Question
a) The following questions are related to operating system security: i. Define buffer overflow attack. ii. (2 marks) Explain how Address Space Layout Randomization
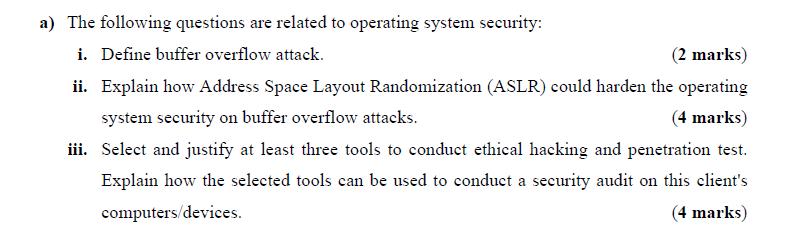
a) The following questions are related to operating system security: i. Define buffer overflow attack. ii. (2 marks) Explain how Address Space Layout Randomization (ASLR) could harden the operating system security on buffer overflow attacks. (4 marks) iii. Select and justify at least three tools to conduct ethical hacking and penetration test. Explain how the selected tools can be used to conduct a security audit on this client's computers/devices. (4 marks)
Step by Step Solution
There are 3 Steps involved in it
Step: 1
It seems youve provided a snapshot of an assignment or study question related to operating system security Lets address each part of the question step by step i A buffer overflow attack occurs when a ...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get StartedRecommended Textbook for
Income Tax Fundamentals 2013
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
31st Edition
1111972516, 978-1285586618, 1285586611, 978-1285613109, 978-1111972516
Students also viewed these Programming questions
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
View Answer in SolutionInn App



