Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Assume that you are the database security analyst for the TECHTEC LLC. The employees are mostly working in shift basis. When 50% of the
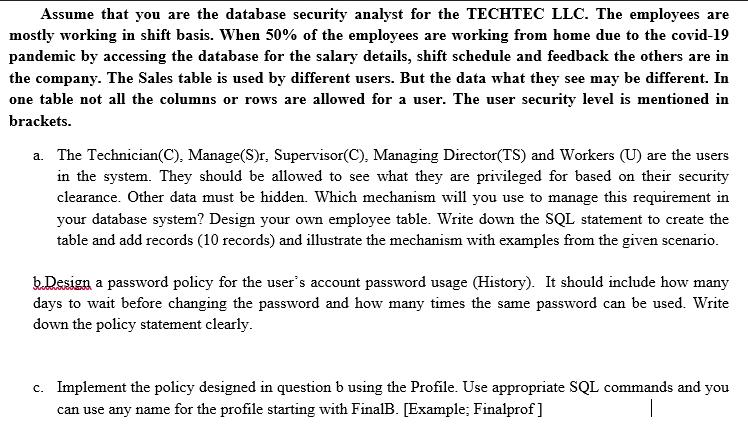
Assume that you are the database security analyst for the TECHTEC LLC. The employees are mostly working in shift basis. When 50% of the employees are working from home due to the covid-19 pandemic by accessing the database for the salary details, shift schedule and feedback the others are in the company. The Sales table is used by different users. But the data what they see may be different. In one table not all the columns or rows are allowed for a user. The user security level is mentioned in brackets. a. The Technician(C), Manage(S)r, Supervisor(C), Managing Director(TS) and Workers (U) are the users in the system. They should be allowed to see what they are privileged for based on their security clearance. Other data must be hidden. Which mechanism will you use to manage this requirement in your database system? Design your own employee table. Write down the SQL statement to create the table and add records (10 records) and illustrate the mechanism with examples from the given scenario. b.Design a password policy for the user's account password usage (History). It should include how many days to wait before changing the password and how many times the same password can be used. Write down the policy statement clearly. c. Implement the policy designed in question b using the Profile. Use appropriate SQL commands and you can use any name for the profile starting with FinalB. [Example; Finalprof]
Step by Step Solution
There are 3 Steps involved in it
Step: 1
a To manage the access control requirements in the database system we can use RoleBased Access Contr...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started