Question
2. Explain how the public key cryptography works, as shown below. Sender Recipient Original message Buy XYZ @ $100 Buy XYZ @ $100 Recipient's
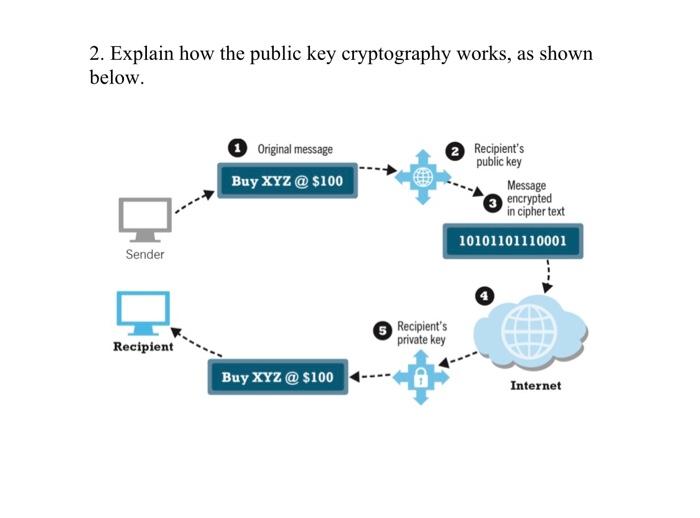
2. Explain how the public key cryptography works, as shown below. Sender Recipient Original message Buy XYZ @ $100 Buy XYZ @ $100 Recipient's private key Recipient's public key Message encrypted in cipher text 10101101110001 Internet
Step by Step Solution
3.40 Rating (163 Votes )
There are 3 Steps involved in it
Step: 1
Public key cryptography also known as asymmetric cryptography is a method of encrypting and decrypti...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get StartedRecommended Textbook for
Cryptography And Network Security
Authors: William Stallings
5th Edition
B00F0ZR6PC, 9780136097044
Students also viewed these Operating System questions
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
View Answer in SolutionInn App



