Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Alice uses the GGH cryptosystem with private basis (58, 53, -68), V1 = and public basis v = (-110, -112, 35), v3 = (-10,
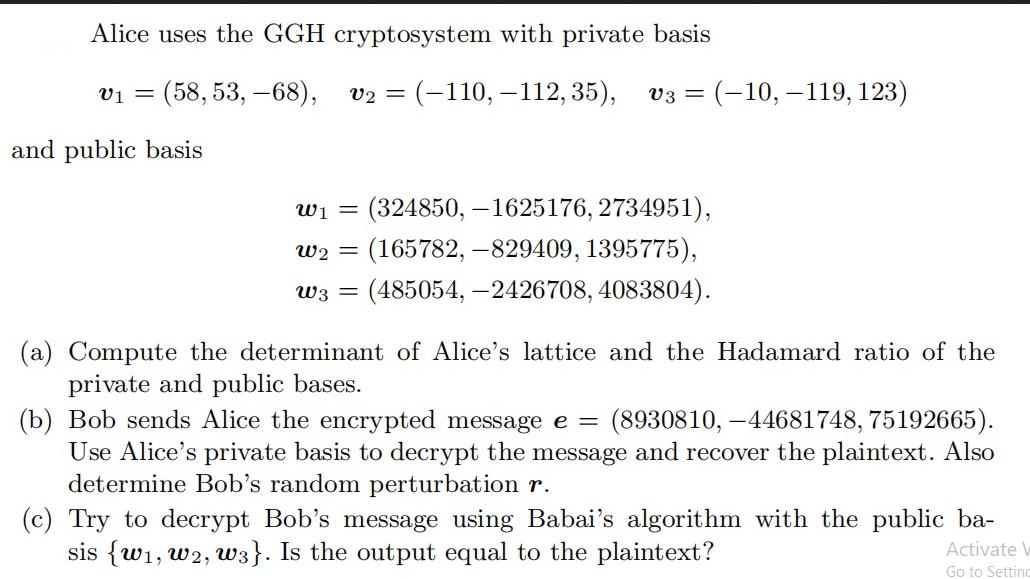
Alice uses the GGH cryptosystem with private basis (58, 53, -68), V1 = and public basis v = (-110, -112, 35), v3 = (-10, -119, 123) W = (324850, -1625176, 2734951), w2 = (165782, -829409, 1395775), W3 = (485054,-2426708, 4083804). (a) Compute the determinant of Alice's lattice and the Hadamard ratio of the private and public bases. (b) Bob sends Alice the encrypted message e = (8930810, -44681748, 75192665). Use Alice's private basis to decrypt the message and recover the plaintext. Also determine Bob's random perturbation r. (c) Try to decrypt Bob's message using Babai's algorithm with the public ba- sis {w, W2, W3}. Is the output equal to the plaintext? Activate Go to Setting
Step by Step Solution
There are 3 Steps involved in it
Step: 1
The image shows a question about the GoldreichGoldwasserHalevi GGH cryptosystem which is a latticebased cryptosystem The GGH cryptosystem uses a private basis that consists of short nearly orthogonal ...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


