Question: Alice wants to send an encrypted email to Bob using public key encryption. What process will Alice use? Alice sends the public key to Bob,
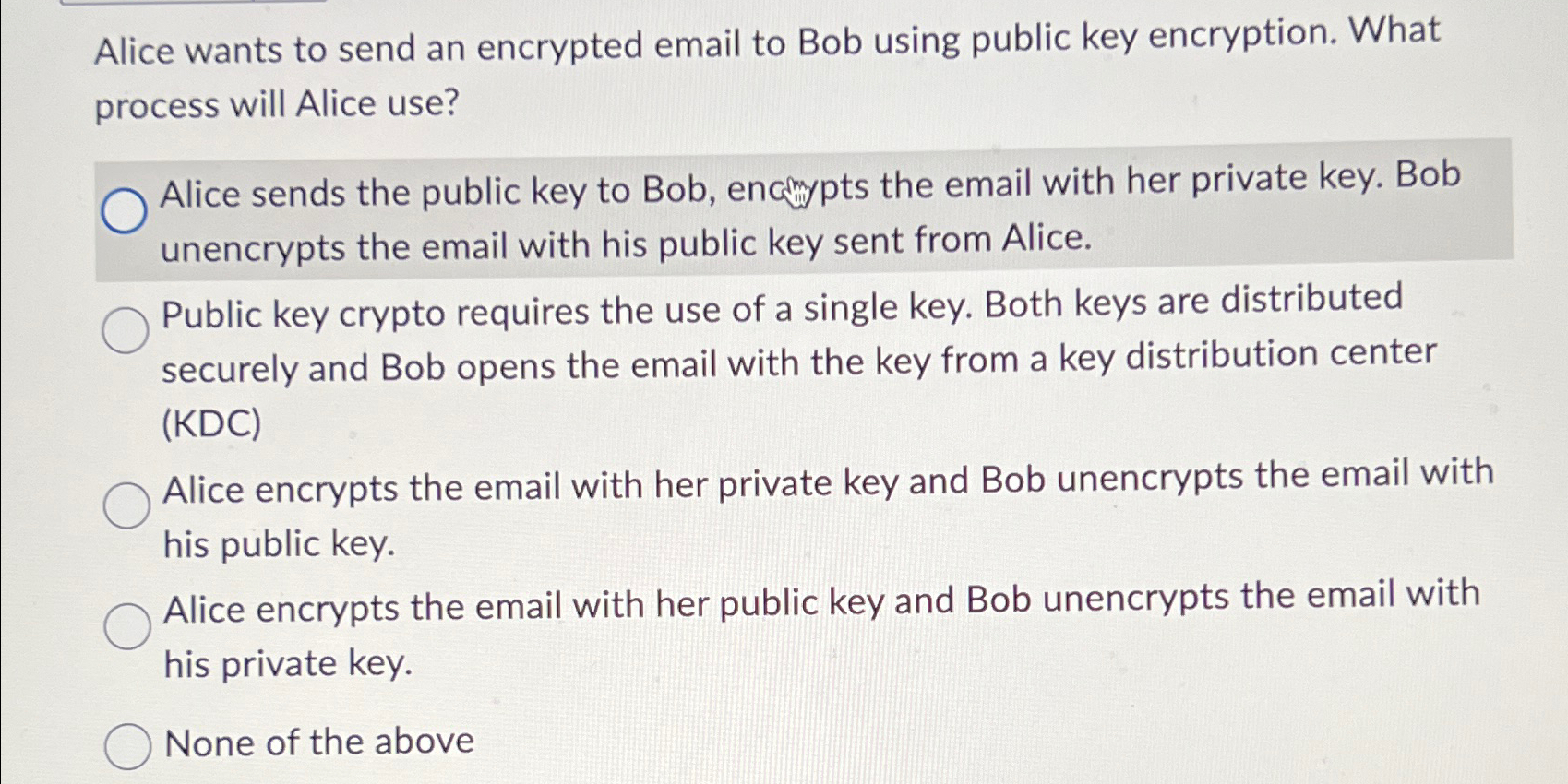
Alice wants to send an encrypted email to Bob using public key encryption. What process will Alice use?
Alice sends the public key to Bob, encmpts the email with her private key. Bob unencrypts the email with his public key sent from Alice.
Public key crypto requires the use of a single key. Both keys are distributed securely and Bob opens the email with the key from a key distribution center KDC
Alice encrypts the email with her private key and Bob unencrypts the email with his public key.
Alice encrypts the email with her public key and Bob unencrypts the email with his private key.
None of the above
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


