Question: 3. (16 points) The figure attached below, Figure 8.21 on page 629 in the text, shows the operations that Alice must perform to provide confidentiality,
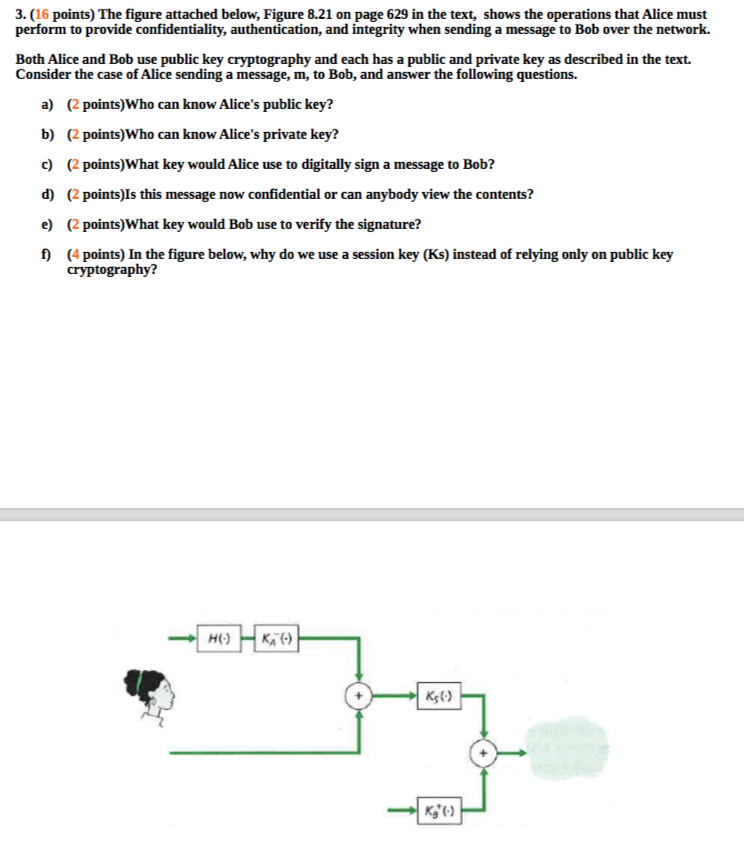
3. (16 points) The figure attached below, Figure 8.21 on page 629 in the text, shows the operations that Alice must perform to provide confidentiality, authentication, and integrity when sending a message to Bob over the network. Both Alice and Bob use public key cryptography and each has a public and private key as described in the text. Consider the case of Alice sending a message, m, to Bob, and answer the following questions. a) (2 points)Who can know Alice's public key? b) (2 points)Who can know Alice's private key? c) 2 points)What key would Alice use to digitally sign a message to Bob? d) (2 points)Is this message now confidential or can anybody view the contents? e (2 points)What key would Bob use to verify the signature? f (4 points) In the figure below, why do we use a session key (Ks) instead of relying only on public key cryptography
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


