Answered step by step
Verified Expert Solution
Question
1 Approved Answer
1. 2. The Student Loan Application Office (SLAO) of Country A's Government has decided to build an electronic student loan application submission system. After
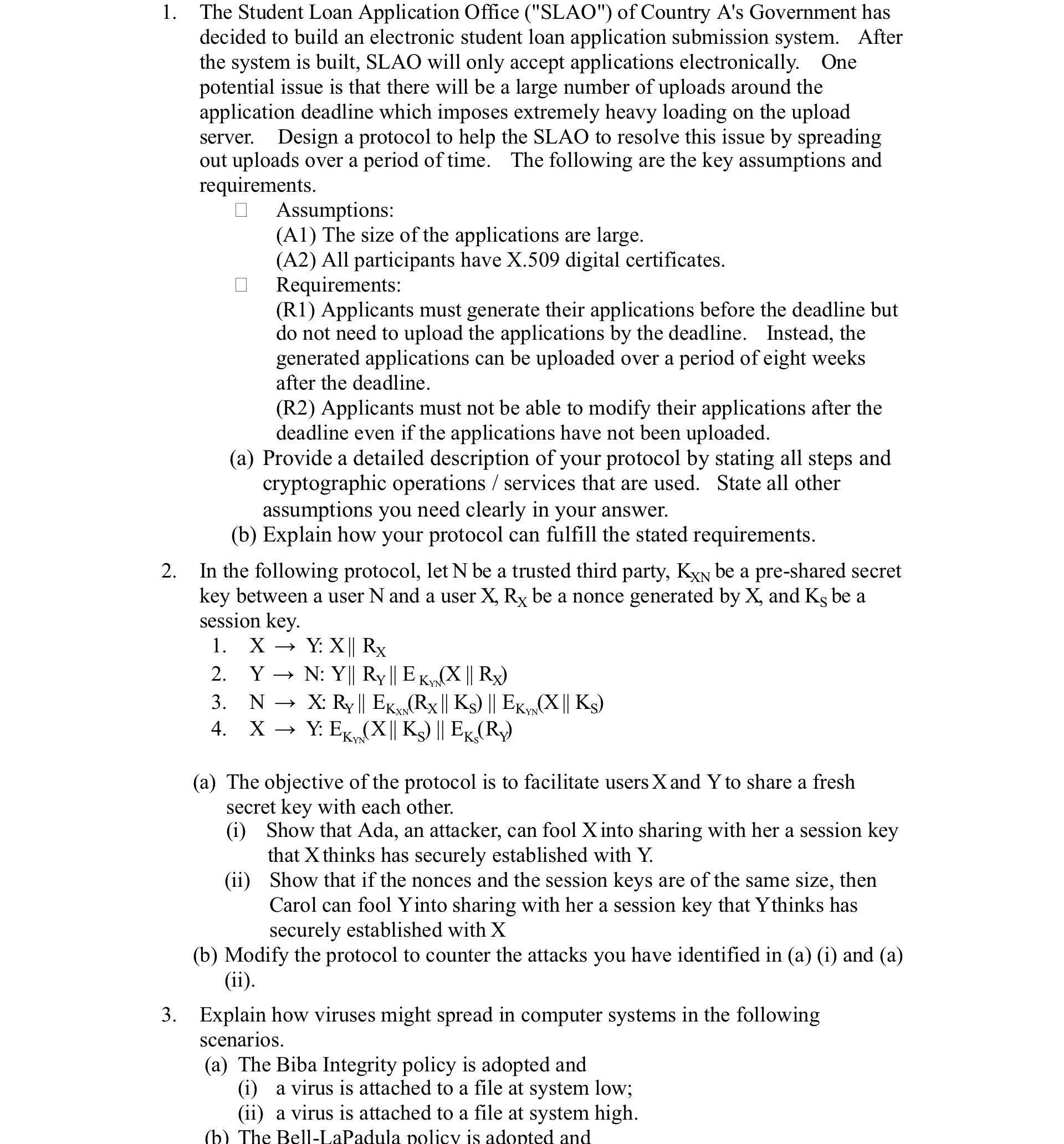
1. 2. The Student Loan Application Office ("SLAO") of Country A's Government has decided to build an electronic student loan application submission system. After the system is built, SLAO will only accept applications electronically. One potential issue is that there will be a large number of uploads around the application deadline which imposes extremely heavy loading on the upload server. Design a protocol to help the SLAO to resolve this issue by spreading out uploads over a period of time. The following are the key assumptions and requirements. Assumptions: (A1) The size of the applications are large. (A2) All participants have X.509 digital certificates. Requirements: (R1) Applicants must generate their applications before the deadline but do not need to upload the applications by the deadline. Instead, the generated applications can be uploaded over a period of eight weeks after the deadline. (R2) Applicants must not be able to modify their applications after the deadline even if the applications have not been uploaded. (a) Provide a detailed description of your protocol by stating all steps and cryptographic operations/services that are used. State all other assumptions you need clearly in your answer. (b) Explain how your protocol can fulfill the stated requirements. In the following protocol, let N be a trusted third party, KXN be a pre-shared secret key between a user N and a user X, Rx be a nonce generated by X, and Ks be a session key. 1. XY: X|| Rx 2. Y N: Y|| Ry || EK (X || Rx) 3. 4. XY: EK NX: Ry || EK (Rx || Ks) || EK, (X|| Ks) XN Y: EK (X|| Ks) || EK, (Ry) YN (a) The objective of the protocol is to facilitate users X and Y to share a fresh secret key with each other. (i) Show that Ada, an attacker, can fool X into sharing with her a session key that X thinks has securely established with Y. (ii) Show that if the nonces and the session keys are of the same size, then Carol can fool Yinto sharing with her a session key that Ythinks has securely established with X (b) Modify the protocol to counter the attacks you have identified in (a) (i) and (a) (ii). 3. Explain how viruses might spread in computer systems in the following scenarios. (a) The Biba Integrity policy is adopted and (i) a virus is attached to a file at system low; (ii) a virus is attached to a file at system high. (b) The Bell-LaPadula policy is adopted and
Step by Step Solution
★★★★★
3.44 Rating (157 Votes )
There are 3 Steps involved in it
Step: 1
The detailed answer for the above question is provided below Answer 1 Protocol for Spreading out Student Loan Application Uploads a Detailed Protocol Description Assumptions A1 Large application sizes ...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started