Question
1. Consider the site-to-site VPN scenario shown in Figure 1. Lets deploy the AH protocol on the two VPN routers (see Figure 1) so that
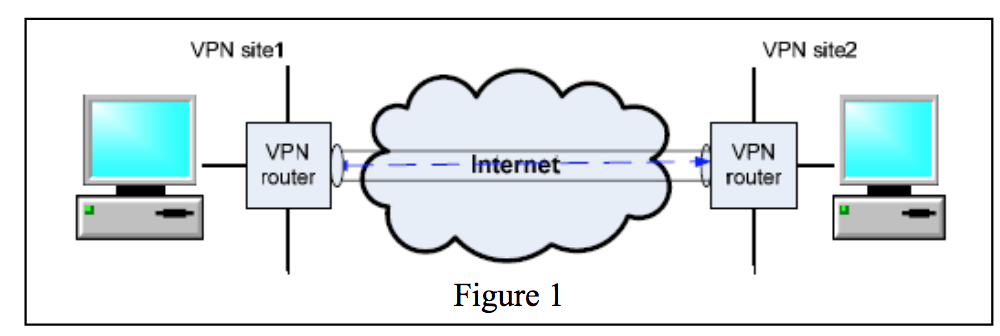
1. Consider the site-to-site VPN scenario shown in Figure 1. Lets deploy the AH protocol on the two VPN routers (see Figure 1) so that no desktop on the two sites need to do any AH operations. Assume Alices desktop is on VPN Site 1 while Bobs desktop is on VPN site 2. Assume the IP address of Alices desktop is 130.2.3.244; the IP address of Bobs desktop is 166.100.66.2.
1.1: When Alice sends message Stock X price $29 to Bob, the message sender program running on Alices desktop needs to firstly compose the packet. Please draw the whole packet. (8 points)
1.2: After a while, the packet will arrive at the VPN router on site 1. After the packet is processed by the VPN router according to the AH protocol, it will be sent out from the VPN router. When the packet leaves the VPN router on site 1, what does the packet look like? Please draw the whole packet. Please note that we assume the VPN router does not enforce the ESP protocol no tunneling. (8 points)
1.3: Lets assume there is a bad guy named Mallory who can intercept this packet in the Internet between these two VPN routers. When this packet is intercepted by Mallory, can Mallory know what the message is? Why? (8 points)
1.4: After a while, the packet will arrive at the VPN router on Site 2. When the packet is processed by the VPN router on Site 2, what will the VPN router do? Please give a step-by-step answer. (8 points)
1.5: To enforce an IP spoofing attack, Mallory will change the header of the packet before it arrives at the VPN router on Site 2. In particular, Mallory will replace the source IP with 130.2.8.3. Can this IP spoofing attack fool the VPN router on Site 2? Why? Note that Mallory will try his best to fake a hash to fool the VPN router. (8 points)
1.6: If the IP spoofing attack mentioned in Question 1.5 is launched by a colleague employee of Alice inside Site 1, Can this IP spoofing attack fool the VPN router on Site 2? Why? (8 points)
2. In this question, we combine ESP with AH. Lets revisit the site-to-site VPN scenario shown in Figure 1. Lets assume Alices desktop is on VPN Site 1 while Bobs is on VPN site 2. Assume the IP address of Alices desktop is 130.2.3.244; the IP address of Bobs desktop is 166.100.66.2. In addition, because neither Alice nor Bob trusts all employees in their companies, they would use the Transport Mode of ESP.
2.1: When Alice sends message Stock X price $29 to Bob, the message sender program running on Alices desktop needs to firstly compose the packet before it is encrypted. This cleartext packet will be the exact same packet in your answer for Question 1.1. Next, the sender program will use ESP (Transport Mode) to encrypt the packet. After this packet is encrypted, what does the packet look like? Please list all the fields contained in the packet; please identify the fields that are encrypted. (8 points) This packet will look like the following
2.2: Next, Alices message sender program will apply the AH protocol so that all IP spoofing attacks and message replacement attacks can be defeated. To compute the hash, which fields of the packet resulted from Question 2.1 will be used as the input? (8 points)
2.3: After the hash is computed by Alices message sender program, the hash will be included in which field of the packet sent out from Alices desktop? (6 points)
2.4: After a while, the packet will arrive at the VPN router on site 2. Will the VPN router decrypt the packet? (6 points)
2.5: After a while, the packet will arrive at Bobs desktop. Is it possible for Bob to decrypt the packet and get the message before the AH header is verified? Why? (8 points)
2.6: After the packet arrives at Bobs desktop, please give a step-by-step answer on how the AH header is verified by the receiver program running on Bobs desktop. (8 points)
2.7: During the whole process from (2.1) to (2.6), where is the IKE protocol used? (8 points)
VPN site1 VPN site2 VPN router Internet VPN router ? _ VPN site1 VPN site2 VPN router Internet VPN router ? _Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started