Answered step by step
Verified Expert Solution
Question
1 Approved Answer
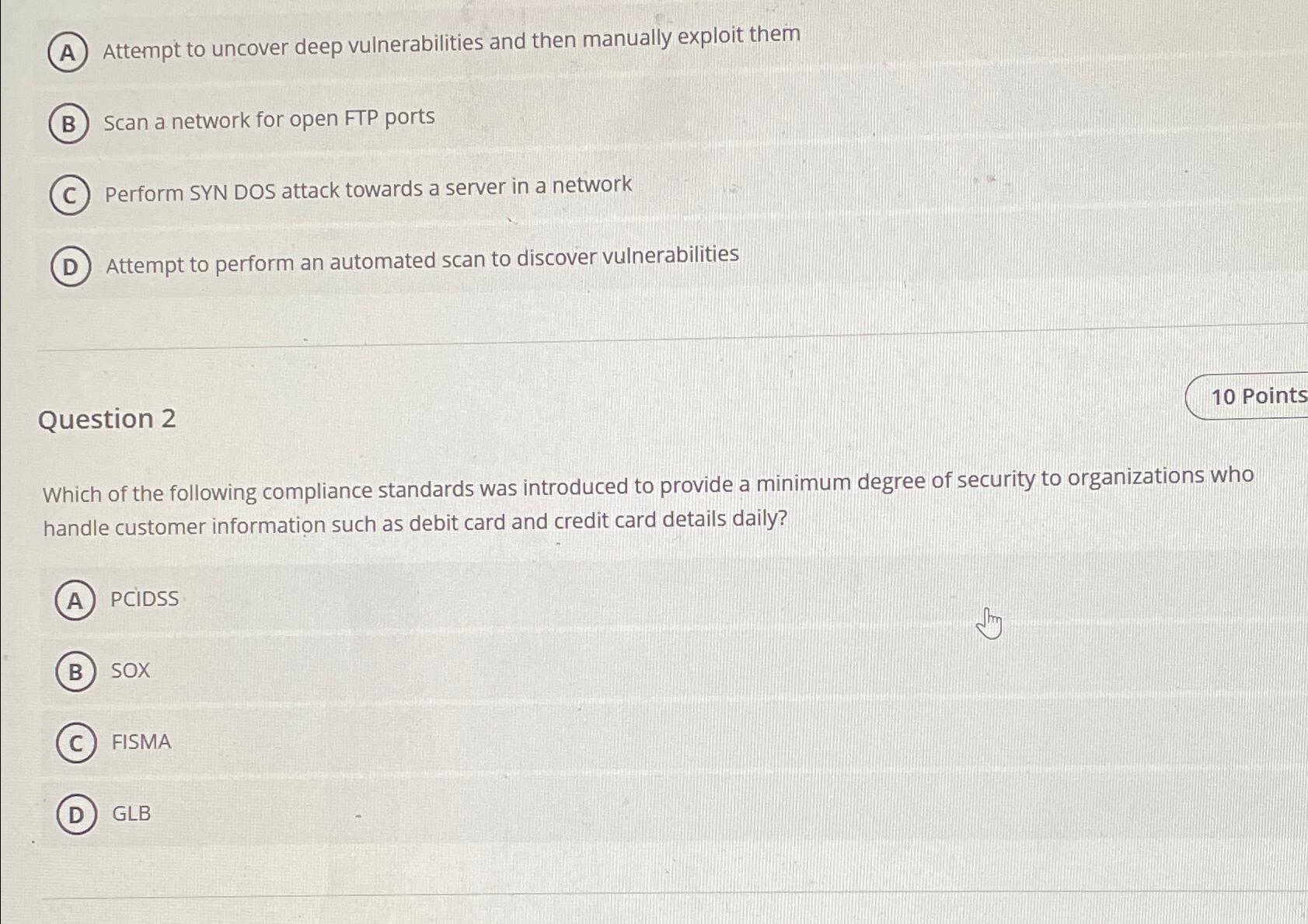
A Attempt to uncover deep vulnerabilities and then manually exploit them Scan a network for open FTP ports Perform SYN DOS attack towards a server
A Attempt to uncover deep vulnerabilities and then manually exploit them
Scan a network for open FTP ports
Perform SYN DOS attack towards a server in a network
Attempt to perform an automated scan to discover vulnerabilities
Question
Which of the following compliance standards was introduced to provide a minimum degree of security to organizations who handle customer information such as debit card and credit card details daily?
PCIDSS
SOX
FISMA
GLB
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


