Question
(b) Draw the general framework a program cycle adheres to. (3 marks) (c) What types of CPU instructions are required to execute this high
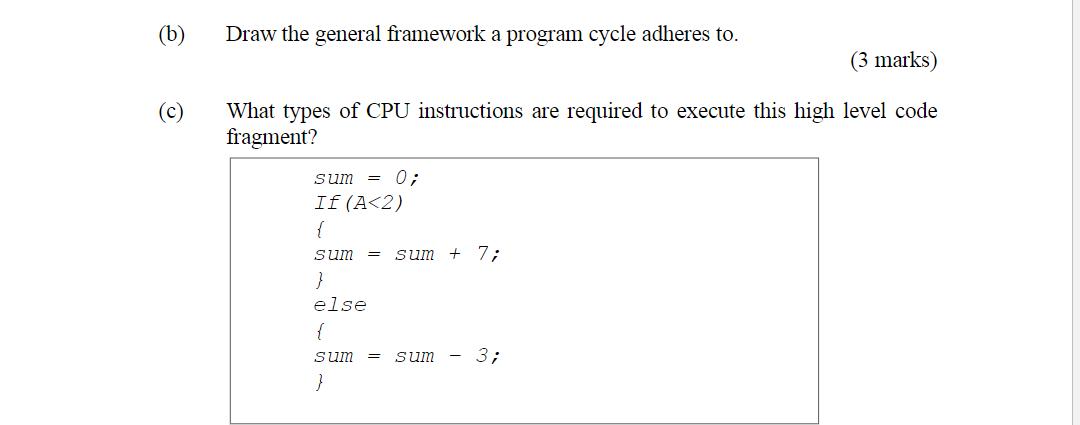
(b) Draw the general framework a program cycle adheres to. (3 marks) (c) What types of CPU instructions are required to execute this high level code fragment? sum = 0; If (A
Step by Step Solution
3.39 Rating (158 Votes )
There are 3 Steps involved in it
Step: 1
b General Framework of a Program Cycle Input Gather initial data or parameters Processing Execute th...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get StartedRecommended Textbook for
Computer Architecture A Quantitative Approach
Authors: John L. Hennessy, David A. Patterson
4th edition
123704901, 978-0123704900
Students also viewed these Programming questions
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
View Answer in SolutionInn App