Answered step by step
Verified Expert Solution
Question
1 Approved Answer
An attacker John starts a software-based AP on his laptop. He then scans for the SSID of the AP at the coffee shop hotspot where
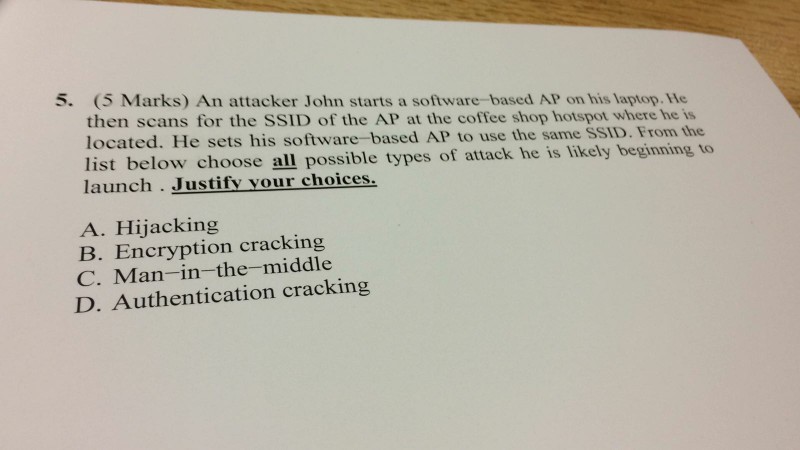
An attacker John starts a software-based AP on his laptop. He then scans for the SSID of the AP at the coffee shop hotspot where he is located. He sets his software-based AP to use the same SSID. From the list below choose all possible types of attack he is likely beginning to launch. Justify your choices. A. Hijacking B. Encryption cracking C. Man-in-the-middle D. Authentication cracking
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


