Alice and Bob meet and agree to use the code to map characters to integers and to use the function C, a, b, c,,z}
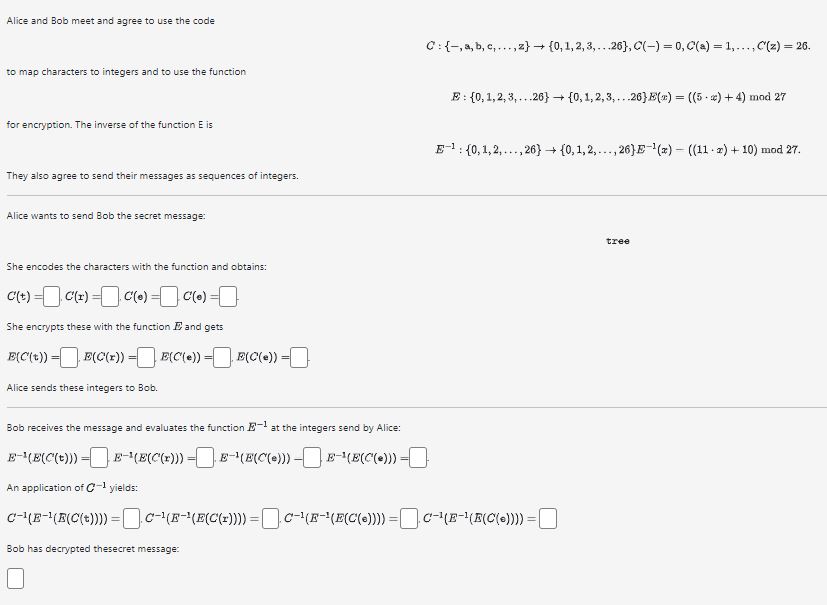
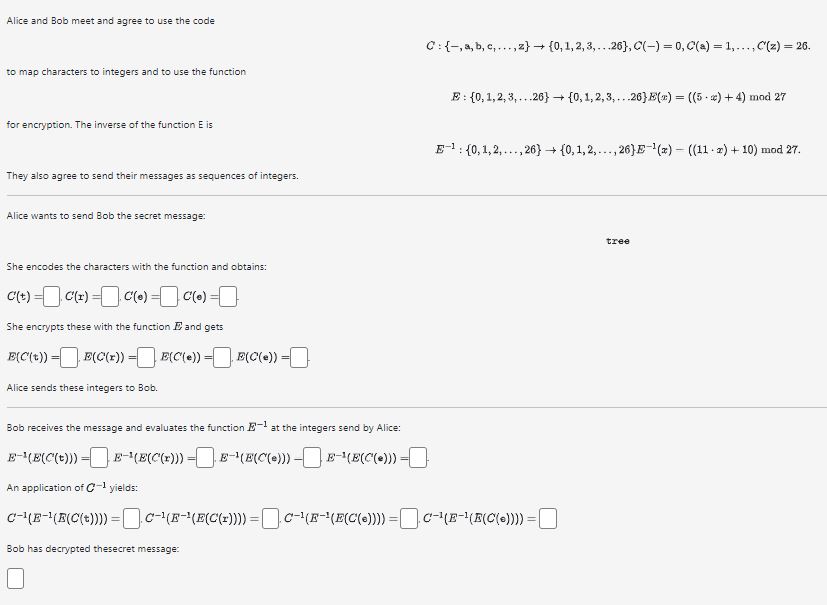
Alice and Bob meet and agree to use the code to map characters to integers and to use the function C, a, b, c,,z} {0, 1, 2, 3,...26), C(-) = 0, C(a) = 1,..., C'(z) = 26. + for encryption. The inverse of the function E is E: {0,1,2,3,...26} {0, 1, 2, 3,...26) E(x) = ((5 ) + 4) mod 27 They also agree to send their messages as sequences of integers. Alice wants to send Bob the secret message: - E{0,1,2,..., 26} {0, 1, 2,..., 26] E-1(x) ((11) + 10) mod 27. She encodes the characters with the function and obtains: C(+) C(r) = C(e) = C(0) = She encrypts these with the function E and gets E(C(t)) = E(C(x)) = E(C(e)) = E(C(e)) = Alice sends these integers to Bob. Bob receives the message and evaluates the function E- at the integers send by Alice: E-(E(C(t))) E(E(C'(x))) E(E(C(e))) E-(E(C(e))) = An application of C-1 yields: C(E(C(t)))) = C(F- (E(C(1)))) = C-(F-(E(C(6)))) = CE(E(C(=)))) = Bob has decrypted thesecret message: tree
Step by Step Solution
There are 3 Steps involved in it
Step: 1

See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started