Answered step by step
Verified Expert Solution
Question
1 Approved Answer
5. The following questions are about PUF-based applications: (a) What applications do you know about PUFs? (b) Can you describe in your own words
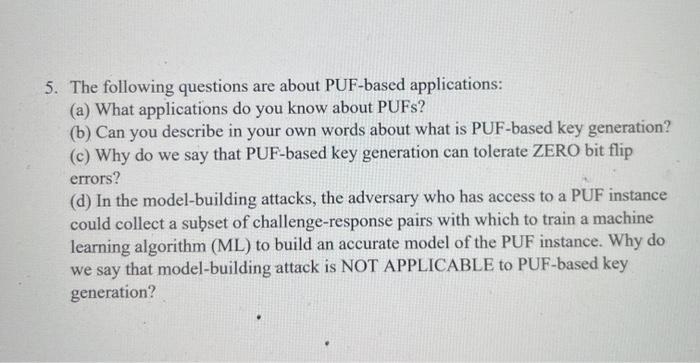
5. The following questions are about PUF-based applications: (a) What applications do you know about PUFs? (b) Can you describe in your own words about what is PUF-based key generation? (c) Why do we say that PUF-based key generation can tolerate ZERO bit flip errors? (d) In the model-building attacks, the adversary who has access to a PUF instance could collect a subset of challenge-response pairs with which to train a machine learning algorithm (ML) to build an accurate model of the PUF instance. Why do we say that model-building attack is NOT APPLICABLE to PUF-based key generation?
Step by Step Solution
★★★★★
3.41 Rating (154 Votes )
There are 3 Steps involved in it
Step: 1
Answer aPhysical unclonable functions PUFs as hardware security primitives exploit manufacturing randomness to extract hardware instancespecific secrets Physically Unclonable Function PUF is a concept ...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started