Question: A network administrator needs to ensure users' data are securely sent and received. Which network protocol should the administrator use? IPX IP IPSec NetBeui
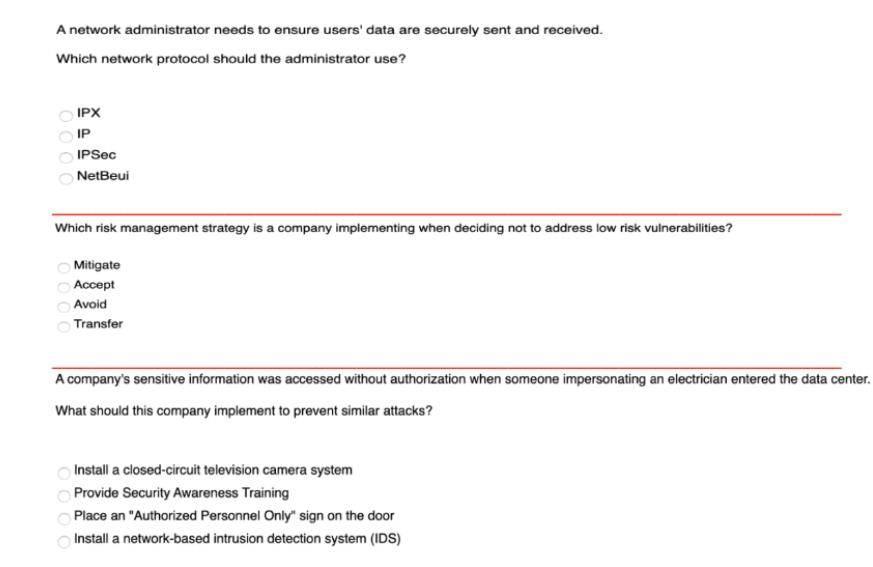
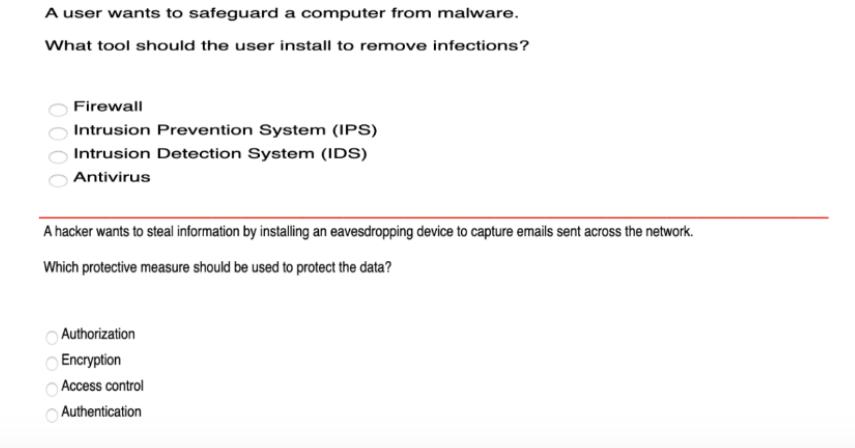
A network administrator needs to ensure users' data are securely sent and received. Which network protocol should the administrator use? IPX IP IPSec NetBeui Which risk management strategy is a company implementing when deciding not to address low risk vulnerabilities? Mitigate Accept Avoid Transfer 0000 A company's sensitive information was accessed without authorization when someone impersonating an electrician entered the data center. What should this company implement to prevent similar attacks? Install a closed-circuit television camera system Provide Security Awareness Training Place an "Authorized Personnel Only" sign on the door Install a network-based intrusion detection system (IDS) A user wants to safeguard a computer from malware. What tool should the user install to remove infections? 0000 Firewall Intrusion Prevention System (IPS) Intrusion Detection System (IDS) Antivirus A hacker wants to steal information by installing an eavesdropping device to capture emails sent across the network. Which protective measure should be used to protect the data? 0 000 Authorization Encryption Access control Authentication
Step by Step Solution
There are 3 Steps involved in it
The detailed answer for the above question is provided below 1 Network protocol IPSec This is the mo... View full answer

Get step-by-step solutions from verified subject matter experts


