Answered step by step
Verified Expert Solution
Question
1 Approved Answer
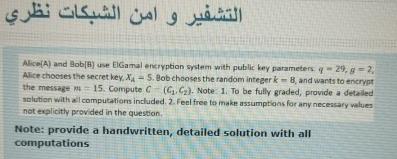
Alice ( A ) and Bob ( B ) use EiGamal enciyption sostem with public key parameters q = 2 9 , g = 2
Alice and BobB use EiGamal enciyption sostem with public key parameters Alice chooses the secret key, Bob chooses the random integer and wants to encrypt the message Compute Note: To be fully graded, provide a detaled aratution with a computations included. Feal free to make assumptions for any neceasary waluen not explicitly provided in the question.
Note: provide a handwritten, detailed solution with all computations
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started