Question: 4. Authentication (12 marks) (a) (6 marks) Consider the following protocol between A and B, with K being a shared symmetric key. What attack is
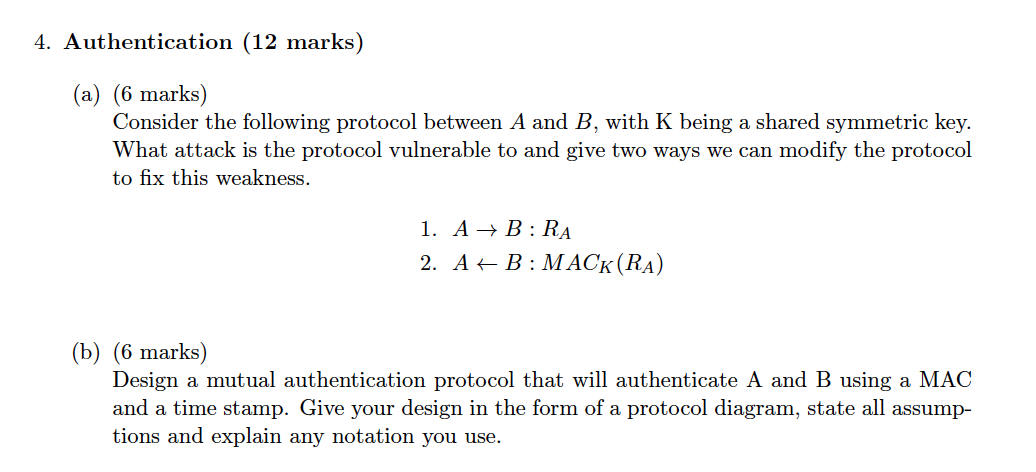
4. Authentication (12 marks) (a) (6 marks) Consider the following protocol between A and B, with K being a shared symmetric key. What attack is the protocol vulnerable to and give two ways we can modify the protocol to fix this weakness. 1. A + B:RA 2. A + B : MACK (RA) (b) (6 marks) Design a mutual authentication protocol that will authenticate A and B using a MAC and a time stamp. Give your design in the form of a protocol diagram, state all assump- tions and explain any notation you use. 4. Authentication (12 marks) (a) (6 marks) Consider the following protocol between A and B, with K being a shared symmetric key. What attack is the protocol vulnerable to and give two ways we can modify the protocol to fix this weakness. 1. A + B:RA 2. A + B : MACK (RA) (b) (6 marks) Design a mutual authentication protocol that will authenticate A and B using a MAC and a time stamp. Give your design in the form of a protocol diagram, state all assump- tions and explain any notation you use
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


