3. A system has a 3 ring security model similar to that discussed in class. Ring...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
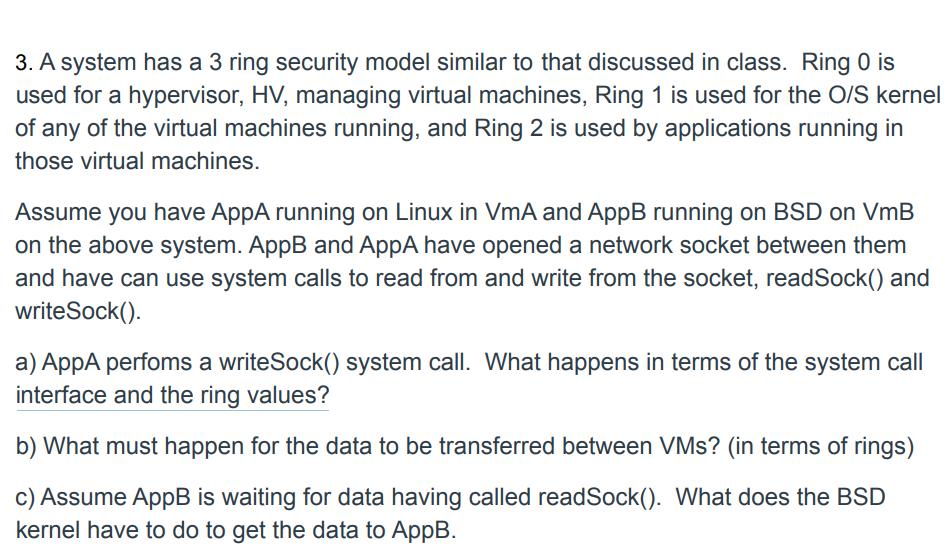
3. A system has a 3 ring security model similar to that discussed in class. Ring 0 is used for a hypervisor, HV, managing virtual machines, Ring 1 is used for the O/S kernel of any of the virtual machines running, and Ring 2 is used by applications running in those virtual machines. Assume you have AppA running on Linux in VmA and AppB running on BSD on VmB on the above system. AppB and AppA have opened a network socket between them and have can use system calls to read from and write from the socket, readSock() and writeSock(). a) AppA perfoms a writeSock() system call. What happens in terms of the system call interface and the ring values? b) What must happen for the data to be transferred between VMs? (in terms of rings) c) Assume AppB is waiting for data having called readSock(). What does the BSD kernel have to do to get the data to AppB. 3. A system has a 3 ring security model similar to that discussed in class. Ring 0 is used for a hypervisor, HV, managing virtual machines, Ring 1 is used for the O/S kernel of any of the virtual machines running, and Ring 2 is used by applications running in those virtual machines. Assume you have AppA running on Linux in VmA and AppB running on BSD on VmB on the above system. AppB and AppA have opened a network socket between them and have can use system calls to read from and write from the socket, readSock() and writeSock(). a) AppA perfoms a writeSock() system call. What happens in terms of the system call interface and the ring values? b) What must happen for the data to be transferred between VMs? (in terms of rings) c) Assume AppB is waiting for data having called readSock(). What does the BSD kernel have to do to get the data to AppB.
Expert Answer:
Answer rating: 100% (QA)
a When AppA performs a writeSock system call it initiates a request to write data to the network socket The system call interface allows the applicati... View the full answer

Related Book For 

Posted Date:
Students also viewed these operating system questions
-
Which is not a reason to use data analytics in business performance? Increase sales. Improve productivity. Eliminate risk and fraud. Improve the customer experience.
-
A system has a 3 ring security model . Ring 0 is used for a hypervisor, HV, managing virtual machines, Ring 1 is used for the O/S kernel of any of the virtual machines running, and Ring 2 is used by...
-
A system has a 3 ring security model. Ring 0 is used for a hypervisor, HV, managing virtual machines, Ring 1 is used for the O/S kernel of any of the virtual machines running, and Ring 2 is used by...
-
Help Mad Mildred's Magic Mall by determining the missing values in the table Labor (workers/day) Output (units/day) Total fixed cost ($/day) Total variable cost ($/day) Total cost ($/day) 50 50 50 75...
-
A zoologist measured tail length in 86 individuals, all in the 1-year age group, of the deermouse Peromyscus. The mean length was 60.43 mm and the standard deviation was 3.06 mm. A 95% confidence...
-
2. What will be the consequences on the competitive situation of the company if the management decides to switch from the existing costing system to: I. a contribution margin approach where overhead...
-
Geary Company had the following transactions: Apr. 15 Issued a \(\$ 6,000,60\)-day, eight percent note payable in payment of an account with Marion Company. May 22 Borrowed \(\$ 50,000\) from...
-
Pharmaceutical Benefits Managers or PBM's are intermediaries between upstream drug manufacturers and downstream insurance companies. They design formularies (list of drugs that insurance will cover)...
-
Identify the risk factors for and the characteristics of potential developmental delays and disabilities and the procedures for appropriate screening and referral. Provide examples of support...
-
Differential Equations 9. Let P (t) denote the population of a colony, where P is measured in units of millions individuals and time t in years. Assume that population is modeled by the logistic...
-
a. What approach should the auditor take in evaluating evidence? b. What restraints should be exercised in the evaluating process?
-
Enumerate the principal types of audit working papers.
-
a. An auditor is expected to have an absolute basis for the expression of an opinion. Do you agree? Why or why not? b. What types of considerations are relevant concerning the basis for the auditor's...
-
Distinguish between (a) schedules and analyses and (b) adjusting and reclassifying entries.
-
a. Enumerate the procedures that may be used in making an analytical review. b. When may analytical review procedures be performed?
-
Prepare the journal entries necessary to record the following transactions. (9 POINTS) 1. In 2017, Payton Corporation began selling a new line of products that carry a two-year warranty against...
-
Suppose that the laptop of Prob. 2.16 is placed in an insulating briefcase with a fully charged battery, but it does not go into sleep mode, and the battery discharges as if the laptop were in use....
-
In A Bend in the River, Nobel Prize winner V. S. Naipaul describes a developing country in which the governments constantly changing tax policies and vague laws regarding property ownership cause...
-
Which of the following demonstrates marginal thinking? a. Deciding to never eat meat b. Deciding to spend one more hour studying economics tonight because you think the improvement on your next test...
-
Which of the following statements is true? a. The opportunity cost of a decision is always expressed in monetary terms. b. The opportunity cost of a decision is the value of the best forgone...

Study smarter with the SolutionInn App