You are assigned as a Cyber Investigator to a Computer Crimes Unit within the Department of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
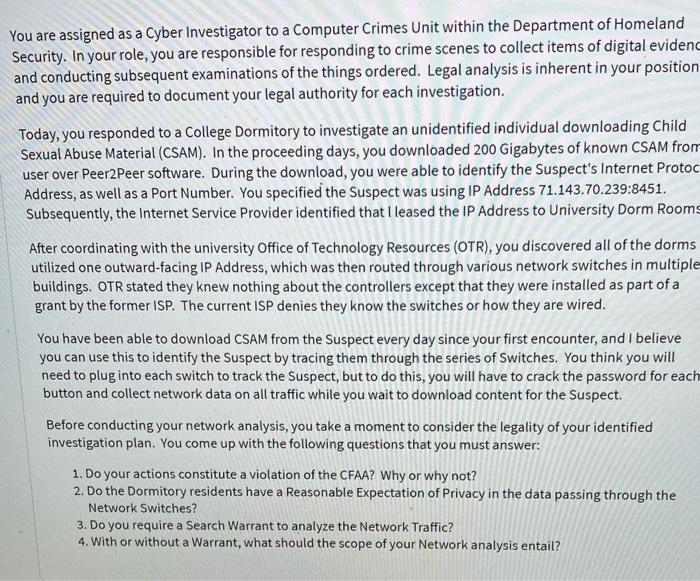
You are assigned as a Cyber Investigator to a Computer Crimes Unit within the Department of Homeland Security. In your role, you are responsible for responding to crime scenes to collect items of digital evidenc and conducting subsequent examinations of the things ordered. Legal analysis is inherent in your position and you are required to document your legal authority for each investigation. Today, you responded to a College Dormitory to investigate an unidentified individual downloading Child Sexual Abuse Material (CSAM). In the proceeding days, you downloaded 200 Gigabytes of known CSAM from user over Peer2Peer software. During the download, you were able to identify the Suspect's Internet Protoc Address, as well as a Port Number. You specified the Suspect was using IP Address 71.143.70.239:8451. Subsequently, the Internet Service Provider identified that I leased the IP Address to University Dorm Rooms After coordinating with the university Office of Technology Resources (OTR), you discovered all of the dorms utilized one outward-facing IP Address, which was then routed through various network switches in multiple buildings. OTR stated they knew nothing about the controllers except that they were installed as part of a grant by the former ISP. The current ISP denies they know the switches or how they are wired. You have been able to download CSAM from the Suspect every day since your first encounter, and I believe you can use this to identify the Suspect by tracing them through the series of Switches. You think you will need to plug into each switch to track the Suspect, but to do this, you will have to crack the password for each button and collect network data on all traffic while you wait to download content for the Suspect. Before conducting your network analysis, you take a moment to consider the legality of your identified investigation plan. You come up with the following questions that you must answer: 1. Do your actions constitute a violation of the CFAA? Why or why not? 2. Do the Dormitory residents have a Reasonable Expectation of Privacy in the data passing through the Network Switches? 3. Do you require a Search Warrant to analyze the Network Traffic? 4. With or without a Warrant, what should the scope of your Network analysis entail? You are assigned as a Cyber Investigator to a Computer Crimes Unit within the Department of Homeland Security. In your role, you are responsible for responding to crime scenes to collect items of digital evidenc and conducting subsequent examinations of the things ordered. Legal analysis is inherent in your position and you are required to document your legal authority for each investigation. Today, you responded to a College Dormitory to investigate an unidentified individual downloading Child Sexual Abuse Material (CSAM). In the proceeding days, you downloaded 200 Gigabytes of known CSAM from user over Peer2Peer software. During the download, you were able to identify the Suspect's Internet Protoc Address, as well as a Port Number. You specified the Suspect was using IP Address 71.143.70.239:8451. Subsequently, the Internet Service Provider identified that I leased the IP Address to University Dorm Rooms After coordinating with the university Office of Technology Resources (OTR), you discovered all of the dorms utilized one outward-facing IP Address, which was then routed through various network switches in multiple buildings. OTR stated they knew nothing about the controllers except that they were installed as part of a grant by the former ISP. The current ISP denies they know the switches or how they are wired. You have been able to download CSAM from the Suspect every day since your first encounter, and I believe you can use this to identify the Suspect by tracing them through the series of Switches. You think you will need to plug into each switch to track the Suspect, but to do this, you will have to crack the password for each button and collect network data on all traffic while you wait to download content for the Suspect. Before conducting your network analysis, you take a moment to consider the legality of your identified investigation plan. You come up with the following questions that you must answer: 1. Do your actions constitute a violation of the CFAA? Why or why not? 2. Do the Dormitory residents have a Reasonable Expectation of Privacy in the data passing through the Network Switches? 3. Do you require a Search Warrant to analyze the Network Traffic? 4. With or without a Warrant, what should the scope of your Network analysis entail?
Expert Answer:
Answer rating: 100% (QA)
1 Whether your actions constitute a violation of the Computer Fraud and Abuse Act CFAA depends on the specifics of the situation and how you access an... View the full answer

Related Book For 

Cost Management A Strategic Emphasis
ISBN: 978-0078025532
6th edition
Authors: Edward Blocher, David Stout, Paul Juras, Gary Cokins
Posted Date:
Students also viewed these business communication questions
-
Find the error with subject-verb agreement. Select the incorrect verb and type it correctly. Three to five minutes are just the right amount of time to steam thin asparagus the asparagus will be...
-
Using the article Comparing Crime Rates between Undocumented Immigrants, Legal Immigrants, and Native-born US citizens in Texas, write a 2-3 page-paper (double-spaced, 1-inch margins, times roman...
-
Answer the questions in your journal. Which contemporary issue interested you the most, and why? (M424) Define Explain Personal Experience What do you think is another contemporary issue the army...
-
Find a couple of bad project management examples from around the world. What were the reasons for the failure? (500 words max) Find a couple of good project management examples from around the world....
-
Refer to the information in RE13-3. Assume that on December 31, 2013, the investment in Todd Corporation bonds has a market value of $22,300, and the investment in Cornett Company stock has a market...
-
What are the three indicators that an organization suffers from poor deployment of Six Sigma principles?
-
The following details for the year ended 31 March 19X8 are available. Draw up the trading account of K Taylor for that year. Stocks: 31 March 19X8 18,504 Returns inwards 1,372 Returns outwards 2,896...
-
Kauli Company produces cellular phones. It has just completed an order for 10,000 phones placed by Stay connect, Ltd. Kauli recently shifted to an activity based costing system, and its controller is...
-
21 You 22m 023/05/21 2023/06/2 3/05 You are a brand new loan officer at Lakshmi Vilas Bank. Your boss gives you two File #1 - Ram Charan Singh needs to purchase a car to get to his new jobstomer...
-
Blossom Corporation manufactures a single product. Monthly production costs incurred in the manufacturing process are shown below for the production of 3,000 units. The utilities and maintenance...
-
A 0.7 MeV photon scatters from an electron initially at rest. If the photon scatters at an angle of 35, calculate (a) the energy and wavelength of the scattered photon, (b) the kinetic energy of the...
-
Give an expression for f(x) using only Real-valued coefficients, having degree 4, passing through the point (-4, -135), with roots x = -1, x = -7, and x = -2+i. Your final answer should not contain...
-
The following table summarizes the activities of a project: A: B: C: D: E: F: G: H: I: J: K: L: M: N: 0: P: R: S: T: Activity Clear site Bring utilities to site Excavate Pour foundation Outside...
-
The proposal to delay got implemented on 15 March 2023 via "REGULATION (EU) 2023/607 OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL of 15 March 2023 amending Regulations (EU) 2017/745 and (EU)...
-
In the last team meeting, a decision to go international was agreed upon. As the Team Lead for marketing of Abena rice, you are expected to communicate (through a memo) any four (4) product-related...
-
What would our supply chain would look like (draw a diagram)? Identify and describe who some of our suppliers will be; list 2 at least sources.
-
Economic feasibility is an important guideline in designing cost accounting systems. Do you agree? Explain.
-
Consider the following information for Fair Wind Yachts, Inc., a manufacturer of sailboat rigging, blocks, and cordage. Advertising Expenses. $ 150,000 Depreciation Expense--Admin. Office 75,000...
-
To maintain profit growth, several manufacturing companies have responded to the recession by cutting jobs. Harley-Davidson reduced its workforce by 1,400 in 2010 and 1,600 more in 2011. As sales...
-
Holly Company has the following information for December 1 to December 31. All direct materials are 100% complete. Required Calculate equivalent units using the weighted-average and FIFO methods....
-
Explain some ways you might reduce motor vehicle insurance premiums.
-
Identify each type of risk and list the four methods of managing risk.
-
Alcohol use is a factor in more than 60 percent of all traffic accidents. Interview classmates, parents, and others to get their views on what can be done to reduce alcohol-related traffic incidents....

Study smarter with the SolutionInn App