOU ES, DI SUB...
-
The "Accounts Receivable-Confirmation Statistics" working paper shown on the next page was prepared by an audit assistant for the 2015 audit of Lewis County Water Company, Inc., a continuing audit...
-
Phung, CPA, has been engaged to audit the financial statements of Vernon Distributors, Inc., a continuing audit client, for the year ended September 30. After obtaining an understanding of Vernon's...
-
Distinguish among the three categories of expenses. Provide an example of each type of expense.
-
Denise Oxley and Charles Tatum agreed to liquidate their partnership on May 31 of the current year. On that date, after financial statements were prepared and closing entries were posted, the general...
-
Why should a partnership agreement be in writing?
-
What happens to an existing partnership if a partner dies?

Study smarter with the SolutionInn App