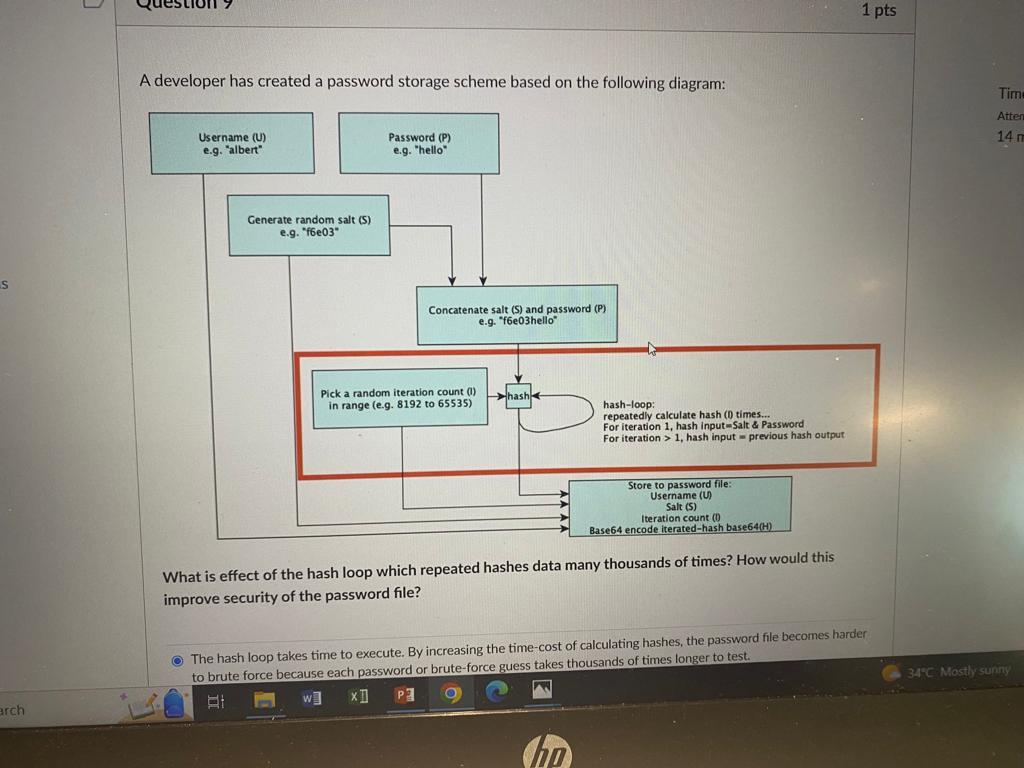
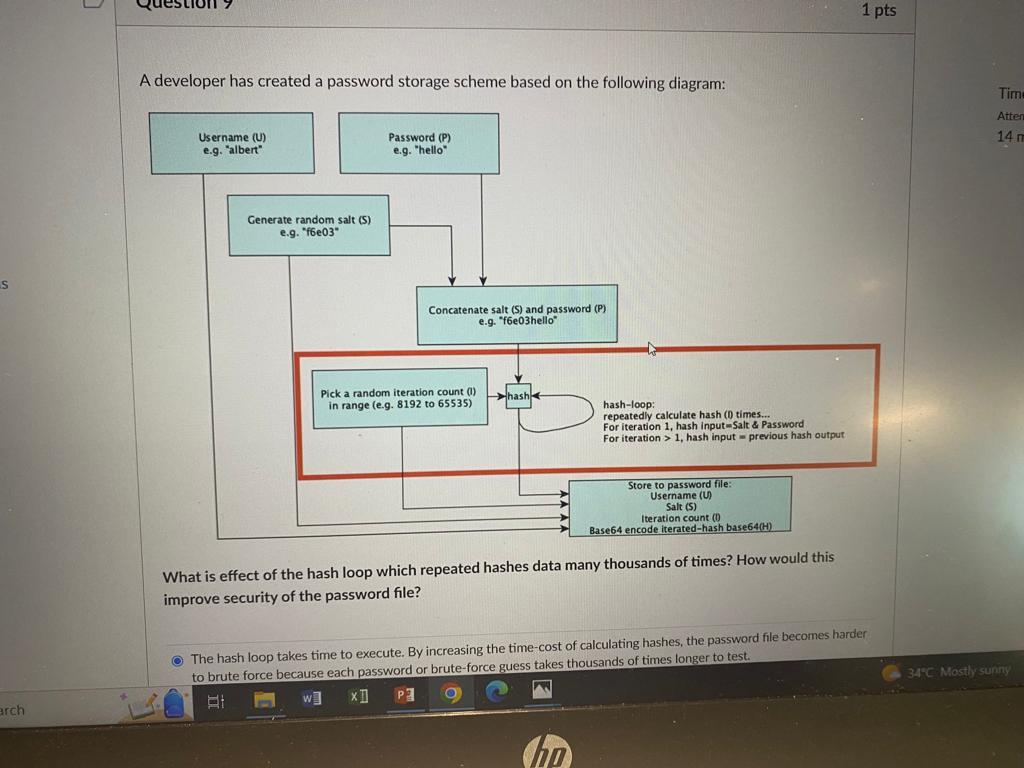
An insecure application can affect the security of an entire network by... Remote Procedure Calls (RPCS) are insecure because they allow applications to remotely trigger code on another computer. An RPC can send un-validated data to a remote computer and compromise the entire network. Sending un-solicited data to other servers or hosts on the network. Exposing a vulnerability that can be exploited to compromise further applications or systems. If an application is not protected by an application-firewall, any data that is sent to the application can be altered by an attacker. This can cause the data to be transmitted to other hosts on the same subnet and allow for other computers or devices to be compromised. Using shared libraries and APIs to make the application more compact and increase interaction between other applications. A developer has created a password storage scheme based on the following diagram: What is effect of the hash loop which repeated hashes data many thousands of times? How would this improve security of the password file? The hash loop takes time to execute. By increasing the time-cost of calculating hashes, the password file becomes harder What is effect of the hash loop which repeated hashes data many thousands of times? How would this improve security of the password file? The hash loop takes time to execute. By increasing the time-cost of calculating hashes, the password file becomes harder to brute force because each password or brute-force guess takes thousands of times longer to test. The hash includes the salt, which means rainbow attacks are impossible. The hash loop extends the password length, making the password much harder to guess. Extending the password length protects against dictionary attacks. The hash loop means the chances of guessing the password are reduced because an attacker doesn't know how many times the loop was run. The attacker needs to guess the password AND the iteration count. The hash loop improves the collision resistance of the hash function. Because all hash functions have a slim probability of a hash collision, repeated hashing reduces the likelihood. Improving collision resistance improves password security