Question
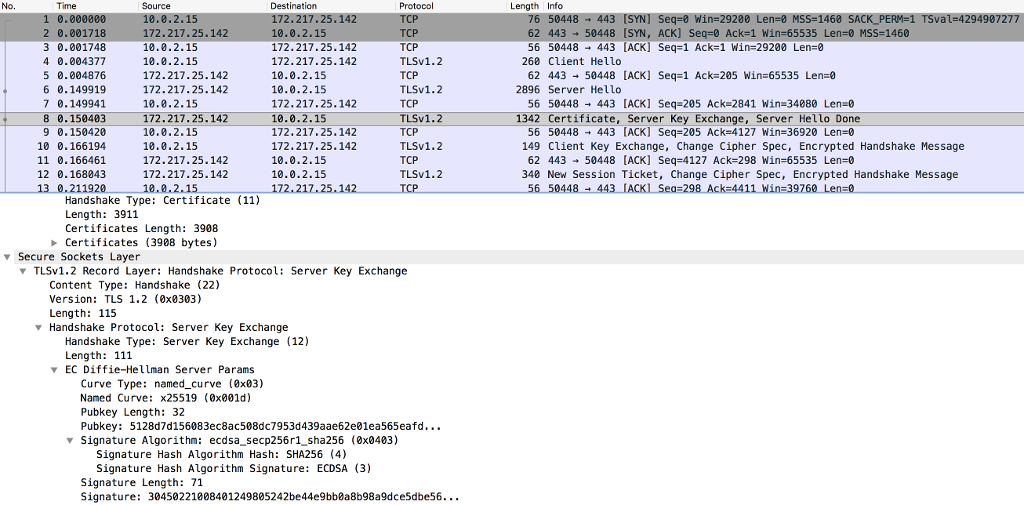
Below is TLS connection packet capture (first 15 packets), do they use RSA algorithm for key exchange? And why or why not? No. Time Source
Below is TLS connection packet capture (first 15 packets), do they use RSA algorithm for key exchange? And why or why not?
No. Time Source Destination Protocol Length Info 1 0.000000 10.0.2.15 172.217.25.142 TCP 76 50448 443 [SYN] Seq=0 Win=29200 Len=0 MSS=1460 SACK_PERM=1 TSval=4294907277 TSecr=0 WS=128
Frame 1: 76 bytes on wire (608 bits), 76 bytes captured (608 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 0, Len: 0
No. Time Source Destination Protocol Length Info 2 0.001718 172.217.25.142 10.0.2.15 TCP 62 443 50448 [SYN, ACK] Seq=0 Ack=1 Win=65535 Len=0 MSS=1460
Frame 2: 62 bytes on wire (496 bits), 62 bytes captured (496 bits) Linux cooked capture Internet Protocol Version 4, Src: 172.217.25.142, Dst: 10.0.2.15 Transmission Control Protocol, Src Port: 443, Dst Port: 50448, Seq: 0, Ack: 1, Len: 0 VSS-Monitoring ethernet trailer, Source Port: 0
No. Time Source Destination Protocol Length Info 3 0.001748 10.0.2.15 172.217.25.142 TCP 56 50448 443 [ACK] Seq=1 Ack=1 Win=29200 Len=0
Frame 3: 56 bytes on wire (448 bits), 56 bytes captured (448 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 1, Ack: 1, Len: 0
No. Time Source Destination Protocol Length Info 4 0.004377 10.0.2.15 172.217.25.142 TLSv1.2 260 Client Hello
Frame 4: 260 bytes on wire (2080 bits), 260 bytes captured (2080 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 1, Ack: 1, Len: 204 Secure Sockets Layer
No. Time Source Destination Protocol Length Info 5 0.004876 172.217.25.142 10.0.2.15 TCP 62 443 50448 [ACK] Seq=1 Ack=205 Win=65535 Len=0
Frame 5: 62 bytes on wire (496 bits), 62 bytes captured (496 bits) Linux cooked capture Internet Protocol Version 4, Src: 172.217.25.142, Dst: 10.0.2.15 Transmission Control Protocol, Src Port: 443, Dst Port: 50448, Seq: 1, Ack: 205, Len: 0 VSS-Monitoring ethernet trailer, Source Port: 0
No. Time Source Destination Protocol Length Info 6 0.149919 172.217.25.142 10.0.2.15 TLSv1.2 2896 Server Hello
Frame 6: 2896 bytes on wire (23168 bits), 2896 bytes captured (23168 bits) Linux cooked capture Internet Protocol Version 4, Src: 172.217.25.142, Dst: 10.0.2.15 Transmission Control Protocol, Src Port: 443, Dst Port: 50448, Seq: 1, Ack: 205, Len: 2840 Secure Sockets Layer
No. Time Source Destination Protocol Length Info 7 0.149941 10.0.2.15 172.217.25.142 TCP 56 50448 443 [ACK] Seq=205 Ack=2841 Win=34080 Len=0
Frame 7: 56 bytes on wire (448 bits), 56 bytes captured (448 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 205, Ack: 2841, Len: 0
No. Time Source Destination Protocol Length Info 8 0.150403 172.217.25.142 10.0.2.15 TLSv1.2 1342 Certificate, Server Key Exchange, Server Hello Done
Frame 8: 1342 bytes on wire (10736 bits), 1342 bytes captured (10736 bits) Linux cooked capture Internet Protocol Version 4, Src: 172.217.25.142, Dst: 10.0.2.15 Transmission Control Protocol, Src Port: 443, Dst Port: 50448, Seq: 2841, Ack: 205, Len: 1286 [2 Reassembled TCP Segments (3920 bytes): #6(2763), #8(1157)] Secure Sockets Layer Secure Sockets Layer
No. Time Source Destination Protocol Length Info 9 0.150420 10.0.2.15 172.217.25.142 TCP 56 50448 443 [ACK] Seq=205 Ack=4127 Win=36920 Len=0
Frame 9: 56 bytes on wire (448 bits), 56 bytes captured (448 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 205, Ack: 4127, Len: 0
No. Time Source Destination Protocol Length Info 10 0.166194 10.0.2.15 172.217.25.142 TLSv1.2 149 Client Key Exchange, Change Cipher Spec, Encrypted Handshake Message
Frame 10: 149 bytes on wire (1192 bits), 149 bytes captured (1192 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 205, Ack: 4127, Len: 93 Secure Sockets Layer
No. Time Source Destination Protocol Length Info 11 0.166461 172.217.25.142 10.0.2.15 TCP 62 443 50448 [ACK] Seq=4127 Ack=298 Win=65535 Len=0
Frame 11: 62 bytes on wire (496 bits), 62 bytes captured (496 bits) Linux cooked capture Internet Protocol Version 4, Src: 172.217.25.142, Dst: 10.0.2.15 Transmission Control Protocol, Src Port: 443, Dst Port: 50448, Seq: 4127, Ack: 298, Len: 0 VSS-Monitoring ethernet trailer, Source Port: 0
No. Time Source Destination Protocol Length Info 12 0.168043 172.217.25.142 10.0.2.15 TLSv1.2 340 New Session Ticket, Change Cipher Spec, Encrypted Handshake Message
Frame 12: 340 bytes on wire (2720 bits), 340 bytes captured (2720 bits) Linux cooked capture Internet Protocol Version 4, Src: 172.217.25.142, Dst: 10.0.2.15 Transmission Control Protocol, Src Port: 443, Dst Port: 50448, Seq: 4127, Ack: 298, Len: 284 Secure Sockets Layer
No. Time Source Destination Protocol Length Info 13 0.211920 10.0.2.15 172.217.25.142 TCP 56 50448 443 [ACK] Seq=298 Ack=4411 Win=39760 Len=0
Frame 13: 56 bytes on wire (448 bits), 56 bytes captured (448 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 298, Ack: 4411, Len: 0
No. Time Source Destination Protocol Length Info 14 0.641843 10.0.2.15 172.217.25.142 TLSv1.2 219 Application Data
Frame 14: 219 bytes on wire (1752 bits), 219 bytes captured (1752 bits) Linux cooked capture Internet Protocol Version 4, Src: 10.0.2.15, Dst: 172.217.25.142 Transmission Control Protocol, Src Port: 50448, Dst Port: 443, Seq: 298, Ack: 4411, Len: 163 Secure Sockets Layer
No. Time Source Destination Protocol Length Info 15 0.642078 172.217.25.142 10.0.2.15 TCP 62 443 50448 [ACK] Seq=4411 Ack=461 Win=65535 Len=0
Time Source 10.0.2.15 172.217.25.142 10.0.2.15 10.0.2.15 172.217.25.142 172.217.25.142 10.0.2.15 172.217.25.142 10.0.2.15 10.0.2.15 172.217.25.142 172.217.25.142 Destination 172.217.25.14 10.0.2.15 172.217.25.142 172.217.25.142 10.0.2.15 10.0.2.15 172.217.25.142 No. Protocol Length Info [SYN] [SYN, 0.000 2 0.001718 3 0.001748 4 0.004377 5 0.004876 6 0.149919 7 0.149941 8 0.150403 9 0.150420 10 0.166194 11 0.166461 12 0.168843 448 443 50448 Seqs1 win-29200 Seq=0 Lens! MSS-1460 SACK-PERM-1 MSS=1460 TSval-4294907277 62 443 ACK] Ack=| Win-65535 Len=0 TCP TCP TLSv1.2 TCP TLSv1.2 TCP 56 50448 443 [ACK] Seqs1 Ack=1 Win-29200 Len=0 62 44350448 [ACK] Seq-1 Ack-205 Win 65535 Len 0 56 50448 443 [ACK] Seq-205 Ack-2841 Win-34080 Len=0 56 50448 443 [ACK] Seq-205 Ack-4127 Win-36920 Len-0 62 443 50448 [ACK] Seq-4127 Ack-298 Win-65535 Len-0 260 Client Hello 2896 Server Hello TLSv1.2-1342 Certificate, Server Key Exchange, Server Hello Done 172.217.25.142 172.217.25.142 10.0.2.15 10.0.2.15 TCP TLSv1.2 TCP TLSv1.2 149 Client Key Exchange, Change Cipher Spec, Encrypted Handshake Message 340 New Session Ticket, Change Cipher Spec, Encrypted Handshake Message Handshake Type: Certificate (11) Length: 3911 Certificates Length: 3908 Certificates (3908 bytes) Secure Sockets Layer TLSv1.2 Record Layer: Handshake Protocol: Server Key Exchange Content Type: Handshake (22) Version: TLS 1.2 (0x0303) Length: 115 Handshake Protocol: Server Key Exchange Handshake Type: Server Key Exchange (12) Length: 111 EC Diffie-Hellman Server Params Curve Type: named curve 8x03) Named Curve: x25519 (0x001d) Pubkey Length: 32 Pubkey: 5128d7d156083ec8ac508dc7953d439aae62e01ea565eafd... Y Signature Algorithm: ecdsa_secp256r1 sha256 (0x0403) Signature Hash Algorithm Hash: SHA256 (4) Signature Hash Algorithm Signature: ECDSA (3) Signature Length:71 Signature: 30450221808401249805242be44e9bb8a8b98a9dce5dbe56.. Time Source 10.0.2.15 172.217.25.142 10.0.2.15 10.0.2.15 172.217.25.142 172.217.25.142 10.0.2.15 172.217.25.142 10.0.2.15 10.0.2.15 172.217.25.142 172.217.25.142 Destination 172.217.25.14 10.0.2.15 172.217.25.142 172.217.25.142 10.0.2.15 10.0.2.15 172.217.25.142 No. Protocol Length Info [SYN] [SYN, 0.000 2 0.001718 3 0.001748 4 0.004377 5 0.004876 6 0.149919 7 0.149941 8 0.150403 9 0.150420 10 0.166194 11 0.166461 12 0.168843 448 443 50448 Seqs1 win-29200 Seq=0 Lens! MSS-1460 SACK-PERM-1 MSS=1460 TSval-4294907277 62 443 ACK] Ack=| Win-65535 Len=0 TCP TCP TLSv1.2 TCP TLSv1.2 TCP 56 50448 443 [ACK] Seqs1 Ack=1 Win-29200 Len=0 62 44350448 [ACK] Seq-1 Ack-205 Win 65535 Len 0 56 50448 443 [ACK] Seq-205 Ack-2841 Win-34080 Len=0 56 50448 443 [ACK] Seq-205 Ack-4127 Win-36920 Len-0 62 443 50448 [ACK] Seq-4127 Ack-298 Win-65535 Len-0 260 Client Hello 2896 Server Hello TLSv1.2-1342 Certificate, Server Key Exchange, Server Hello Done 172.217.25.142 172.217.25.142 10.0.2.15 10.0.2.15 TCP TLSv1.2 TCP TLSv1.2 149 Client Key Exchange, Change Cipher Spec, Encrypted Handshake Message 340 New Session Ticket, Change Cipher Spec, Encrypted Handshake Message Handshake Type: Certificate (11) Length: 3911 Certificates Length: 3908 Certificates (3908 bytes) Secure Sockets Layer TLSv1.2 Record Layer: Handshake Protocol: Server Key Exchange Content Type: Handshake (22) Version: TLS 1.2 (0x0303) Length: 115 Handshake Protocol: Server Key Exchange Handshake Type: Server Key Exchange (12) Length: 111 EC Diffie-Hellman Server Params Curve Type: named curve 8x03) Named Curve: x25519 (0x001d) Pubkey Length: 32 Pubkey: 5128d7d156083ec8ac508dc7953d439aae62e01ea565eafd... Y Signature Algorithm: ecdsa_secp256r1 sha256 (0x0403) Signature Hash Algorithm Hash: SHA256 (4) Signature Hash Algorithm Signature: ECDSA (3) Signature Length:71 Signature: 30450221808401249805242be44e9bb8a8b98a9dce5dbe56Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started