Answered step by step
Verified Expert Solution
Question
1 Approved Answer
9.6 Computer Fraud and Abuse Techniques. Match the computer fraud and abuse technique in the left column with the scenario in the right column.
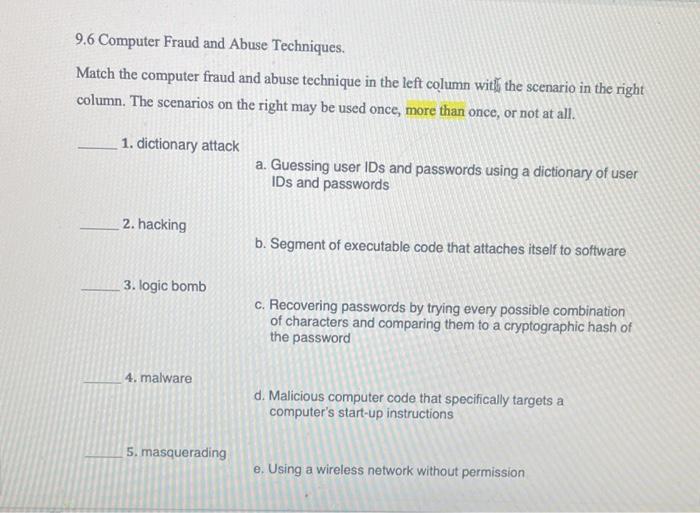
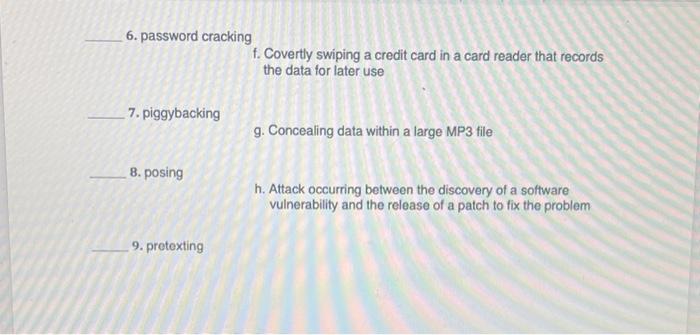
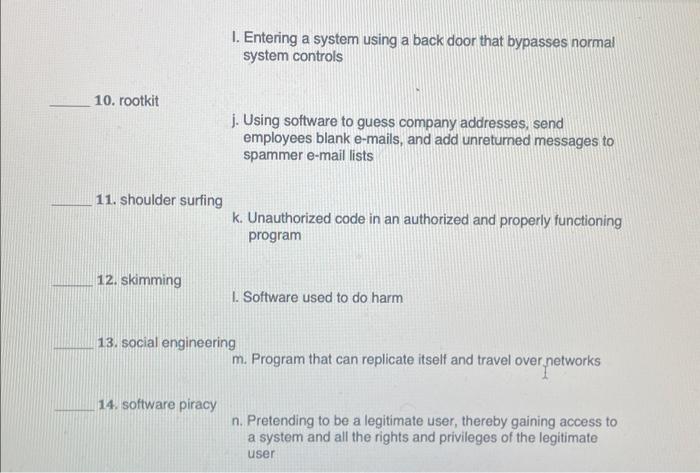
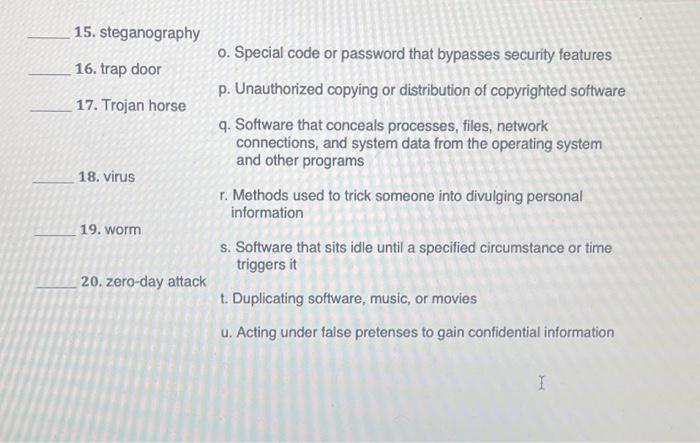
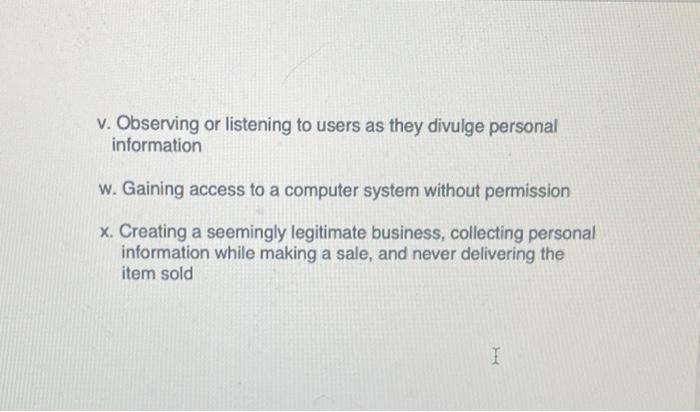
9.6 Computer Fraud and Abuse Techniques. Match the computer fraud and abuse technique in the left column with the scenario in the right column. The scenarios on the right may be used once, more than once, or not at all. 1. dictionary attack 2. hacking 3. logic bomb a. Guessing user IDs and passwords using a dictionary of user IDs and passwords b. Segment of executable code that attaches itself to software c. Recovering passwords by trying every possible combination of characters and comparing them to a cryptographic hash of the password 4. malware d. Malicious computer code that specifically targets a computer's start-up instructions 5. masquerading e. Using a wireless network without permission
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started