(1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
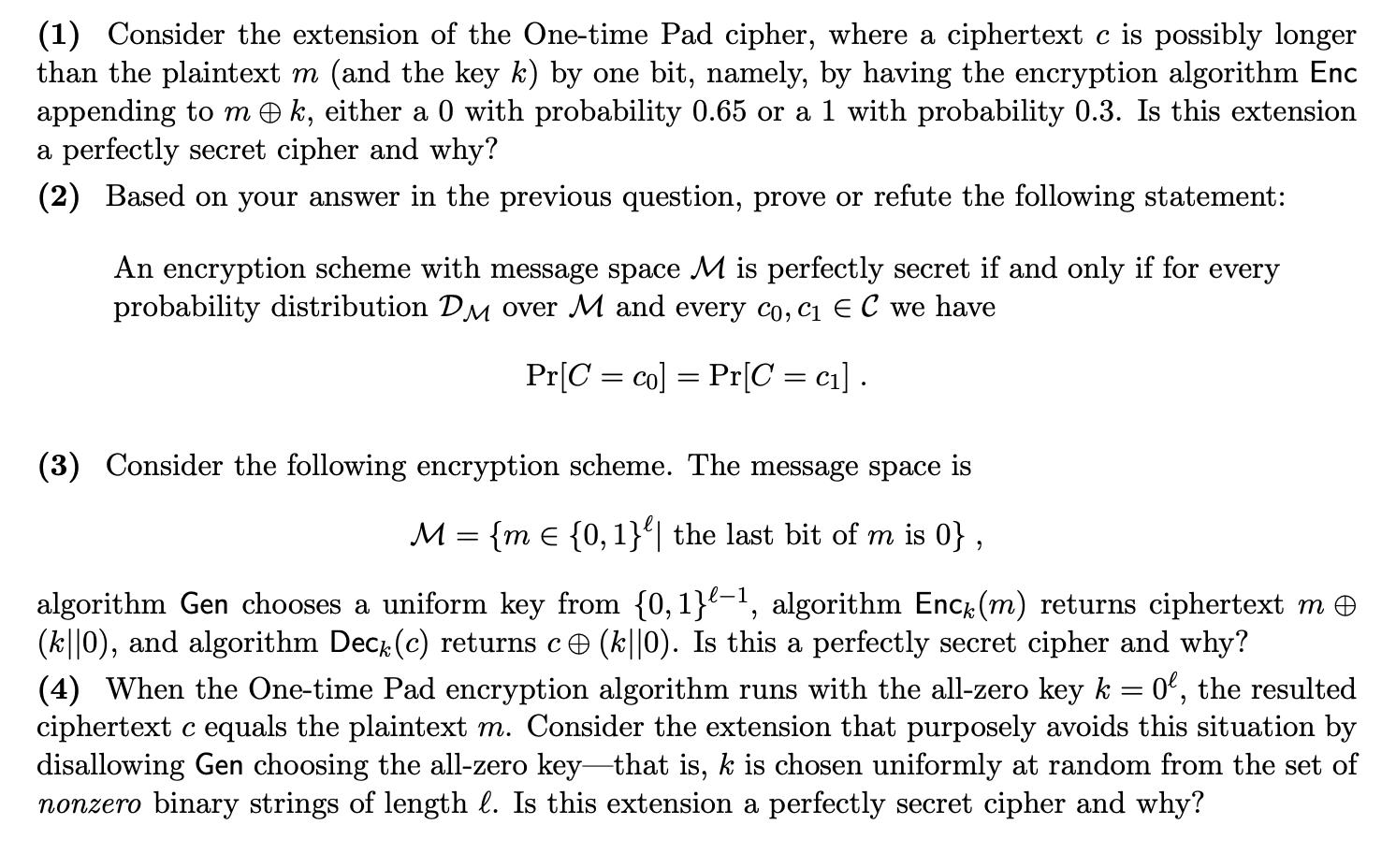
(1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer than the plaintext m (and the key k) by one bit, namely, by having the encryption algorithm Enc appending to mk, either a 0 with probability 0.65 or a 1 with probability 0.3. Is this extension a perfectly secret cipher and why? (2) Based on your answer in the previous question, prove or refute the following statement: An encryption scheme with message space M is perfectly secret if and only if for every probability distribution DM over M and every co, c₁ E C we have Pr[C= co] Pr[C = c₁]. = (3) Consider the following encryption scheme. The message space is M = {m = {0, 1}| the last bit of m is 0}, algorithm Gen chooses a uniform key from {0,1}-¹, algorithm Enck (m) returns ciphertext m © (k||0), and algorithm Decê (c) returns c ℗ (k||0). Is this a perfectly secret cipher and why? (4) When the One-time Pad encryption algorithm runs with the all-zero key k = 0, the resulted ciphertext c equals the plaintext m. Consider the extension that purposely avoids this situation by disallowing Gen choosing the all-zero key-that is, k is chosen uniformly at random from the set of nonzero binary strings of length l. Is this extension a perfectly secret cipher and why? (1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer than the plaintext m (and the key k) by one bit, namely, by having the encryption algorithm Enc appending to mk, either a 0 with probability 0.65 or a 1 with probability 0.3. Is this extension a perfectly secret cipher and why? (2) Based on your answer in the previous question, prove or refute the following statement: An encryption scheme with message space M is perfectly secret if and only if for every probability distribution DM over M and every co, c₁ E C we have Pr[C= co] Pr[C = c₁]. = (3) Consider the following encryption scheme. The message space is M = {m = {0, 1}| the last bit of m is 0}, algorithm Gen chooses a uniform key from {0,1}-¹, algorithm Enck (m) returns ciphertext m © (k||0), and algorithm Decê (c) returns c ℗ (k||0). Is this a perfectly secret cipher and why? (4) When the One-time Pad encryption algorithm runs with the all-zero key k = 0, the resulted ciphertext c equals the plaintext m. Consider the extension that purposely avoids this situation by disallowing Gen choosing the all-zero key-that is, k is chosen uniformly at random from the set of nonzero binary strings of length l. Is this extension a perfectly secret cipher and why?
Expert Answer:
Answer rating: 100% (QA)
Extension of Onetime Pad This extension is not a perfectly secret cipher In a perfectly secret ciphe... View the full answer

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
In 1999, GLSEN identified that little was known about the school experiences of lesbian, gay, bisexual, transgender, and queer (LGBTQ+) youth and that LGBTQ+ youth were nearly absent from national...
-
The article notes that the hospital did not fully understand how its electronic health record system would estimate expected revenue. This was obviously happening at the hospital for some time. How...
-
Consider a repeated version of the game in exercise 24.5. In this version, we do not give all the proposal power to one person but rather imagine that the players are bargaining by making different...
-
Someone offered the investment options to Hendry on January 1, 2023: 1. Hendry has to save up to 5 times the initial deposit of US $ 150,000/year. 2. The savings cannot be taken for 20 years until...
-
According to the News Wire "Reserve Requirements," 1. By how much did excess reserves in China increase (in yuan)? 2. By how much did the lending capacity of Chinese banks increase as a result?
-
Mohammad Omar Aly Hassan and nine others were indicted in a federal district court on charges of conspiring to advance violent jihad (holy war against enemies of Islam) and other offenses related to...
-
Label each of the following characteristics of a corporation as either an (A) advantage or a (D) disadvantage: a. Limited liability b. Taxation c. Regulations d. Transferability of ownership
-
Fouts Systems Co. offers its services to residents in the Chicago area. Selected accounts from the ledger of Fouts Systems Co. for the current fiscal year ended October 31, 2012, are as follows:...
-
Angela Simpson is considering the purchase of a home entertainment center. The product attributes she plans to consider and the weights assigned to each attribute are listed in the table below....
-
Tony and Suzie graduate from college in May 2024 and begin developing their new business. They begin by offering clinics for basic outdoor activities such as mountain biking or kayaking. Upon...
-
How does the concept of servant leadership intersect with transformational leadership principles, and what synergies exist between these approaches in driving organizational excellence and societal...
-
Solve y' = 8-16x-10e -5x+5 given that the solution passes through the point (1,4).
-
Morganton Company makes one product, and has provided the following information to help prepare the master budget for its first four months of operations: The budgeted selling price per unit is $ 7...
-
The following condensed balance sheet is for the partnership of Miller, Tyson, and Watson, who share profits and losses in the ratio of 6 : 2 : 2 , respectively: Cash $ 5 7 , 0 0 0 Liabilities...
-
1. What legal provision 'saved' common law and equity as a source of law in your chosen country at or after it obtained independence or self-governance? 2. Where was common law placed in the...
-
What is the total sales revenue for the first six months of next year on the pro forma income statement assuming Frank's estimate of a 20% increase in sales?
-
What is the sigma level of their FAFSA application program? Does the sigma level per class, for example, senior, change your recommendation on whether to focus on a specific error or a specific...
-
Why do markets typically lead to an efficient outcome for buyers and sellers?
-
In the ring topology in Figure 1.7, what happens if one of the stations is unplugged? Figure 1.7 Repeater Repeater Repeater |Repeater Repeater Repeater
-
Referring to the CRC-8 in Table 5.4, answer the following questions: a. Does it detect a single error? Defend your answer. b. Does it detect a burst error of size 6? Defend your answer. c. What is...
-
Write a statement in Java to create a socket address bound to the local host and the HTTP server process.
-
Oligopolies exist when only a(n) _________ firms control all or most of the production and sale of a product.
-
What is a Nash equilibrium?
-
How does a tit-for-tat strategy work?

Study smarter with the SolutionInn App


