Answered step by step
Verified Expert Solution
Question
1 Approved Answer
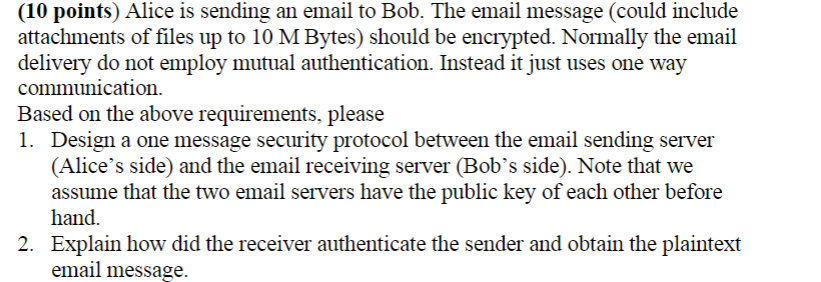
( 1 0 points ) Alice is sending an email to Bob. The email message ( could include attachments of files up to 1 0
points Alice is sending an email to Bob. The email message could include
attachments of files up to Bytes should be encrypted. Normally the email
delivery do not employ mutual authentication. Instead it just uses one way
communication.
Based on the above requirements, please
Design a one message security protocol between the email sending server
Alices side and the email receiving server Bobs side Note that we
assume that the two email servers have the public key of each other before
hand.
Explain how did the receiver authenticate the sender and obtain the plaintext
email message.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started